What should an engineer use to aid the trusted exchange of public keys between user tom0411976943 and dan1968754032?
How does statistical detection differ from rule-based detection?
Refer to the exhibit.
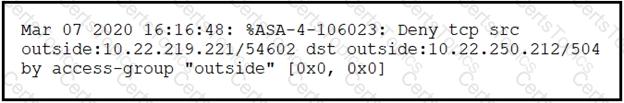
Which technology generates this log?
What is a disadvantage of the asymmetric encryption system?