What is the virtual address space for a Windows process?
Which items is an end-point application greylist used?
An engineer is sharing folders and files with different departments and got this error: "No such file or directory". What must the engineer verify next?
Refer to the exhibit.
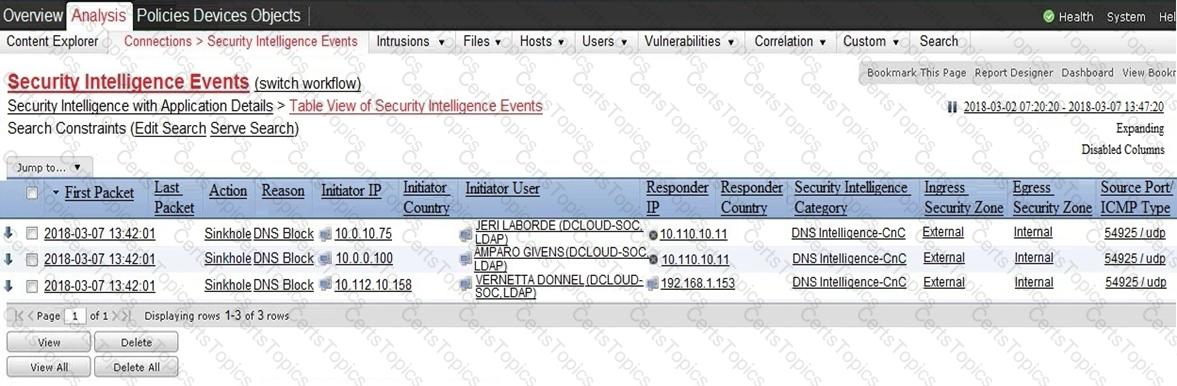
Which two elements in the table are parts of the 5-tuple? (Choose two.)