What does cyber attribution identify in an investigation?
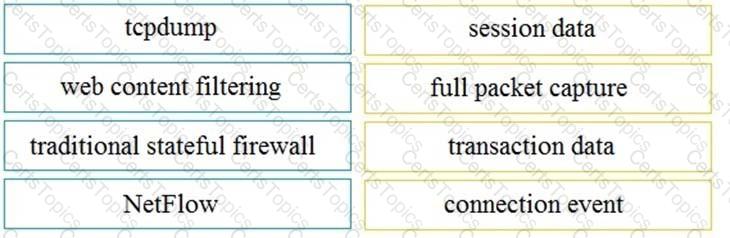
Drag and drop the technology on the left onto the data type the technology provides on the right.
Which type of data must an engineer capture to analyze payload and header information?
Which event is user interaction?