An engineer adds a custom detection policy to a Cisco AMP deployment and encounters issues with the
configuration. The simple detection mechanism is configured, but the dashboard indicates that the hash is not 64 characters and is non-zero. What is the issue?
An organization has two systems in their DMZ that have an unencrypted link between them for communication.
The organization does not have a defined password policy and uses several default accounts on the systems.
The application used on those systems also have not gone through stringent code reviews. Which vulnerability
would help an attacker brute force their way into the systems?
For which two conditions can an endpoint be checked using ISE posture assessment? (Choose two)
Refer to the exhibit.
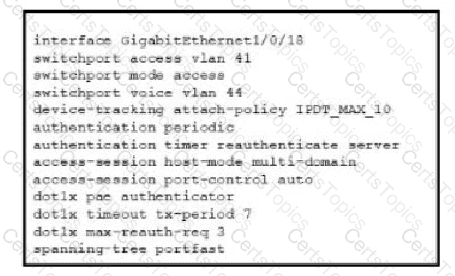
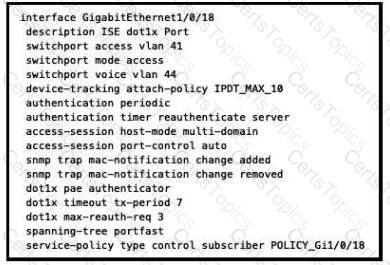
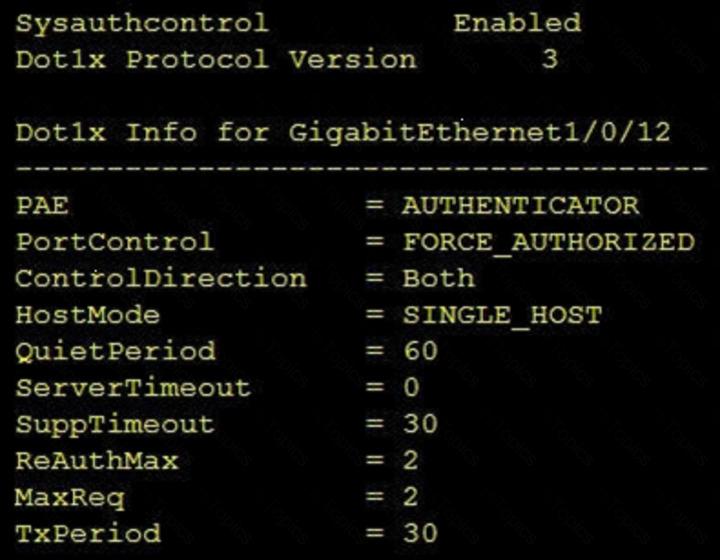
Refer to the exhibit. A Cisco ISE administrator adds a new switch to an 802.1X deployment and has difficulty with some endpoints gaining access.
Most PCs and IP phones can connect and authenticate using their machine certificate credentials. However printer and video cameras cannot base d on the interface configuration provided, what must be to get these devices on to the network using Cisco ISE for authentication and authorization while maintaining security controls?
Which feature must be configured before implementing NetFlow on a router?
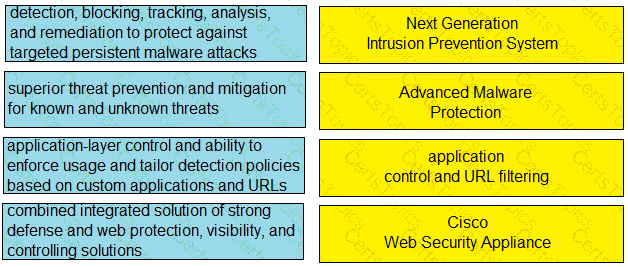
Drag and drop the capabilities from the left onto the correct technologies on the right.
Which CLI command is used to enable URL filtering support for shortened URLs on the Cisco Secure Email Gateway?
Which information is required when adding a device to Firepower Management Center?
Which ASA deployment mode can provide separation of management on a shared appliance?
Which network monitoring solution uses streams and pushes operational data to provide a near real-time view
of activity?
A network engineer is configuring DMVPN and entered the crypto isakmp key cisc0380739941 address 0.0.0.0 command on hostA. The tunnel is not being established to hostB. What action is needed to authenticate the VPN?
What is a difference between GRE over IPsec and IPsec with crypto map?
When configuring ISAKMP for IKEv1 Phase1 on a Cisco IOS router, an administrator needs to input the
command crypto isakmp key cisco address 0.0.0.0. The administrator is not sure what the IP addressing in this command issued for. What would be the effect of changing the IP address from 0.0.0.0 to 1.2.3.4?
Which two descriptions of AES encryption are true? (Choose two)
An organization is trying to improve their Defense in Depth by blocking malicious destinations prior to a
connection being established. The solution must be able to block certain applications from being used within the network. Which product should be used to accomplish this goal?
Which encryption algorithm provides highly secure VPN communications?
With which components does a southbound API within a software-defined network architecture communicate?
