A penetration tester utilized Nmap to scan host 64.13.134.52 and received the following results:
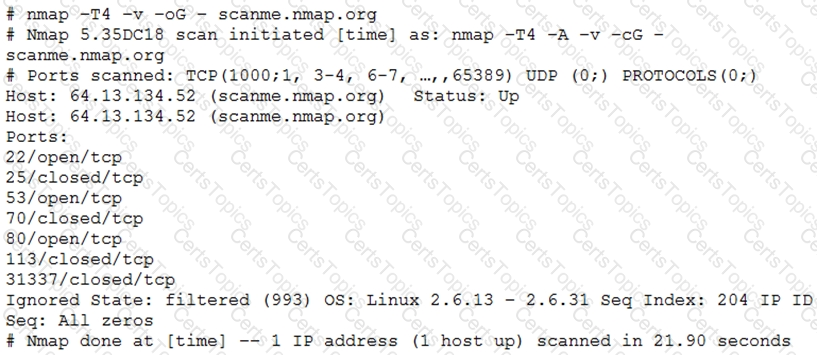
Based on the output, which of the following services are MOST likely to be exploited? (Choose two.)
A penetration tester runs the following command:
l.comptia.local axfr comptia.local
which of the following types of information would be provided?
A penetration tester was able to compromise a web server and move laterally into a Linux web server. The tester now wants to determine the identity of the last user who signed in to the web server. Which of the following log files will show this activity?
Which of the following tools would be best suited to perform a cloud security assessment?