You have an Azure AD tenant that contains the users shown in the following table.
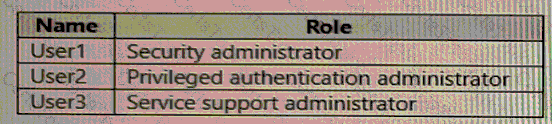
User2 reports that he can only configure multi-factor authenticating (MFA) to use the Microsoft Authenticator app.
You need to ensure that User2 can configure alternate MFA methods.
Which configuration is required, and which user should perform the configuration? To answer, select the appropriate options in the answer area.
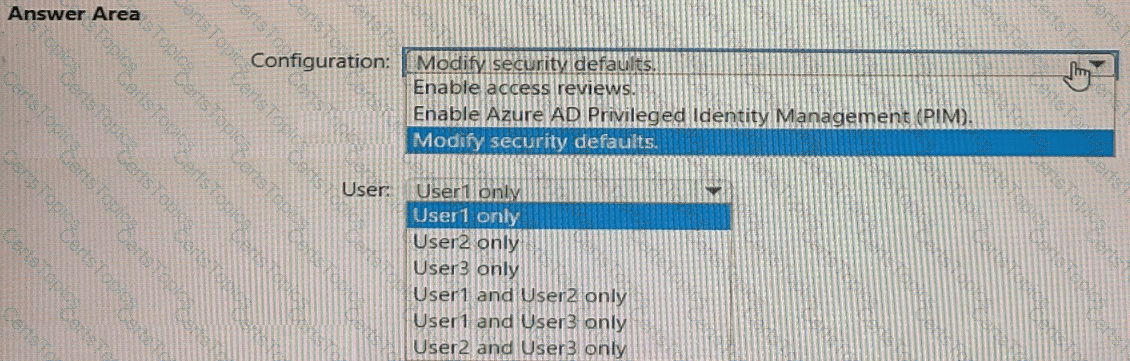
You have an Azure AD tenant contains the users shown in the following table.
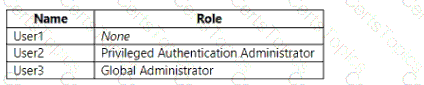
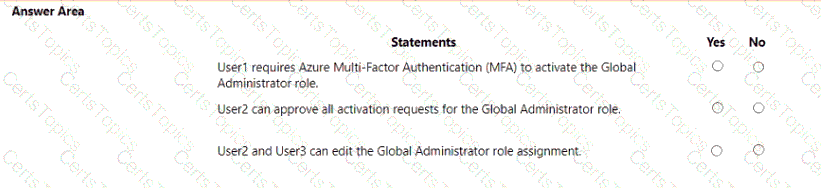
In Azure AD Privileged Identity Management (PIM), you configure the Global Administrator role as shown in the following exhibit.
User 1 is eligible for the Global Administrator role.
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. as a result, these questions will not appear in the review screen.
You have an Amazon Web Services (AWS) account a Google Workspace subscription, and a GitHub account
You deploy an Azure subscription and enable Microsoft 365 Defender.
You need to ensure that you can monitor OAuth authentication requests by using Microsoft Defender for Cloud Apps.
Solution: From the Microsoft 365 Defender portal, you add the GitHub app connector
Does this meet the goal?
You have an Azure subscription that containes a registered app named App1.
You need to review the sign-in activity for App1. The solution must meet the following requirements:
• Identify the number of failed sign-ins.
• Identify the success rate of sign-ins.
• Minimize administrative effort.
What should you use?