An organization has a Cisco ESA set up with policies and would like to customize the action assigned for
violations. The organization wants a copy of the message to be delivered with a message added to flag it as a
DLP violation. Which actions must be performed in order to provide this capability?
Which form of attack is launched using botnets?
When NetFlow is applied to an interface, which component creates the flow monitor cache that is used
to collect traffic based on the key and nonkey fields in the configured record?
Which CLI command is used to enable URL filtering support for shortened URLs on the Cisco ESA?
Which security solution uses NetFlow to provide visibility across the network, data center, branch
offices, and cloud?
Which type of dashboard does Cisco Catalyst Center provide for complete control of the network?
With regard to RFC 5176 compliance, how many IETF attributes are supported by the RADIUS CoA feature?
Which statement about the configuration of Cisco ASA NetFlow v9 Secure Event Logging is true?
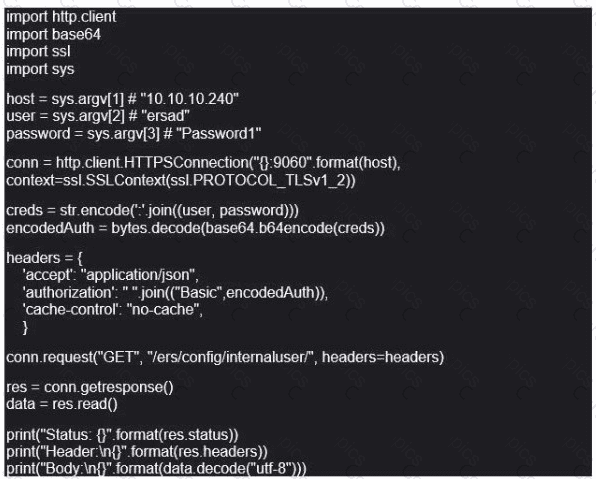
Refer to the exhibit. What does this Python script accomplish?
Refer to the exhibit.
What is the function of the Python script code snippet for the Cisco ASA REST API?
Which algorithm is an NGE hash function?
Refer to the exhibit.
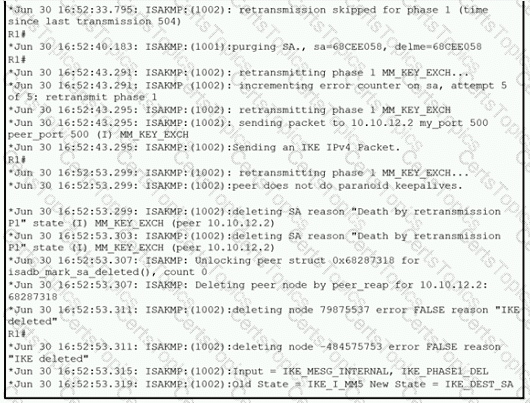
A network administrator configured a site-to-site VPN tunnel between two Cisco IOS routers, and hosts are unable to communicate between two sites of VPN. The network administrator runs the debug crypto isakmp sa command to track VPN status. What is the problem according to this command output?
Which attack is preventable by Cisco ESA but not by the Cisco WSA?
Which statement about IOS zone-based firewalls is true?
An organization is using Cisco Firepower and Cisco Meraki MX for network security and needs to centrally
manage cloud policies across these platforms. Which software should be used to accomplish this goal?
Which Cisco Umbrella package supports selective proxy for Inspection of traffic from risky domains?
Cisco SensorBase gaihers threat information from a variety of Cisco products and services and performs analytics to find patterns on threats Which term describes this process?
An administrator is trying to determine which applications are being used in the network but does not want the
network devices to send metadata to Cisco Firepower. Which feature should be used to accomplish this?
In which cloud services model is the tenant responsible for virtual machine OS patching?
A switch with Dynamic ARP Inspection enabled has received a spoofed ARP response on a trusted interface.
How does the switch behave in this situation?
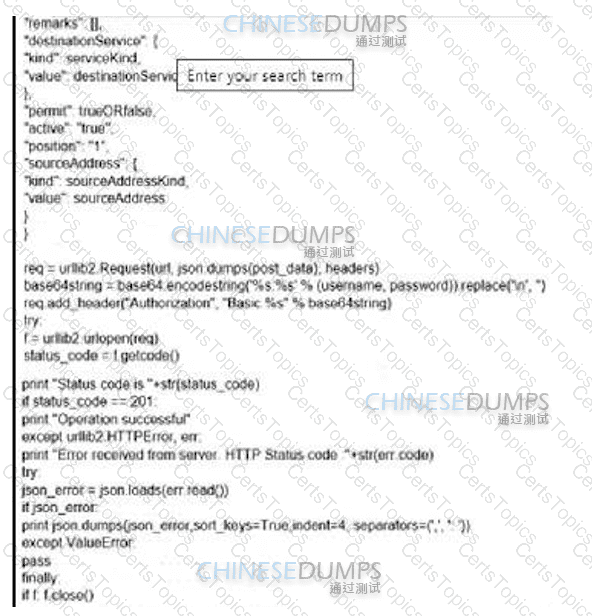
Refer to the exhibit.
