After verifying that API Server is not running, how can you start the API Server?
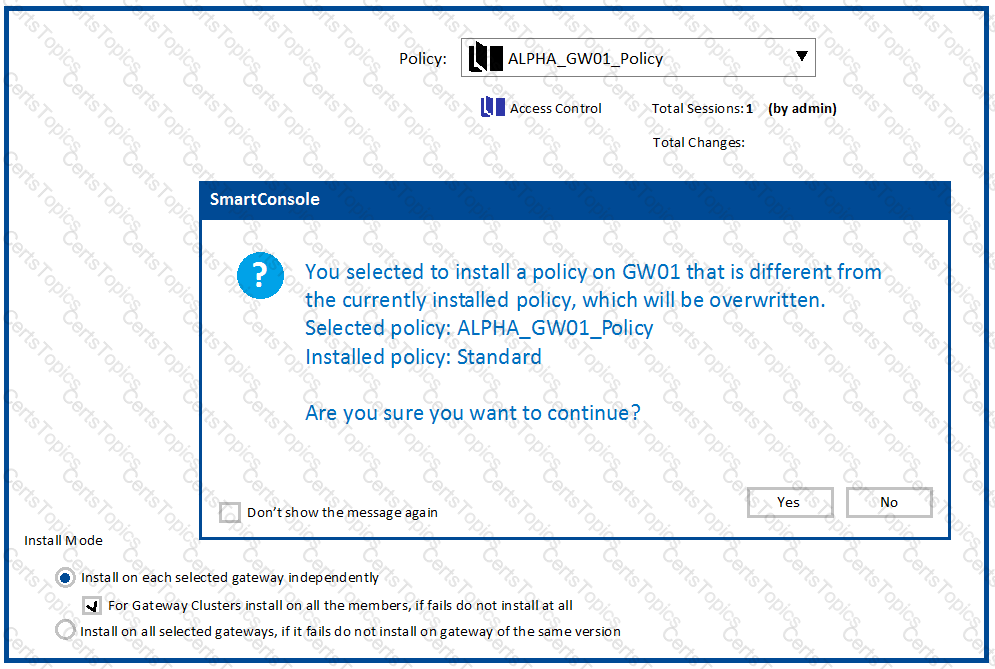
Why would an administrator see the message below?
Access roles allow the firewall administrator to configure network access according to:
By default how often updates are checked when the CPUSE Software Updates Policy is set to Automatic?