ECCouncil Related Exams
312-96 Exam







James is a Java developer working INFR INC. He has written Java code to open a file, read it line by line and display its content in the text editor. He wants to ensure that any unhandled exception raised by the code should automatically close the opened file stream. Which of the following exception handling block should he use for the above purpose?
Which of the threat classification model is used to classify threats during threat modeling process?
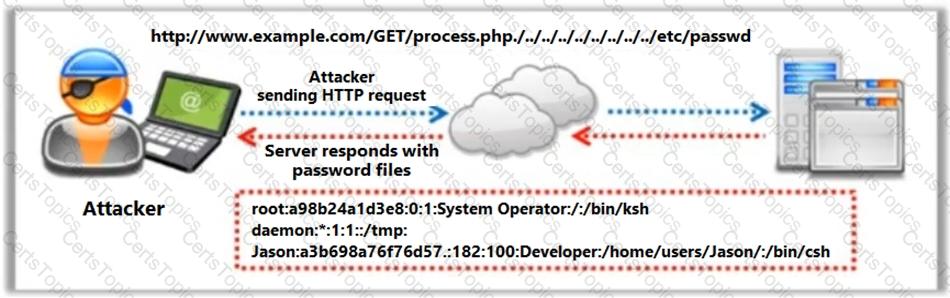
Identify the type of attack depicted in the following figure.