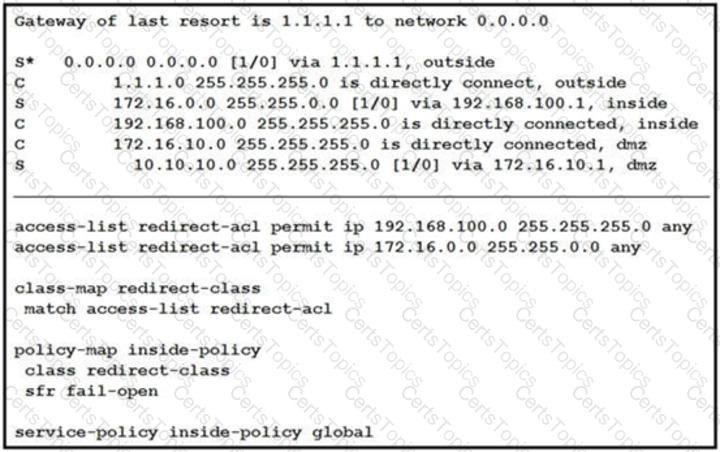
What is a result of the configuration?
Refer to the exhibit.
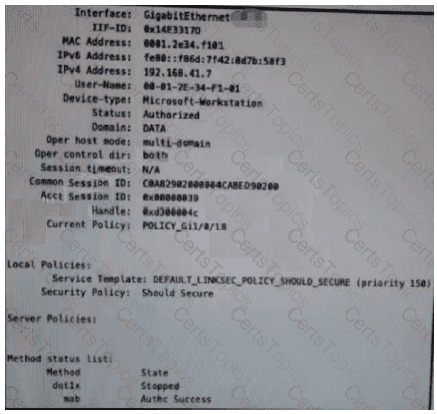
Which configuration item makes it possible to have the AAA session on the network?
What is a benefit of using Cisco Tetration?
How does Cisco Stealthwatch Cloud provide security for cloud environments?
A Cisco ESA network administrator has been tasked to use a newly installed service to help create policy based on the reputation verdict. During testing, it is discovered that the Cisco ESA is not dropping files that have an undetermined verdict. What is causing this issue?
Which policy does a Cisco Secure Web Appliance use to block or monitor URL requests based on the reputation score?
Which VPN provides scalability for organizations with many remote sites?
Which two Cisco ISE components must be configured for BYOD? (Choose two.)
Which feature is used in a push model to allow for session identification, host reauthentication, and session termination?
While using Cisco Secure Firewall's Security Intelligence policies, which two criteria is blocking based upon? (Choose two.)
For which type of attack is multifactor authentication an effective deterrent?
Refer to the exhibit.
What will occur when this device tries to connect to the port?
An engineer has been tasked with implementing a solution that can be leveraged for securing the cloud users,
data, and applications. There is a requirement to use the Cisco cloud native CASB and cloud cybersecurity
platform. What should be used to meet these requirements?
Which two request of REST API are valid on the Cisco ASA Platform? (Choose two)
What is a benefit of performing device compliance?
Which attack is commonly associated with C and C++ programming languages?
What is the difference between deceptive phishing and spear phishing?
Why is it important to have a patching strategy for endpoints?
A malicious user gained network access by spoofing printer connections that were authorized using MAB on
four different switch ports at the same time. What two catalyst switch security features will prevent further
violations? (Choose two)
Which type of dashboard does Cisco DNA Center provide for complete control of the network?
How does DNS Tunneling exfiltrate data?
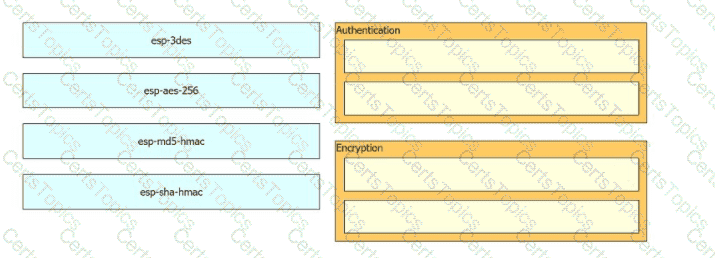
Drag and drop the cryptographic algorithms for IPsec from the left onto the cryptographic processes on the right.
Which term describes when the Cisco Firepower downloads threat intelligence updates from Cisco Talos?
A network engineer has entered the snmp-server user andy myv3 auth sha cisco priv aes 256
cisc0380739941 command and needs to send SNMP information to a host at 10.255.254.1. Which command achieves this goal?
Which two products are used to forecast capacity needs accurately in real time? (Choose two.)
What is the concept of Cl/CD pipelining?
Which technology must De used to Implement secure VPN connectivity among company branches over a private IP cloud with any-to-any scalable connectivity?
Which cryptographic process provides origin confidentiality, integrity, and origin authentication for packets?
