A security analyst sees an increase of vulnerabilities on workstations after a deployment of a company group policy. Which of the following vulnerability types will the analyst most likely find on the workstations?
A security administrator recently reset local passwords and the following values were recorded in the system:
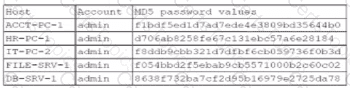
Which of the following in the security administrator most likely protecting against?
Which of the following is used to validate a certificate when it is presented to a user?
Which of the following would most likely be deployed to obtain and analyze attacker activity and techniques?