During which phase of the forensic process is data that is related to a specific event labeled and recorded to preserve its integrity?
An employee received an email from a colleague’s address asking for the password for the domain controller. The employee noticed a missing letter within the sender’s address. What does this incident describe?
What are the two differences between vulnerability and exploit? (Choose two.)
Which security monitoring data type is associated with application server logs?
What is the difference between a vulnerability and an attack surface?
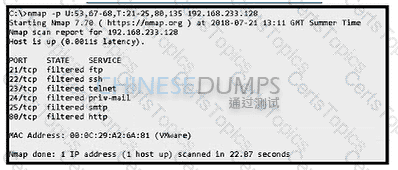
Refer to the exhibit. An attacker scanned the server using Nmap. What did the attacker obtain from this scan?
What are two differences of deep packet inspection compared to stateful firewall inspection? (Choose two.)
What is the difference between a threat and a risk?
What is the impact of false negative alerts when compared to true negative alerts?
Which two attacks are denial-of-service (DoS) attacks? (Choose two.)
What is a key difference between a tampered and an untampered disk image during a forensic investigation?
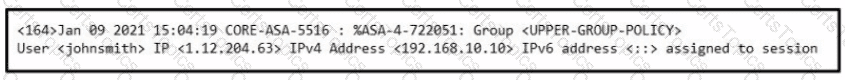
Refer to the exhibit.
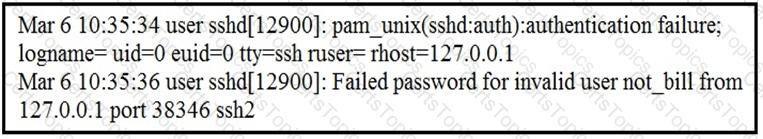
In which Linux log file is this output found?
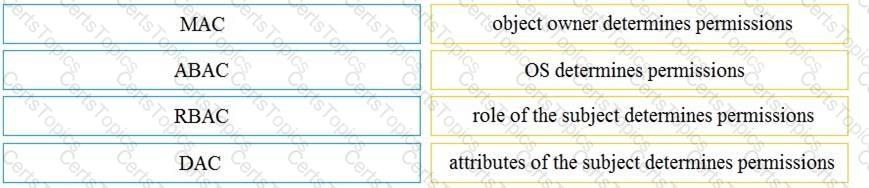
Drag and drop the access control models from the left onto the correct descriptions on the right.
A network engineer informed a security team of a large amount of traffic and suspicious activity from an unknown source to the company DMZ server The security team reviewed the data and identified a potential DDoS attempt According to NIST, at which phase of incident response is the security team?
Which management concept best describes developing, operating, maintaining, upgrading, and disposing of all resources?
A cyberattacker notices a security flaw in a software that a company is using They decide to tailor a specific worm to exploit this flaw and extract saved passwords from the software To which category of the Cyber Kill Cham model does this event belong?
A user received an email attachment named "Hr405-report2609-empl094.exe" but did not run it. Which category of the cyber kill chain should be assigned to this type of event?
Which list identifies the information that the client sends to the server in the negotiation phase of the TLS handshake?
An engineer received a ticket to investigate a potentially malicious file detected by a malware scanner that was trying to execute multiple commands. During the initial review, the engineer discovered that the file was created two days prior. Further analyses show that the file was downloaded from a known malicious domain after a successful phishing attempt on an asset owner. At which phase of the Cyber Kill Chain was this attack mitigated?
Which attack method is being used when an attacker tries to compromise a network with an authentication system that uses only 4-digit numeric passwords and no username?
According to CVSS, which condition is required for attack complexity metrics?
An engineer must analyze a security event from last month. The engineer has access to a .pcap file collected via traffic mirroring and NetFlow data. The engineer must perform checks quickly on a busy network segment without prior knowledge of the incident details. Which source of data should be used for analysis?
What is a difference between an inline and a tap mode traffic monitoring?
What is a Heartbleed vulnerability?
What is the name of the technology that searches for and reports on known weaknesses and flaws present in an organization’s IT infrastructure?
A company is using several network applications that require high availability and responsiveness, such that milliseconds of latency on network traffic is not acceptable. An engineer needs to analyze the network and identify ways to improve traffic movement to minimize delays. Which information must the engineer obtain for this analysis?
Which system monitors local system operation and local network access for violations of a security policy?
A data privacy officer at a marketing firm has received a request from a former client to delete all personally sensitive information held by the company. The firm operates globally and follows international data protection standards. The only information retained about the client is a unique customer ID, "051473912", which is not directly tied to the name, address, or any other identifiable details. Which action should the data privacy officer take?
A developer is working on a project using a Linux tool that enables writing processes to obtain these required results:
If the process is unsuccessful, a negative value is returned.
If the process is successful, 0 value is returned to the child process, and the process ID is sent to the parent process.
Which component results from this operation?
What is the difference between an attack vector and attack surface?