An organization wants to improve its cybersecurity processes and to add intelligence to its data The organization wants to utilize the most current intelligence data for URL filtering, reputations, and vulnerability information that can be integrated with the Cisco FTD and Cisco WSA What must be done to accomplish these objectives?
What is a functional difference between Cisco AMP for Endpoints and Cisco Umbrella Roaming Client?
What are two benefits of using an MDM solution? (Choose two.)
An administrator has been tasked with configuring the Cisco Secure Email Gateway to ensure there are no viruses before quarantined emails are delivered. In addition, delivery of mail from known bad mail servers must be prevented. Which two actions must be taken in order to meet these requirements? (Choose two.)
Which service allows a user export application usage and performance statistics with Cisco Application Visibility
and control?
What is the most commonly used protocol for network telemetry?
Which function is included when Cisco AMP is added to web security?
Refer to the exhibit.
Which command was used to display this output?
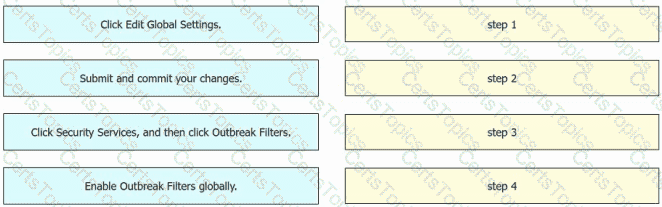
An engineer must enable Outbreak Filters globally on an AsyncOS for Cisco Secure Email Gateway to protect the network from large-scale malware attacks. Drag and drop the steps from the left into the sequence on the right to complete the configuration.
A web hosting company must upgrade its older, unsupported on-premises servers. The company wants a cloud solution in which the cloud provider is responsible for:
Server patching
Application maintenance
Data center security
Disaster recovery
Which type of cloud meets the requirements?
Which two prevention techniques are used to mitigate SQL injection attacks? (Choose two)
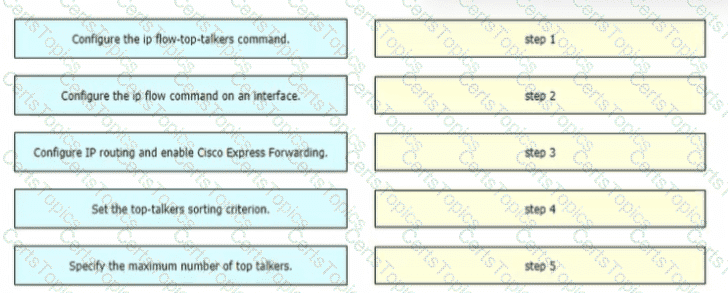
A network engineer is configuring NetFlow top talkers on a Cisco router Drag and drop the steps in the process from the left into the sequence on the right
In an IaaS cloud services model, which security function is the provider responsible for managing?
For a given policy in Cisco Umbrella, how should a customer block website based on a custom list?
Which two preventive measures are used to control cross-site scripting? (Choose two)
What does Cisco ISE use to collect endpoint attributes that are used in profiling?
An engineer notices traffic interruption on the network. Upon further investigation, it is learned that broadcast
packets have been flooding the network. What must be configured, based on a predefined threshold, to
address this issue?
Which Cisco security solution secures public, private, hybrid, and community clouds?
Which technology provides a combination of endpoint protection endpoint detection, and response?
Which Cisco AMP file disposition valid?
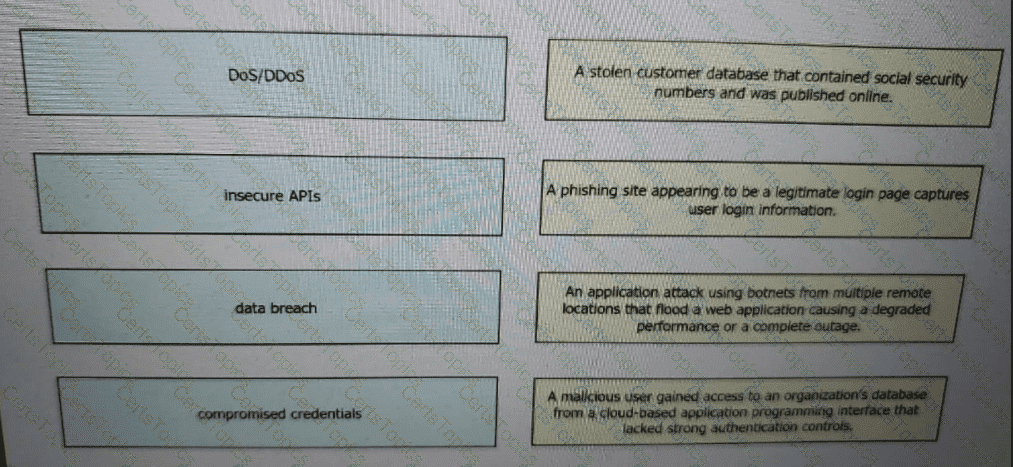
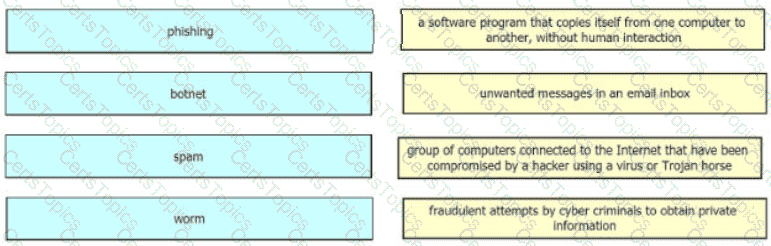
Drag and drop the threats from the left onto examples of that threat on the right
Which attribute has the ability to change during the RADIUS CoA?
