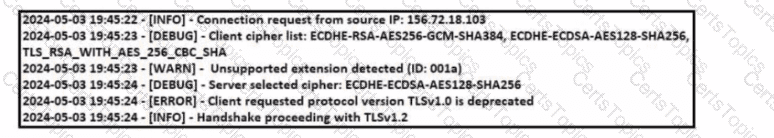
Refer to the exhibit Which TLS version does this client support?
What describes a buffer overflow attack?
What is a benefit of agent-based protection when compared to agentless protection?
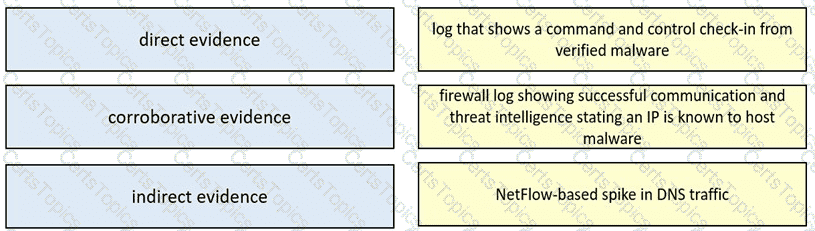
Drag and drop the type of evidence from the left onto the description of that evidence on the right.