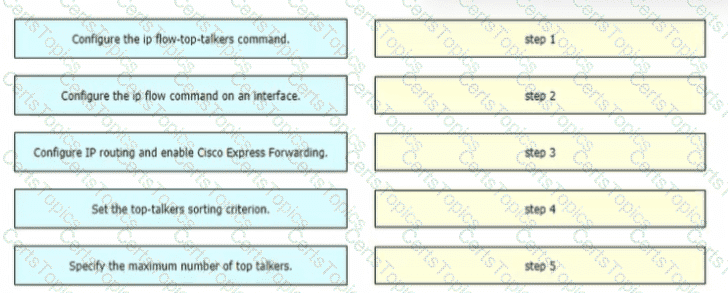
A network engineer is configuring NetFlow top talkers on a Cisco router Drag and drop the steps in the process from the left into the sequence on the right
In an IaaS cloud services model, which security function is the provider responsible for managing?
For a given policy in Cisco Umbrella, how should a customer block website based on a custom list?
Which two preventive measures are used to control cross-site scripting? (Choose two)