Which two methods are available in Cisco Secure Web Appliance to process client requests when configured in Transparent mode? (Choose two.)
What is the difference between deceptive phishing and spear phishing?
How is DNS tunneling used to exfiltrate data out of a corporate network?
Which statement describes a serverless application?
A small organization needs to reduce the VPN bandwidth load on their headend Cisco ASA in order to
ensure that bandwidth is available for VPN users needing access to corporate resources on the10.0.0.0/24 local HQ network. How is this accomplished without adding additional devices to the
network?
What are two Trojan malware attacks? (Choose two)
A company has 5000 Windows users on its campus. Which two precautions should IT take to prevent WannaCry ransomware from spreading to all clients? (Choose two.)
Which risk is created when using an Internet browser to access cloud-based service?
Which VPN technology can support a multivendor environment and secure traffic between sites?
When using Cisco AMP for Networks which feature copies a file to the Cisco AMP cloud for analysis?
Which direction do attackers encode data in DNS requests during exfiltration using DNS tunneling?
An administrator is establishing a new site-to-site VPN connection on a Cisco IOS router. The organization
needs to ensure that the ISAKMP key on the hub is used only for terminating traffic from the IP address of
172.19.20.24. Which command on the hub will allow the administrator to accomplish this?
Based on the NIST 800-145 guide, which cloud architecture is provisioned for exclusive use by a specific group of consumers from different organizations and may be owned, managed, and operated by one or more of those organizations?
Which deployment model is the most secure when considering risks to cloud adoption?
Which two tasks allow NetFlow on a Cisco ASA 5500 Series firewall? (Choose two)
An organization uses Cisco FMC to centrally manage multiple Cisco FTD devices The default management port conflicts with other communications on the network and must be changed What must be done to ensure that all devices can communicate together?
Which Cisco AMP feature allows an engineer to look back to trace past activities, such as file and process
activity on an endpoint?
An organization uses Cisco FMC to centrally manage multiple Cisco FTD devices. The default management
port conflicts with other communications on the network and must be changed. What must be done to ensure
that all devices can communicate together?
What is a benefit of using Cisco FMC over Cisco ASDM?
Which feature requires that network telemetry be enabled?
What must be enabled to secure SaaS-based applications?
What are two advantages of using Cisco Any connect over DMVPN? (Choose two)
Which two types of connectors are used to generate telemetry data from IPFIX records in a Cisco Secure Workload implementation? (Choose two.)
Which command is used to log all events to a destination colector 209.165.201.107?
Which action controls the amount of URI text that is stored in Cisco WSA logs files?
A network engineer is tasked with configuring a Cisco ISE server to implement external authentication against Active Directory. What must be considered about the authentication requirements? (Choose two.)
A network administrator is configuring a rule in an access control policy to block certain URLs and selects the “Chat and Instant Messaging” category. Which reputation score should be selected to accomplish this goal?
What is a functional difference between a Cisco ASA and a Cisco IOS router with Zone-based policy firewall?
What are two workload security models? (Choose two.)
Why would a user choose an on-premises ESA versus the CES solution?
Which attack type attempts to shut down a machine or network so that users are not able to access it?
What is the purpose of the Trusted Automated exchange cyber threat intelligence industry standard?
A network administrator is configuring a switch to use Cisco ISE for 802.1X. An endpoint is failing
authentication and is unable to access the network. Where should the administrator begin troubleshooting to verify the authentication details?
Which VPN technology supports a multivendor environment and secure traffic between sites?
Which Dos attack uses fragmented packets to crash a target machine?
What are two functions of secret key cryptography? (Choose two)
Which security solution is used for posture assessment of the endpoints in a BYOD solution?
An engineer wants to generate NetFlow records on traffic traversing the Cisco ASA. Which Cisco ASA
command must be used?
