CrowdStrike Related Exams
CCFH-202b Exam







You suspect that a user is abusing their admin privileges and you want to see the recent commands they have been utilizing. Which Investigate search will identify this?
Refer to the image.
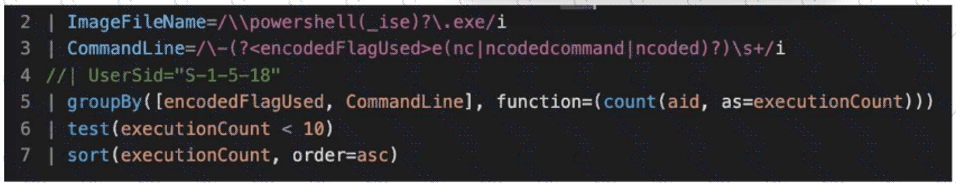
What line item of the query is used to perform outlier analysis?
You are investigating a suspicious file execution on a host and need to understand how the process interacted with the system. Which combination of key data event types should be used in this scenario to understand the process execution and its network activity?