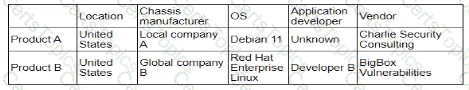
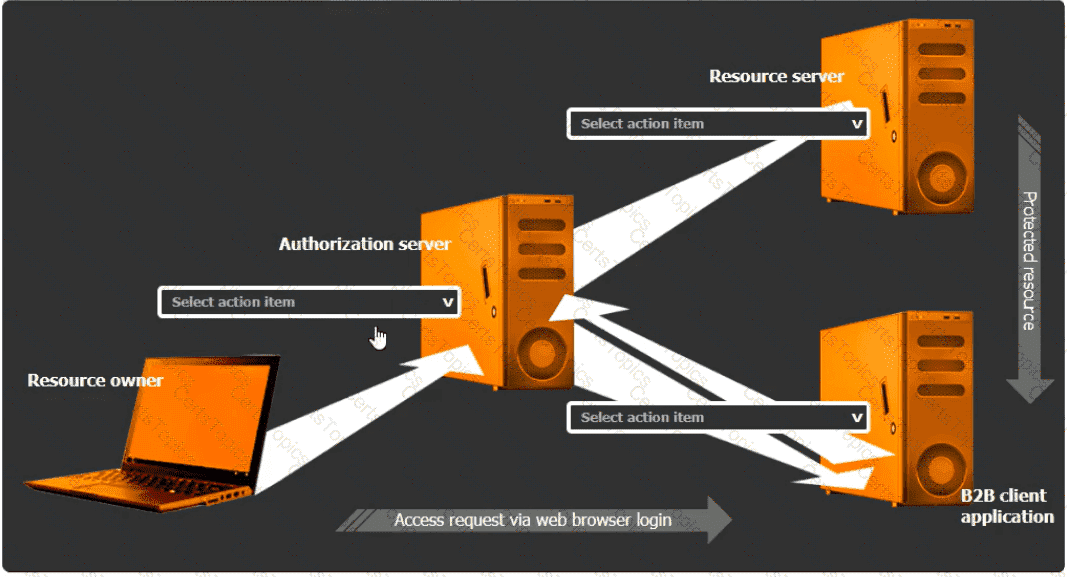
Select the Action Items for the Appropriate Locations:
Authorization Server:
Action Item: Grant access
The authorization server ' s role is to authenticate the user and then issue an authorization code or token that the client application can use to access resources. Granting access involves the server authenticating the resource owner and providing the necessary tokens for the client application.
Resource Server:
Action Item: Access issued tokens
The resource server is responsible for serving the resources requested by the client application. It must verify the issued tokens from the authorization server to ensure the client has the right permissions to access the requested data.
B2B Client Application:
Action Item: Authorize access to other applications
The B2B client application must handle the OAuth flow to authorize access on behalf of the user without requiring direct knowledge of the user ' s credentials. This includes obtaining authorization tokens from the authorization server and using them to request access to the resource server.
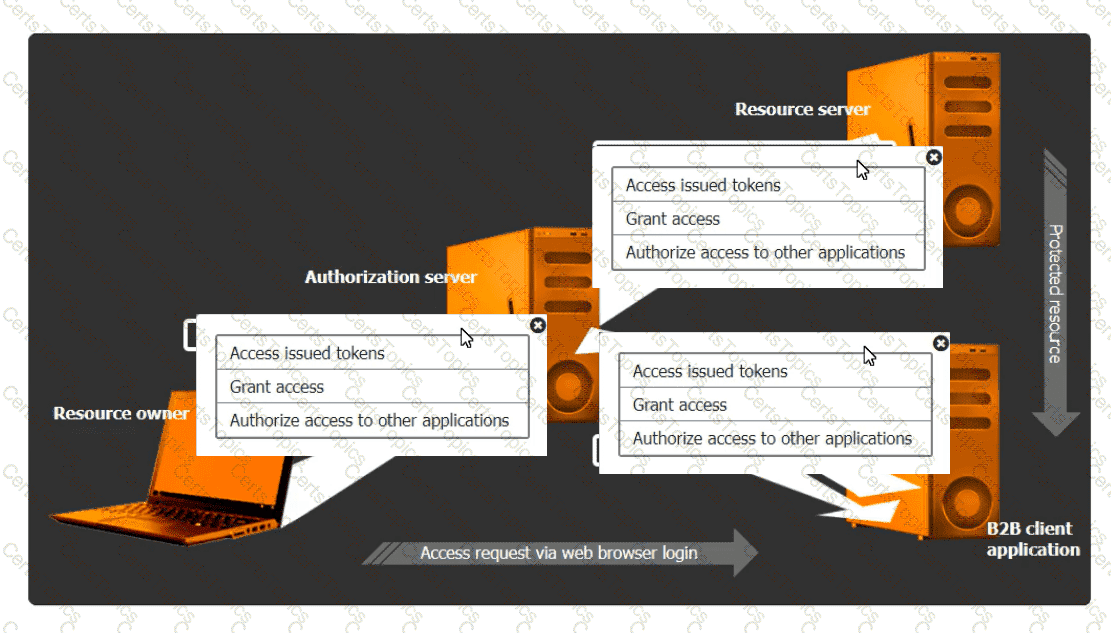
Detailed Explanation:
OAuth 2.0 is designed to provide specific authorization flows for web applications, desktopapplications, mobile phones, and living room devices. The integration involves multiple steps and components, including:
Resource Owner (User):
The user owns the data and resources that are being accessed.
Client Application (B2B Client Application):
Requests access to the resources controlled by the resource owner but does not directly handle the user ' s credentials. Instead, it uses tokens obtained through the OAuth flow.
Authorization Server:
Handles the authentication of the resource owner and issues the access tokens to the client application upon successful authentication.
Resource Server:
Hosts the resources that the client application wants to access. It verifies the access tokens issued by the authorization server before granting access to the resources.
OAuth Workflow:
The resource owner accesses the client application.
The client application redirects the resource owner to the authorization server for authentication.
The authorization server authenticates the resource owner and asks for consent to grant access to the client application.
Upon consent, the authorization server issues an authorization code or token to the client application.
The client application uses the authorization code or token to request access to the resources from the resource server.
The resource server verifies the token with the authorization server and, if valid, grants access to the requested resources.
[References:, CompTIA Security+ Study Guide: Provides comprehensive information on various authentication and authorization protocols, including OAuth., OAuth 2.0 Authorization Framework (RFC 6749): The official documentation detailing the OAuth 2.0 framework, its flows, and components., OAuth 2.0 Simplified: A book by Aaron Parecki that provides a detailed yet easy-to-understand explanation of the OAuth 2.0 protocol., By ensuring that each component in the OAuth workflow performs its designated role, the B2B client application can securely access the necessary resources without compromising user credentials, adhering to the principle of least privilege., , , , , , , ]