Which two are valid suppression types on a Cisco Next Generation Intrusion Prevention System? (Choose two)
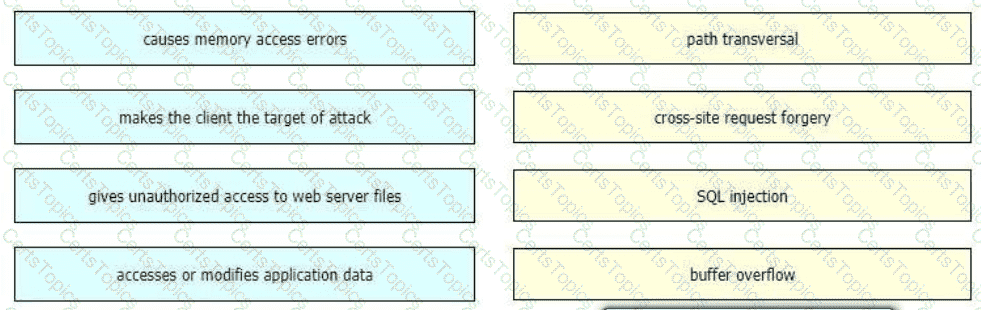
Drag and drop the exploits from the left onto the type of security vulnerability on the right.
An engineer needs to configure an access control policy rule to always send traffic for inspection without
using the default action. Which action should be configured for this rule?
Which Cisco ASA Platform mode disables the threat detection features except for Advanced Threat Statistics?
A network engineer entered the snmp-server user asmith myv7 auth sha cisco priv aes 256
cisc0xxxxxxxxx command and needs to send SNMP information to a host at 10.255.255.1. Which
command achieves this goal?
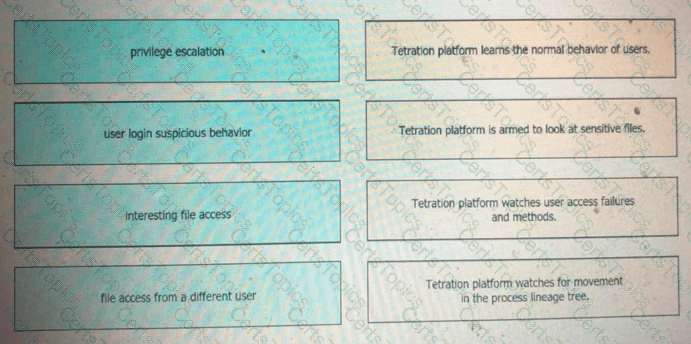
Drag and drop the suspicious patterns for the Cisco Tetration platform from the left onto the correct definitions on the right.
What are two things to consider when using PAC files with the Cisco WSA? (Choose two.)
Which two cryptographic algorithms are used with IPsec? (Choose two)
Which action configures the IEEE 802.1X Flexible Authentication feature to support Layer 3 authentication mechanisms?
In which two ways does a system administrator send web traffic transparently to the Web Security Appliance?
(Choose two)
An engineer enabled SSL decryption for Cisco Umbrella intelligent proxy and needs to ensure that traffic is inspected without alerting end-users.
An administrator configures a Cisco WSA to receive redirected traffic over ports 80 and 443. The organization requires that a network device with specific WSA integration capabilities be configured to send the traffic to the WSA to proxy the requests and increase visibility, while making this invisible to the users. What must be done on the Cisco WSA to support these requirements?
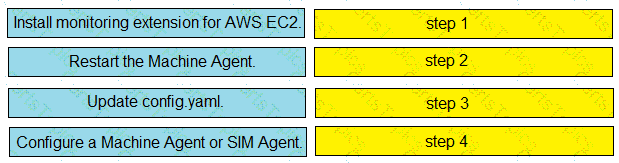
Drag and drop the steps from the left into the correct order on the right to enable AppDynamics to monitor an EC2 instance in Amazon Web Services.
When planning a VPN deployment, for which reason does an engineer opt for an active/active FlexVPN
configuration as opposed to DMVPN?
What is the purpose of a denial-of-service attack?
Which function is performed by certificate authorities but is a limitation of registration authorities?
Drag and drop the common security threats from the left onto the definitions on the right.
An engineer must deploy Cisco Secure Email with Cloud URL Analysis and must meet these requirements:
To protect the network from large-scale virus outbreaks
To protect the network from non-viral attacks such as phishing scams and malware distribution
To provide active analysis of the structure of the URL and information about the domain and page contents
Which two prerequisites must the engineer ensure are configured? (Choose two.)
Which key feature of Cisco ZFW is unique among other Cisco IOS firewall solutions?
Which Cisco security solution gives the most complete view of the relationships and evolution of Internet domains IPs, and flies, and helps to pinpoint attackers' infrastructures and predict future threat?
Which security solution protects users leveraging DNS-layer security?
A security administrator is designing an email protection solution for an onsite email server and must meet these requirements:
Remove malware from email before it reaches corporate premises
Drop emails with risky links automatically
Block access to newly infected sites with real-time URL analysis
Which solution must be used?
Which compliance status is shown when a configured posture policy requirement is not met?
Which Cisco security solution integrates with cloud applications like Dropbox and Office 365 while protecting data from being exfiltrated?
A security test performed on one of the applications shows that user input is not validated. Which security vulnerability is the application more susceptible to because of this lack of validation?
An engineer is deploying a Cisco Secure Email Gateway and must ensure it reaches the Cisco update servers to retrieve new rules. The engineer must now manually configure the Outbreak Filter rules on an AsyncOS for Cisco Secure Email Gateway. Only outdated rules must be replaced. Up-to-date rules must be retained. Which action must the engineer take next to complete the configuration?