What should a security analyst consider when comparing inline traffic interrogation with traffic tapping to determine which approach to use in the network?
An engineer is working on a ticket for an incident from the incident management team A week ago. an external web application was targeted by a DDoS attack Server resources were exhausted and after two hours it crashed. An engineer was able to identify the attacker and technique used Three hours after the attack, the server was restored and the engineer recommended implementing mitigation by Blackhole filtering and transferred the incident ticket back to the IR team According to NIST SP800-61, at which phase of the incident response did the engineer finish work?
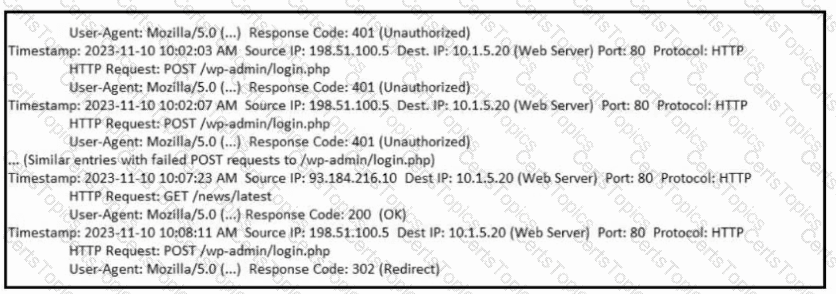
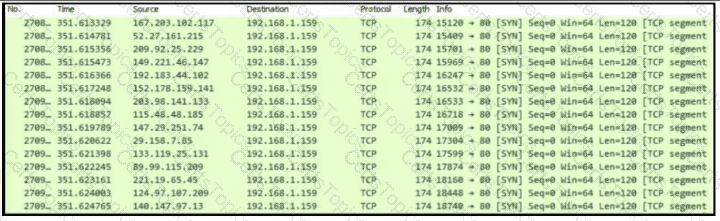
Refer to the exhibit.
Which type of attack is represented?
A threat actor penetrated an organization's network. Using the 5-tuple approach, which data points should the analyst use to isolate the compromised host in a grouped set of logs?
Which NIST IR category stakeholder is responsible for coordinating incident response among various business units, minimizing damage, and reporting to regulatory agencies?
What is an example of social engineering attacks?
When trying to evade IDS/IPS devices, which mechanism allows the user to make the data incomprehensible without a specific key, certificate, or password?
Which signature impacts network traffic by causing legitimate traffic to be blocked?
Which filter allows an engineer to filter traffic in Wireshark to further analyze the PCAP file by only showing the traffic for LAN 10.11.x.x, between workstations and servers without the Internet?
Which utility blocks a host portscan?
An organization recently experienced a major incident in which servers were attacked and data integrity was compromised. The attacker exploited a vulnerability in TLS 1.2 and performed a man-in-the-middle attack by downgrading the connection. Which action should a security specialist take to prevent similar attacks in the future?
What is the difference between an attack vector and an attack surface?
How does TOR alter data content during transit?
Which action matches the weaponization step of the Cyber Kill Chain model?
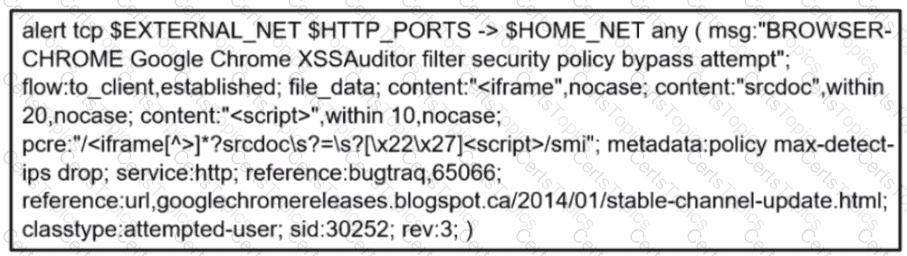
Refer to the exhibit.
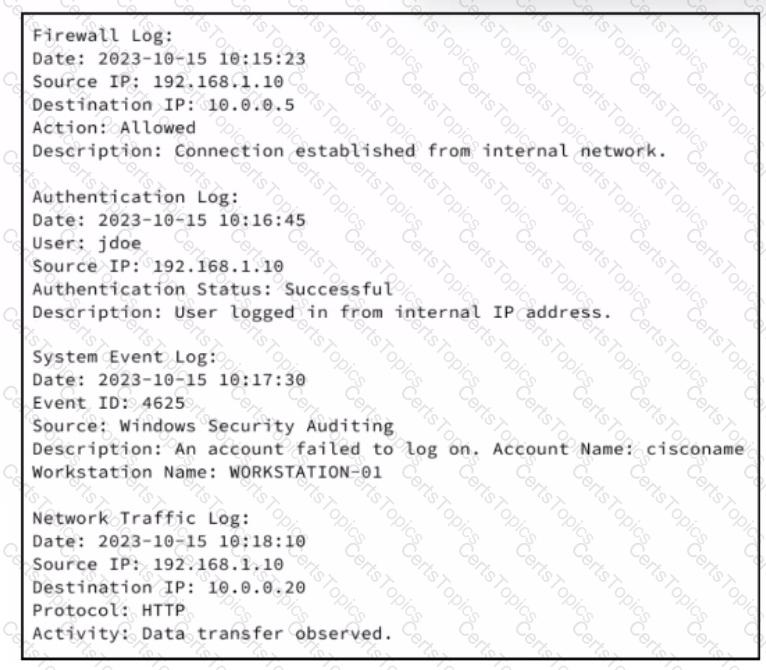
An analyst receives an IDS alert pertaining to a possible data exfiltration attempt. An additional set of logs is collected from different systems and analyzed. Which type of evidence do the logs provide in relation to the primary alert from the IDS?
