Which two measures are used by the defense-m-depth strategy? (Choose two)
Which classification of cross-site scripting attack executes the payload without storing it for repeated use?
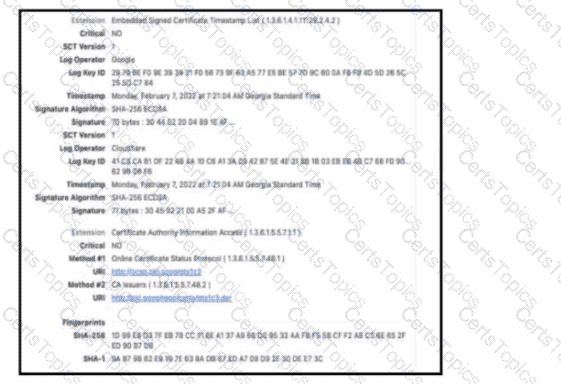
Refer to the exhibit. The figure shows an X 509 certificate. Which field represents the digital cryptographic algorithm used by the issuer to sign the certificate?
An employee reports that someone has logged into their system and made unapproved changes, files are out of order, and several documents have been placed in the recycle bin. The security specialist reviewed the system logs, found nothing suspicious, and was not able to determine what occurred. The software is up to date; there are no alerts from antivirus and no failed login attempts. What is causing the lack of data visibility needed to detect the attack?