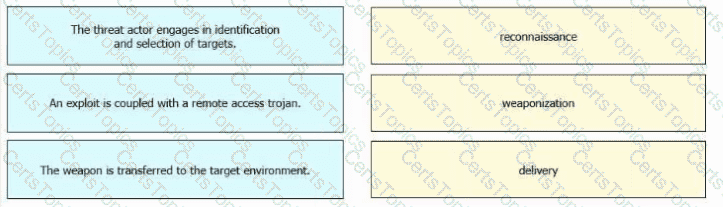
Drag and drop the definitions from the left onto the phases on the right to classify intrusion events according to the Cyber Kill Chain model.
Which technology prevents end-device to end-device IP traceability?
What is the impact of encapsulation on the network?
Refer to the exhibit.
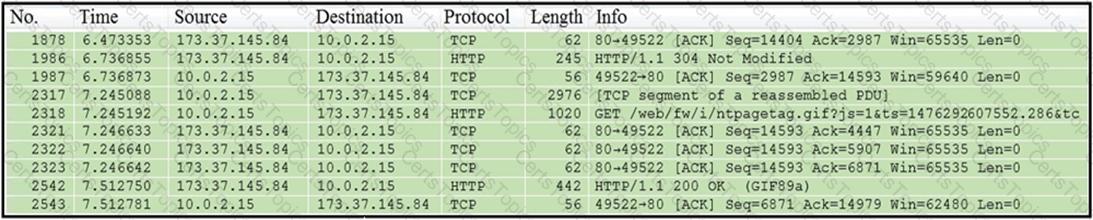
Which packet contains a file that is extractable within Wireshark?