A security engineer deploys an enterprise-wide host/endpoint technology for all of the company's corporate PCs. Management requests the engineer to block a selected set of applications on all PCs.
Which technology should be used to accomplish this task?
Which information must an organization use to understand the threats currently targeting the organization?
Refer to the exhibit.
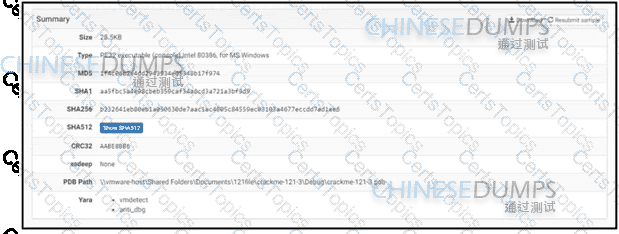
An engineer is reviewing a Cuckoo report of a file. What must the engineer interpret from the report?
An automotive company provides new types of engines and special brakes for rally sports cars. The company has a database of inventions and patents for their engines and technical information Customers can access the database through the company's website after they register and identify themselves. Which type of protected data is accessed by customers?
An engineer must investigate suspicious connections. Data has been gathered using a tcpdump command on a Linux device and saved as sandboxmatware2022-12-22.pcaps file.The engineer is trying to open the tcpdump in the Wireshark tool. What is the expected result?
What is an attack surface as compared to a vulnerability?
Which technique is a low-bandwidth attack?
Which data format is the most efficient to build a baseline of traffic seen over an extended period of time?
What is an advantage of symmetric over asymmetric encryption?
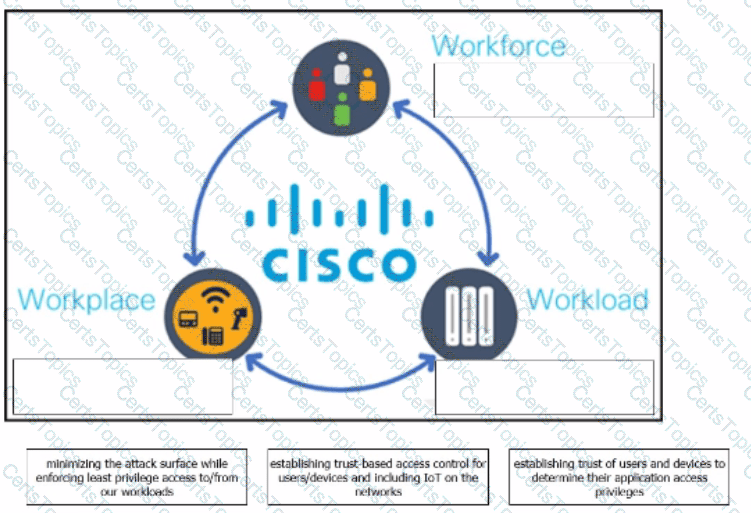
The Cisco Zero Trust Architecture simplifies the zero trust journey into three critical areas. Drag and drop the definitions onto the graphic to describe zero trust from the Cisco perspective.
Which security technology allows only a set of pre-approved applications to run on a system?
What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
How does statistical detection differ from rule-based detection?
Refer to the exhibit.
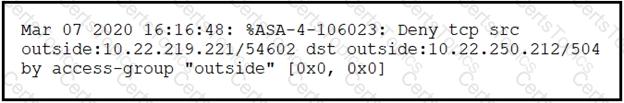
Which technology generates this log?
What is a disadvantage of the asymmetric encryption system?
What is a ransomware attack?
Refer to the exhibit.
Which type of evidence is this file?
A system administrator is ensuring that specific registry information is accurate.
Which type of configuration information does the HKEY_LOCAL_MACHINE hive contain?
Which action should be taken if the system is overwhelmed with alerts when false positives and false negatives are compared?
