Google Related Exams
Professional-Cloud-Network-Engineer Exam







Your company has separate Virtual Private Cloud (VPC) networks in a single region for two departments: Sales and Finance. The Sales department's VPC network already has connectivity to on-premises locations using HA VPN, and you have confirmed that the subnet ranges do not overlap. You plan to peer both VPC networks to use the same HA tunnels for on-premises connectivity, while providing internet connectivity for the Google Cloud workloads through Cloud NAT. Internet access from the on-premises locations should not flow through Google Cloud. You need to propagate all routes between the Finance department and on-premises locations. What should you do?
You need to create a GKE cluster in an existing VPC that is accessible from on-premises. You must meet the following requirements:
IP ranges for pods and services must be as small as possible.
The nodes and the master must not be reachable from the internet.
You must be able to use kubectl commands from on-premises subnets to manage the cluster.
How should you create the GKE cluster?
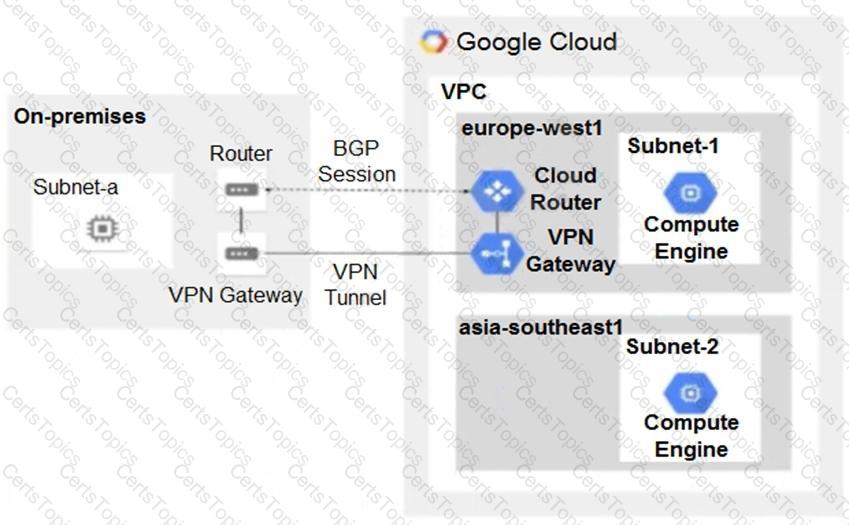
You have the following routing design. You discover that Compute Engine instances in Subnet-2 in the asia-southeast1 region cannot communicate with compute resources on-premises. What should you do?