A company is using an intrusion detection and prevention system (IDPS) to scan and analyze intrusion events.
Which IDPS technique uses a database that contains known attack patterns?
Which process eliminates data redundancy in a data set?
Refer to the exhibit:
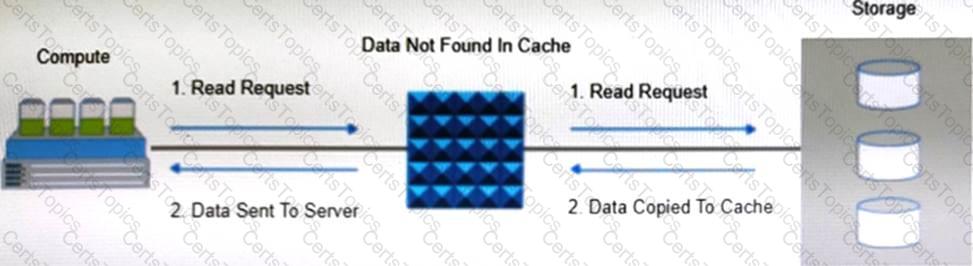
Which operation is represented?
What is a purpose of the policy engine in a data archiving environment?