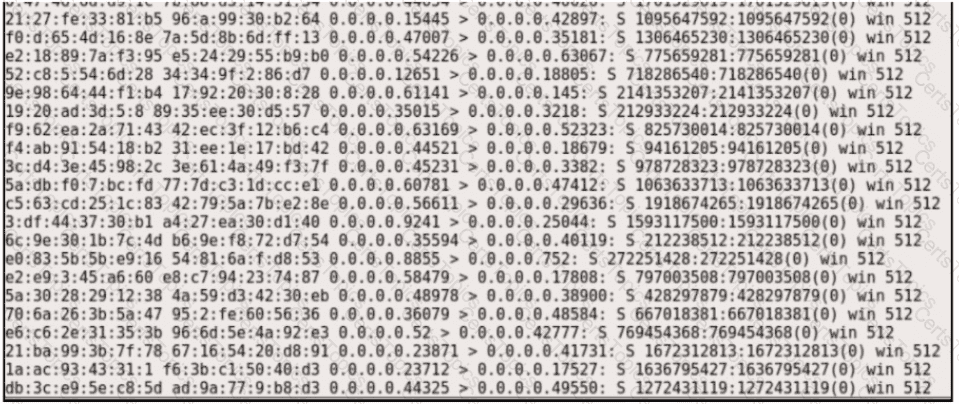
Refer to the exhibit. What is occurring?
Which metric in CVSS indicates an attack that takes a destination bank account number and replaces it with a different bank account number?
Refer to the exhibit.
Which technology produced the log?
Which scenario describes a social engineering attack?
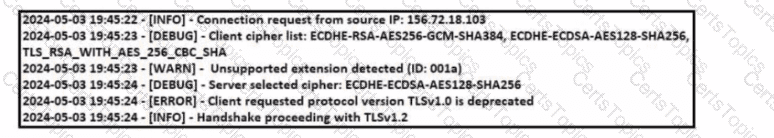
Refer to the exhibit Which TLS version does this client support?
What describes a buffer overflow attack?
What is a benefit of agent-based protection when compared to agentless protection?
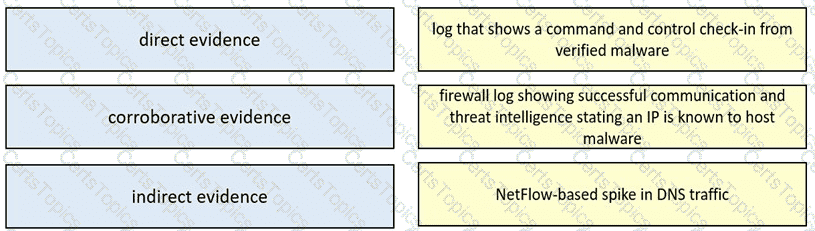
Drag and drop the type of evidence from the left onto the description of that evidence on the right.
An organization is cooperating with several third-party companies. Data exchange is on an unsecured channel using port 80 Internal employees use the FTP service to upload and download sensitive data An engineer must ensure confidentiality while preserving the integrity of the communication. Which technology must the engineer implement in this scenario'?
A company had a recent breach and lost confidential data to a competitor. An internal investigation found out that a new junior accounting specialist logged in to the accounting server with their user ID and stole confidential data. The junior accounting specialist denies the action and claims that the attempt was done by someone else. During court proceedings, the company presents logs and CCTV camera recordings that show the malicious insider in action. Which type of evidence has the company presented?
What is the difference between authentication and authorization?
What is the difference between mandatory access control (MAC) and discretionary access control (DAC)?
What is a difference between a threat and a risk?
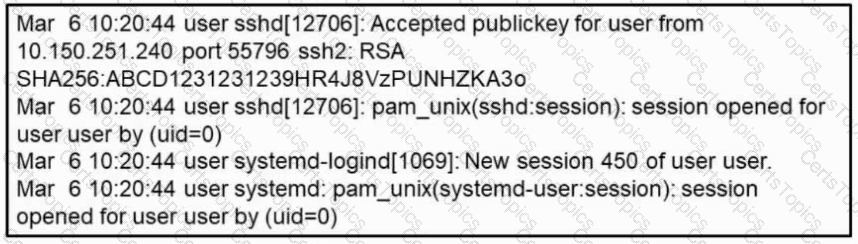
Refer to the exhibit. What occurred on this system based on this output?
What is the difference between discretionary access control (DAC) and role-based access control (RBAC)?
