Rotor to the exhibit.
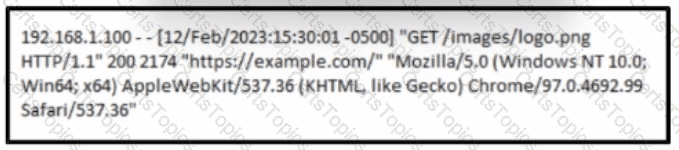
A cybersecurity analyst must analyst the logs from an Apache server for the client. The concern is that an offboarded employee home IP address was potentially used to access the company web server via a still active VPN connection Based on this log entry, what should an analyst conclude?
Refer to the exhibit.
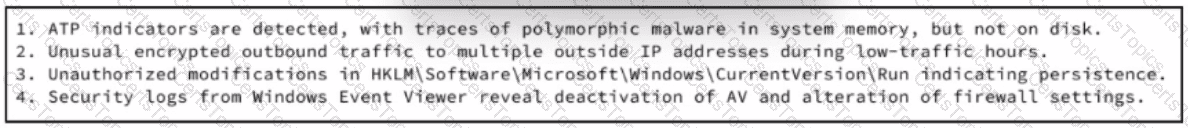
An experienced cybersecurity analyst is investigating a sophisticated suspected breach on a Windows server within an enterprise network and compiled the evidence gathered so far Which action should the analyst prioritize to understand the scope and impact of the breach?
Refer to the exhibit.
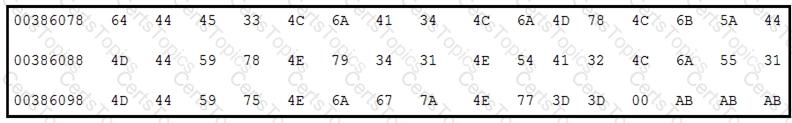
Which encoding technique is represented by this HEX string?
During a routine inspection of system logs, a security analyst notices an entry where Microsoft Word initiated a PowerShell command with encoded arguments. Given that the user's role does not involve scripting or advanced document processing, which action should the analyst take to analyze this output for potential indicators of compromise?