On Cisco Firepower Management Center, which policy is used to collect health modules alerts from managed
devices?
Which solution is more secure than the traditional use of a username and password and encompasses at least two of the methods of authentication?
What is the purpose of the My Devices Portal in a Cisco ISE environment?
Why is it important to have logical security controls on endpoints even though the users are trained to spot security threats and the network devices already help prevent them?
Which type of algorithm provides the highest level of protection against brute-force attacks?
Which Cisco Firewall solution requires zone definition?
What are two reasons for implementing a multifactor authentication solution such as Duo Security provide to an
organization? (Choose two)
Which type of protection encrypts RSA keys when they are exported and imported?
How does the Cisco WSA enforce bandwidth restrictions for web applications?
What is a difference between an XSS attack and an SQL injection attack?
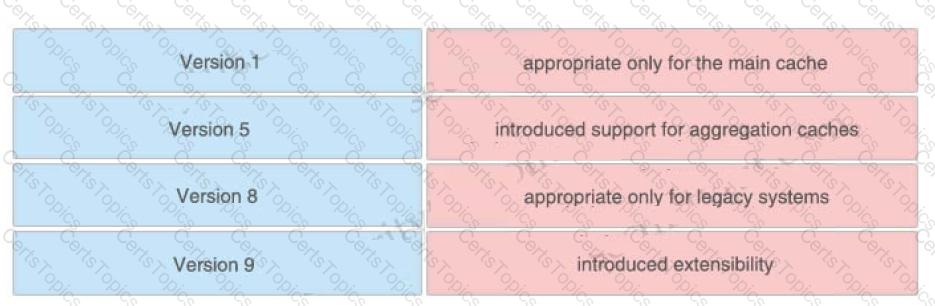
Drag and drop the NetFlow export formats from the left onto the descriptions on the right.
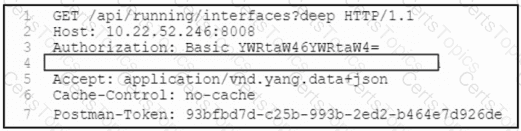
Refer to the exhibit. A network engineer must retrieve the interface configuration on a Cisco router by using the NETCONF API. The engineer uses a python script to automate the activity.
Which code snippet completes the script?
Which solution supports high availability in routed or transparent mode as well as in northbound and
southbound deployments?
Which Cisco ISE feature helps to detect missing patches and helps with remediation?
Which action must be taken in the AMP for Endpoints console to detect specific MD5 signatures on endpoints and then quarantine the files?
What is the term for when an endpoint is associated to a provisioning WLAN that is shared with guest
access, and the same guest portal is used as the BYOD portal?
An organization recently installed a Cisco Secure Web Appliance and would like to take advantage of the AVC engine to allow the organization to create a policy to control application-specific activity. After enabling the AVC engine, what must be done to implement this?
A network administrator configures Dynamic ARP Inspection on a switch. After Dynamic ARP Inspection is applied, all users on that switch are unable to communicate with any destination. The network administrator checks the interface status of all interfaces, and there is no err-disabled interface. What is causing this problem?
What are the components of endpoint protection against social engineering attacks?
An engineer integrates Cisco FMC and Cisco ISE using pxGrid Which role is assigned for Cisco FMC?
Which two key and block sizes are valid for AES? (Choose two)
Which Talos reputation center allows you to track the reputation of IP addresses for email and web traffic?
An engineer is configuring guest WLAN access using Cisco ISE and the Cisco WLC. Which action temporarily gives guest endpoints access dynamically while maintaining visibility into who or what is connecting?
What is the difference between a vulnerability and an exploit?
A network administrator needs to find out what assets currently exist on the network. Third-party systems need to be able to feed host data into Cisco Firepower. What must be configured to accomplish this?
Which Cisco Advanced Malware protection for Endpoints deployment architecture is designed to keep data
within a network perimeter?
Which Cisco security solution protects remote users against phishing attacks when they are not connected to
the VPN?
What are two functions of TAXII in threat intelligence sharing? (Choose two.)
When a next-generation endpoint security solution is selected for a company, what are two key
deliverables that help justify the implementation? (Choose two.)
What is the primary benefit of deploying an ESA in hybrid mode?
What is an advantage of using a next-generation firewall compared to a traditional firewall?
What are two differences between a Cisco Secure Web Appliance that is running in transparent mode and one running in explicit mode? (Choose two.)
An engineer is configuring IPsec VPN and needs an authentication protocol that is reliable and supports ACK
and sequence. Which protocol accomplishes this goal?
Refer to the exhibit.