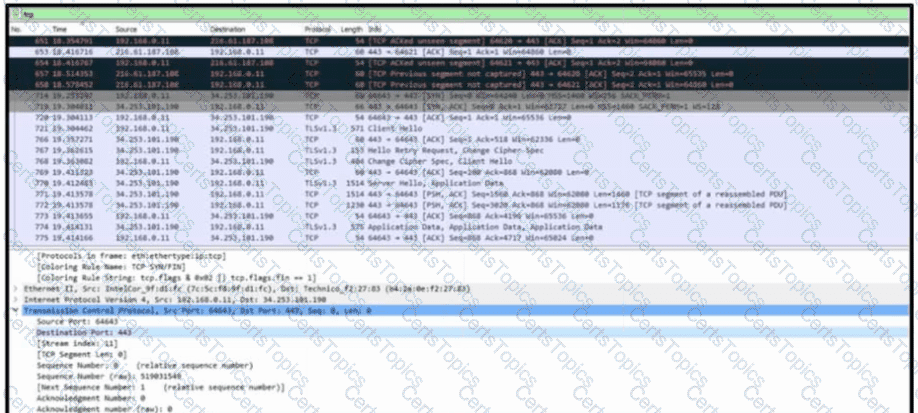
Refer to the exhibit. A communication issue exists between hosts 192.168.0.11 and 34.253.101.190. What is a description of the initial TCP connection?
What is the virtual address space for a Windows process?
Which items is an end-point application greylist used?
An engineer is sharing folders and files with different departments and got this error: "No such file or directory". What must the engineer verify next?
Refer to the exhibit.
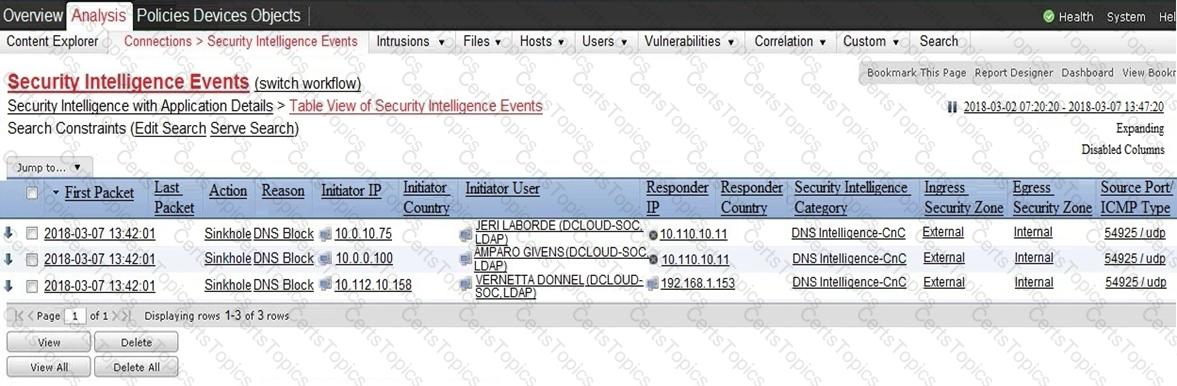
Which two elements in the table are parts of the 5-tuple? (Choose two.)
What is the purpose of a ransomware attack?
Refer to the exhibit.

Which component is identifiable in this exhibit?
Which type of evasion technique is accomplished by separating the traffic into smaller segments before transmitting across the network?
Syslog collecting software is installed on the server For the log containment, a disk with FAT type partition is used An engineer determined that log files are being corrupted when the 4 GB tile size is exceeded. Which action resolves the issue?
An engineer is analyzing a recent breach where confidential documents were altered and stolen by the receptionist. Further analysis shows that the threat actor connected an externa USB device to bypass security restrictions and steal data. The engineer could not find an external USB device Which piece of information must an engineer use for attribution in an investigation?
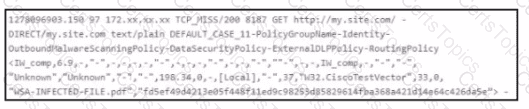
Refer to the exhibit.
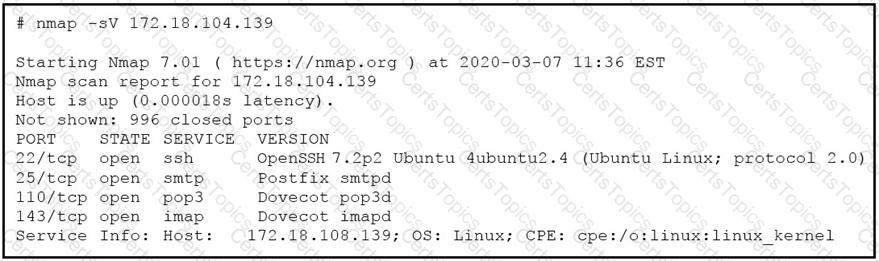
What does the output indicate about the server with the IP address 172.18.104.139?
How does agentless monitoring differ from agent-based monitoring?
Refer to the exhibit.
A company's user HTTP connection to a malicious site was blocked according to configured policy What is the source technology used for this measure'?
An analyst see that this security alert "Default-Botnet-Communication-Detection-By-Endpoint" has been raised from the IPS. The analyst checks and finds that an endpoint communicates to the C&C. How must an impact from this event be categorized?
Which event is a vishing attack?
What is the impact of false positive alerts on business compared to true positive?
Refer to the exhibit A penetration tester runs the Nmap scan against the company server to uncover possible vulnerabilities and exploit them Which two elements can the penetration tester identity from the scan results? (Choose two.)
