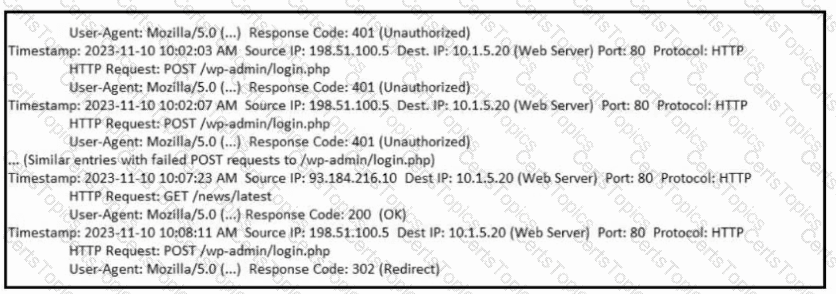
Refer to the exhibit. What is occurring?
Which metric in CVSS indicates an attack that takes a destination bank account number and replaces it with a different bank account number?
Refer to the exhibit.
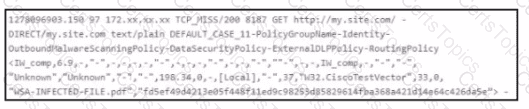
Which technology produced the log?
Which scenario describes a social engineering attack?