Refer to the image.
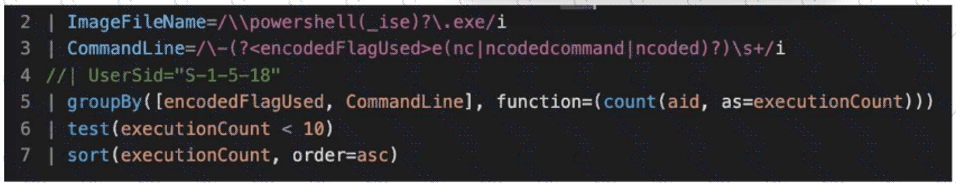
What line item of the query is used to perform outlier analysis?
You suspect one of your endpoint host systems may have a vulnerable BIOS version. Which Investigate Dashboard will confirm vulnerability information such as the type and timeline?
Which document can reference any searchable event and its description?
Which pre-defined reports will show activities that typically indicate suspicious activity occurring on a system?
You want to hunt for the least-used Windows services that are starting from non-standard locations. Which query below will provide this information?
Refer to the image.
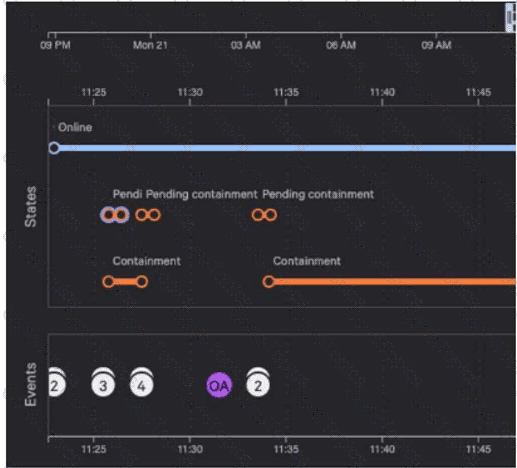
Why are there six pending containment events?
Which built-in hunting report helps you find executables from the Recycle Bin?
You are investigating a suspicious file execution on a host and need to understand how the process interacted with the system. Which combination of key data event types should be used in this scenario to understand the process execution and its network activity?
Which statement will filter for all events that correspond to a new scheduled task registered by the user "Doris"?
Refer to the exhibit.
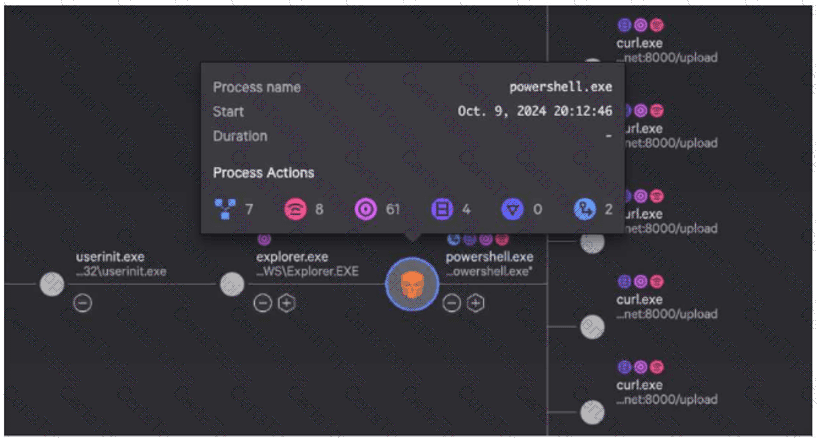
While investigating a process tree, you hover over a malicious powershell.exe process. What is the correct sequence of Process Actions?
An attacker created a scheduled task which executes a remote management application. Which MITRE ATT & CK Matrix for Enterprise stage is this an example of?
You've been tasked with writing a query that would rename the RemoteAddressIP4 field to SourceIP. What would be the correct syntax using the rename() function?
Which hunting query's results could indicate that an adversary is performing reconnaissance from a specific host?
Which is a normal parent of cmd.exe on Windows?
You get a detection for a malicious PowerShell script with the process flow below:
Unknown Process - > chrome.exe - > wscript.exe - > powershell.exe Which process should you investigate further to identify the source of the script?
What can a hunter add at the end of a search string in Advanced Event Search to identify outliers when quantifying the results?
You are investigating a compromise on a Linux host. You suspect that the host is running an older version of Apache and that the Log4j (CVE-2021-44228) vulnerability is being exploited using JNDI lookups. Which CQL query could you use to determine if Log4j is the root cause of the compromise?
You suspect that a user is abusing their admin privileges and you want to see the recent commands they have been utilizing. Which Investigate search will identify this?