What is personally identifiable information that must be safeguarded from unauthorized access?
Which are two denial-of-service attacks? (Choose two.)
What is a difference between SIEM and SOAR?
Why should an engineer use a full packet capture to investigate a security breach?
An engineer received an alert affecting the degraded performance of a critical server Analysis showed a heavy CPU and memory load What is the next step the engineer should take to investigate this resource usage7
Which technology assures that the information transferred from point A to point B is unaltered and authentic?
According to CVSS, what is attack complexity?
What is the practice of giving an employee access to only the resources needed to accomplish their job?
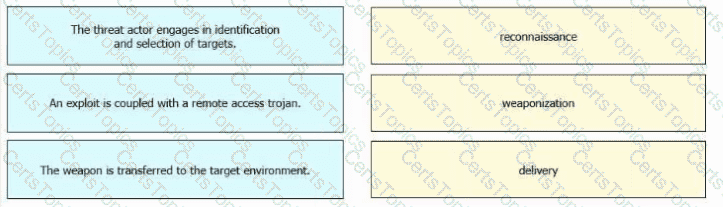
Drag and drop the definitions from the left onto the phases on the right to classify intrusion events according to the Cyber Kill Chain model.
Which technology prevents end-device to end-device IP traceability?
What is the impact of encapsulation on the network?
Refer to the exhibit.
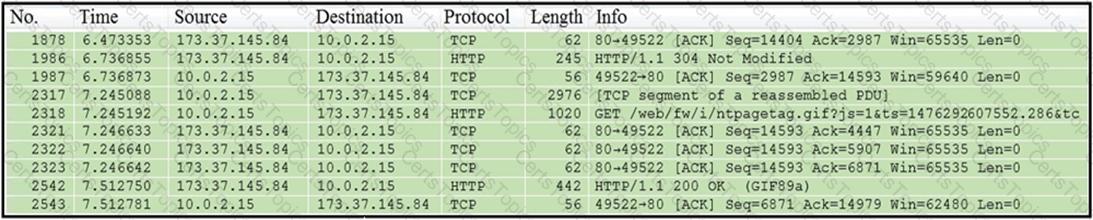
Which packet contains a file that is extractable within Wireshark?
What does cyber attribution identify in an investigation?
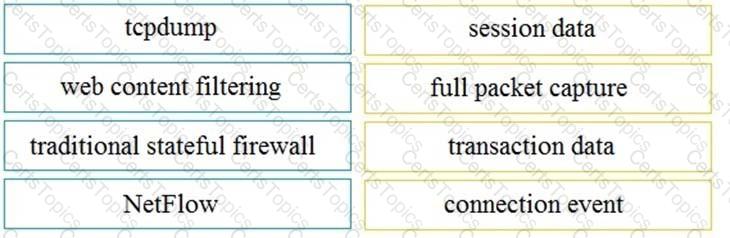
Drag and drop the technology on the left onto the data type the technology provides on the right.
Which type of data must an engineer capture to analyze payload and header information?
Which event is user interaction?
What is a comparison between rule-based and statistical detection?
An engineer needs to have visibility on TCP bandwidth usage, response time, and latency, combined with deep packet inspection to identify unknown software by its network traffic flow. Which two features of Cisco Application Visibility and Control should the engineer use to accomplish this goal? (Choose two.)
What is the benefit of processing statistical data for security systems?
An engineer runs a suspicious file in a sandbox analysis tool to see the outcome. The analysis report shows that outbound callouts were made post infection.
Which two pieces of information from the analysis report are needed to investigate the callouts? (Choose two.)
Refer to exhibit.
An engineer is Investigating an Intrusion and Is analyzing the pcap file. Which two key elements must an engineer consider? (Choose two.)
What is a scareware attack?
What is the difference between the ACK flag and the RST flag?
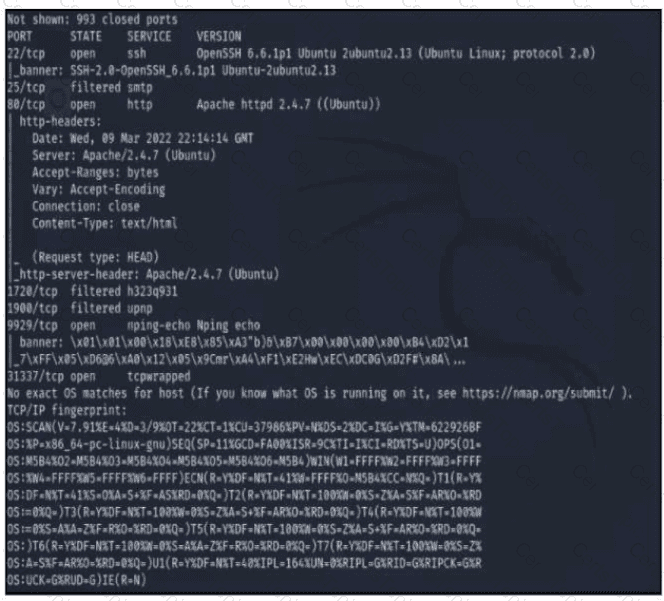
Refer to the exhibit.
