An insider scattered multiple USB flash drives with zero-day malware in a company HQ building. Many employees connected the USB flash drives to their workstations. An attacker was able to get access to endpoints from outside, steal user credentials, and exfiltrate confidential information from internal web resources. Which two steps prevent these types of security incidents in the future? (Choose two.)
Which tool should be used for dynamic malware analysis?
An incident response analyst is preparing to scan memory using a YARA rule. How is this task completed?
Refer to the exhibit.
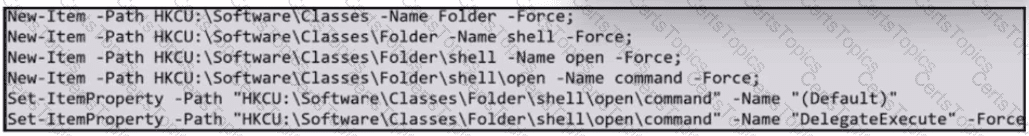
What does the exhibit indicate?