You want to hunt for the least-used Windows services that are starting from non-standard locations. Which query below will provide this information?
Refer to the image.
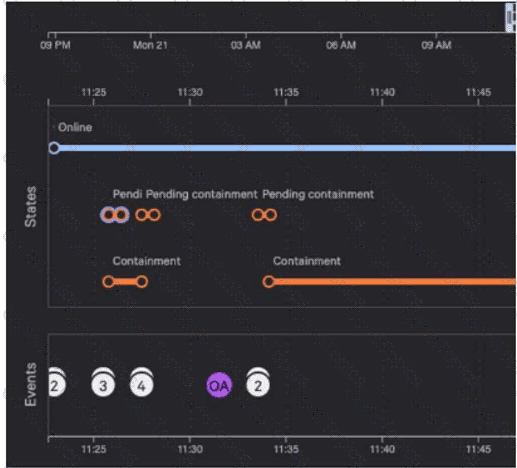
Why are there six pending containment events?
Which built-in hunting report helps you find executables from the Recycle Bin?
You are investigating a suspicious file execution on a host and need to understand how the process interacted with the system. Which combination of key data event types should be used in this scenario to understand the process execution and its network activity?