Which piece of information is needed for attribution in an investigation?
Refer to the exhibit.

Which type of log is displayed?
What is a difference between SI EM and SOAR security systems?
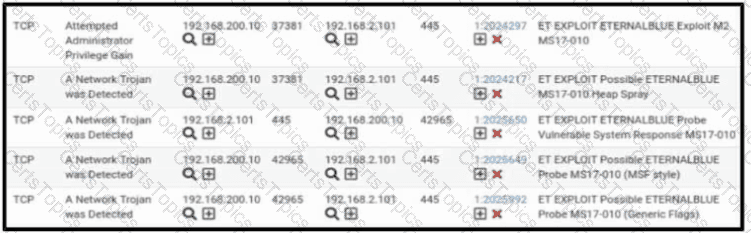
Refer to the exhibit. A security engineer receives several alerts from the SNORT IPS/IDS reporting malicious traffic. What should the engineer understand by examining the SNORT logs?