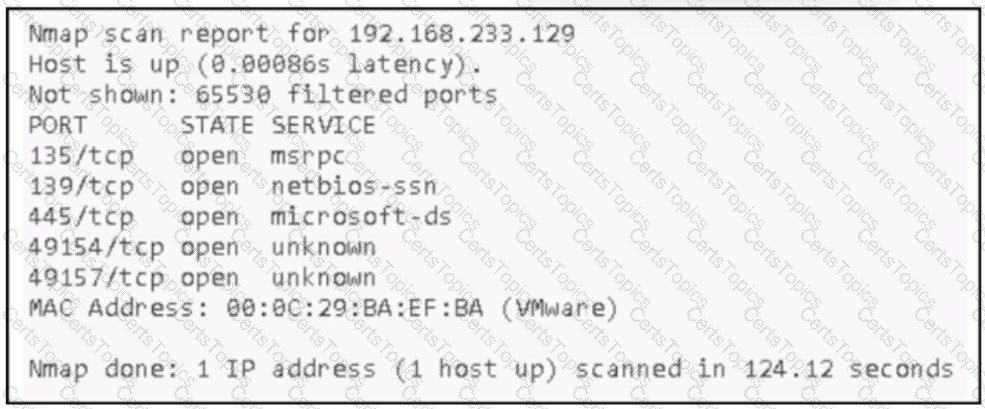
An attacker Infiltrated an organization's network and ran a scan to advance with the lateral movement technique. Which two elements from the scan assist the attacker? (Choose two.)
A company receptionist received a threatening call referencing stealing assets and did not take any action assuming it was a social engineering attempt. Within 48 hours, multiple assets were breached, affecting the confidentiality of sensitive information. What is the threat actor in this incident?
Refer to the exhibit.
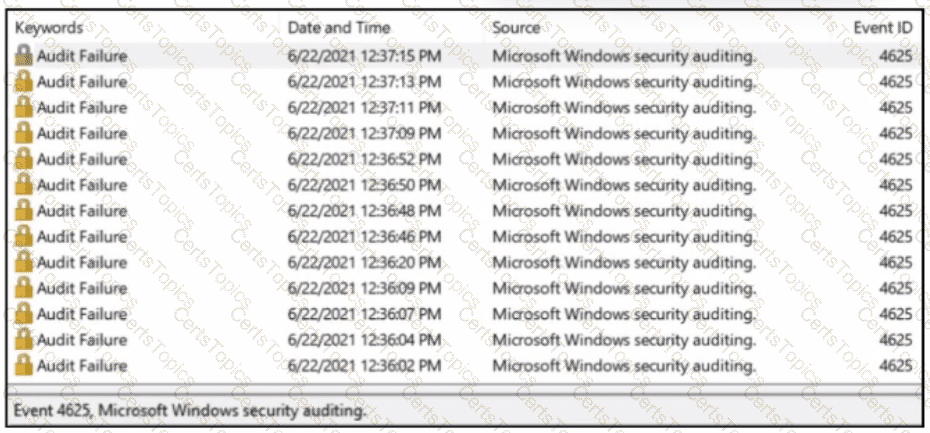
A SOC analyst received a message from SIEM about abnormal activity on the Windows server The analyst checked the Windows event log and saw numerous Audit Failures logs. What is occurring?
Refer to the exhibit.
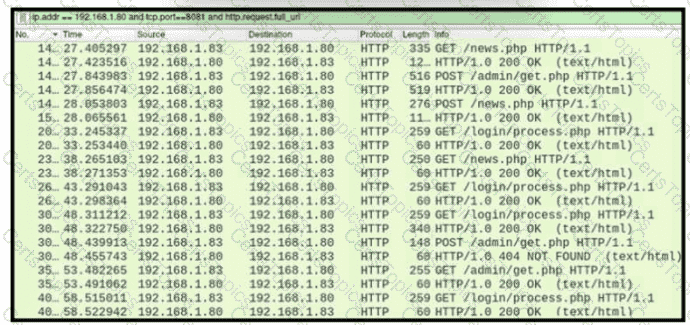
A network administrator is investigating suspicious network activity by analyzing captured traffic. An engineer notices abnormal behavior and discovers that the default user agent is present in the headers of requests and data being transmitted What is occurring?
What is vulnerability management?
Which piece of information is needed for attribution in an investigation?
Refer to the exhibit.

Which type of log is displayed?
What is a difference between SI EM and SOAR security systems?