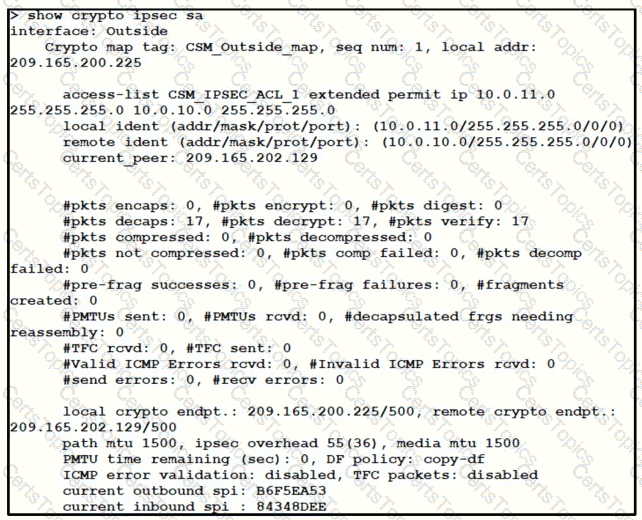
Traffic is not passing through IPsec site-to-site VPN on the Firepower Threat Defense appliance. What is causing this issue?
Which type of data does the Cisco Stealthwatch system collect and analyze from routers, switches, and firewalls?
What does the Cloudlock Apps Firewall do to mitigate security concerns from an application perspective?
What is an advantage of network telemetry over SNMP pulls?
Which type of encryption uses a public key and private key?
Which cloud model is a collaborative effort where infrastructure is shared and jointly accessed by several organizations from a specific group?
Which open standard creates a framework for sharing threat intelligence in a machine-digestible format?
An engineer is configuring Dropbox integration with Cisco Cloudlock. Which action must be taken before granting API access in the Dropbox admin console?
Which two Cisco Umbrella security categories are used to prevent command-and-control callbacks on port 53 and protect users from being tricked into providing confidential information? (Choose two.)
An engineer is configuring Cisco Umbrella and has an identity that references two different policies. Which action ensures that the policy that the identity must use takes precedence over the second one?
What is the function of SDN southbound API protocols?
Which Cisco ISE service checks the compliance of endpoints before allowing the endpoints to connect to
the network?
Which feature is used to restrict communication between interfaces on a Cisco ASA?
Where are individual sites specified to be blacklisted in Cisco Umbrella?
A network engineer must create an access control list on a Cisco Adaptive Security Appliance firewall. The access control list must permit HTTP traffic to the internet from the organization's inside network 192.168.1.0/24. Which IOS command must oe used to create the access control list?
Which Cisco security solution provides patch management in the cloud?
An organization recently installed a Cisco WSA and would like to take advantage of the AVC engine to allow the organization to create a policy to control application specific activity. After enabling the AVC engine, what must be done to implement this?
Which two probes are configured to gather attributes of connected endpoints using Cisco Identity Services
Engine? (Choose two)
What are two differences between a Cisco WSA that is running in transparent mode and one running in explicit mode? (Choose two)
What does endpoint isolation in Cisco AMP for Endpoints security protect from?
What limits communication between applications or containers on the same node?
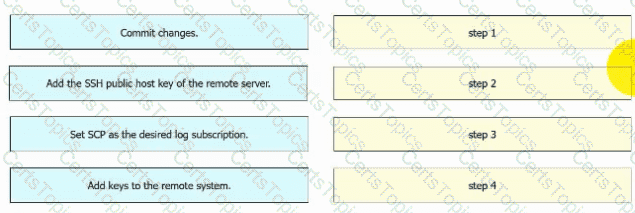
An engineer must configure AsyncOS for Cisco Secure Web Appliance to push log files to a syslog server using the SCP retrieval method. Drag and drop the steps from the left into the sequence on the right to complete the configuration.
On which part of the IT environment does DevSecOps focus?
During a recent security audit a Cisco IOS router with a working IPSEC configuration using IKEv1 was flagged for using a wildcard mask with the crypto isakmp key command The VPN peer is a SOHO router with a dynamically assigned IP address Dynamic DNS has been configured on the SOHO router to map the dynamic IP address to the host name of vpn sohoroutercompany.com In addition to the command crypto isakmp key Cisc425007536 hostname vpn.sohoroutercompany.com what other two commands are now required on the Cisco IOS router for the VPN to continue to function after the wildcard command is removed? (Choose two)
An engineer is configuring 802.1X authentication on Cisco switches in the network and is using CoA as a mechanism. Which port on the firewall must be opened to allow the CoA traffic to traverse the network?
After deploying a Cisco ESA on your network, you notice that some messages fail to reach their destinations.
Which task can you perform to determine where each message was lost?
Which factor must be considered when choosing the on-premise solution over the cloud-based one?
Which type of attack is MFA an effective deterrent for?
What is the most common type of data exfiltration that organizations currently experience?
How does Cisco Umbrella protect clients when they operate outside of the corporate network?
Why should organizations migrate to an MFA strategy for authentication?
Email security has become a high priority task for a security engineer at a large multi-national organization due to ongoing phishing campaigns. To help control this, the engineer has deployed an Incoming Content Filter with a URL reputation of (-10 00 to -6 00) on the Cisco ESA Which action will the system perform to disable any links in messages that match the filter?
A network engineer is deciding whether to use stateful or stateless failover when configuring two ASAs for high availability. What is the connection status in both cases?