What is the difference between a vulnerability and an attack surface?
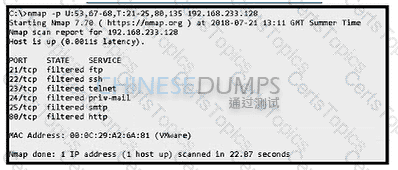
Refer to the exhibit. An attacker scanned the server using Nmap. What did the attacker obtain from this scan?
What are two differences of deep packet inspection compared to stateful firewall inspection? (Choose two.)
What is the difference between a threat and a risk?