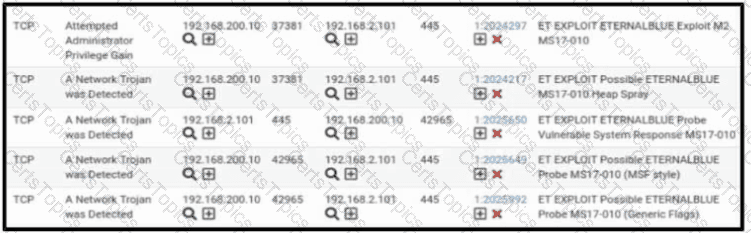
Refer to the exhibit. A security engineer receives several alerts from the SNORT IPS/IDS reporting malicious traffic. What should the engineer understand by examining the SNORT logs?
A security engineer must protect the company from known issues that trigger adware. Recently new incident has been raised that could harm the system. Which security concepts are present in this scenario?
What describes the defense-m-depth principle?
What is a purpose of a vulnerability management framework?
A malicious file has been identified in a sandbox analysis tool.
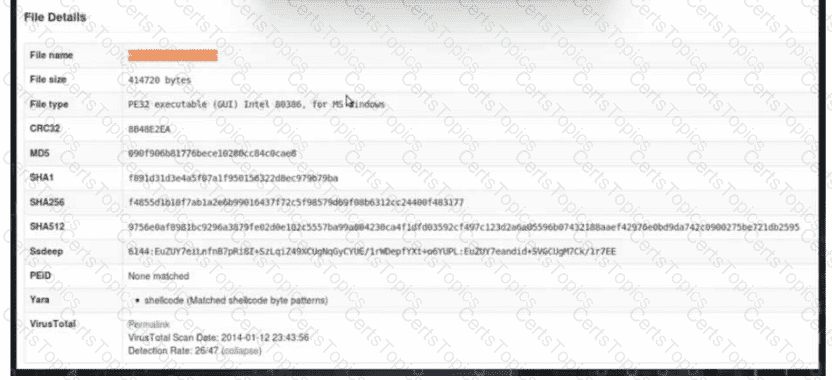
Which piece of information is needed to search for additional downloads of this file by other hosts?
A network engineer noticed in the NetFlow report that internal hosts are sending many DNS requests to external DNS servers A SOC analyst checked the endpoints and discovered that they are infected and became part of the botnet Endpoints are sending multiple DNS requests but with spoofed IP addresses of valid external sources What kind of attack are infected endpoints involved in1?
Refer to exhibit.
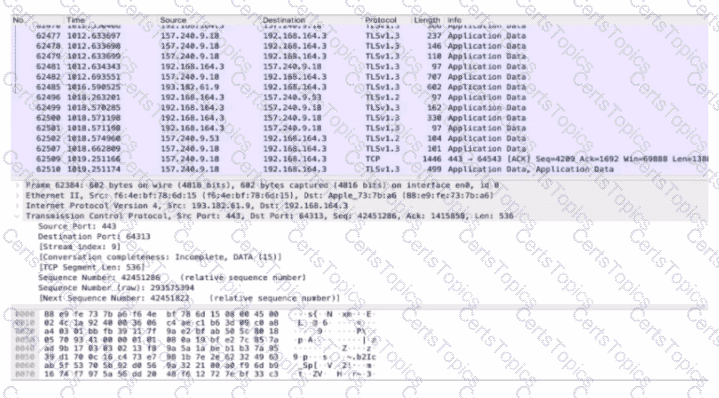
An analyst performs the analysis of the pcap file to detect the suspicious activity. What challenges did the analyst face in terms of data visibility?
What is a description of a social engineering attack?
What is the role of indicator of compromise in an investigation?
Which two measures are used by the defense-m-depth strategy? (Choose two)
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
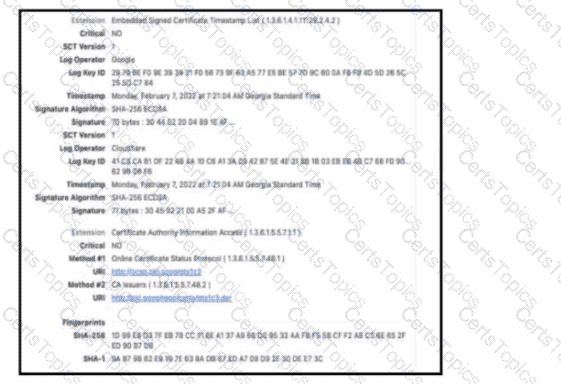
Refer to the exhibit. The figure shows an X 509 certificate. Which field represents the digital cryptographic algorithm used by the issuer to sign the certificate?
An employee reports that someone has logged into their system and made unapproved changes, files are out of order, and several documents have been placed in the recycle bin. The security specialist reviewed the system logs, found nothing suspicious, and was not able to determine what occurred. The software is up to date; there are no alerts from antivirus and no failed login attempts. What is causing the lack of data visibility needed to detect the attack?
What is an evasion technique?
What is data tunneling?