A security analyst is reviewing the following log:
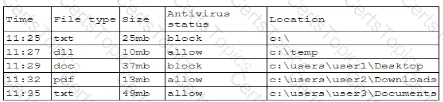
Which of the following possible events should the security analyst investigate further?
Engineers are unable to control pumps at Site A from Site B when the SCADA controller at Site A experiences an outage. A security analyst must provide a secure solution that ensures Site A pumps can be controlled by a SCADA controller at Site B if a similar outage occurs again. Which of the following represents the most cost-effective solution?
A building camera is remotely accessed and disabled from the remote console application during off-hours. A security analyst reviews the following logs:
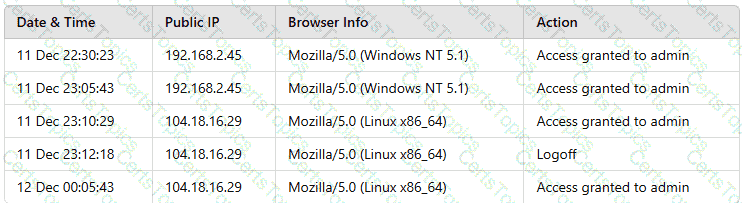
Which of the following actions should the analyst take to best mitigate the threat?
An organization is deploying a new data lake that will centralize records from several applications. During the design phase, the security architect identifies the following requirements:
• The sensitivity levels of the data is different.
• The data must be accessed through stateless API calls after authentication.
• Different users will have access to different data sets.
Which of the following should the architect implement to best meet these requirements?