Refer to the exhibit.
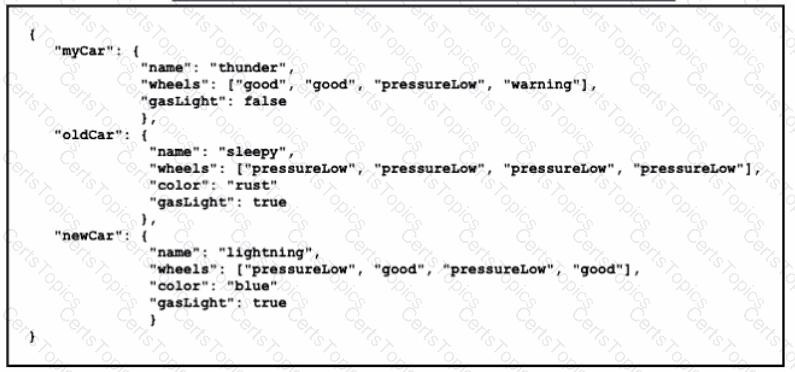
In which structure does the word " warning " directly reside?
Which authentication method requires the user to provide a physical attribute to authenticate successfully?
In which way does a spine-and-leaf architecture allow for scalability in a network when additional access ports are required?
A new DHCP server has been deployed in a corporate environment with lease time set to eight hours. Which CMD command on a Windows-based device allows the engineer to verify the DHCP lease expiration?