Pegasystems Related Exams
PEGAPCSSA86V1 Exam







The exam covers:
Advanced case management and data modeling
Security and authentication in Pega applications
Reporting, integrations, and performance optimization
Application debugging and deployment best practices
Advanced user interface (UI) design
Decisioning and rule resolution
PEGAPCSSA86V1 is based on Pega 8.6, while PEGAPCSSA87V1 aligns with the newer Pega 8.7 platform. The 87V1 exam includes updated topics like queue processors, ECS, and ruleset skimming. Both exams target certified system architects with similar formats and question counts.
A view has a part number field that requires the first two characters are letters, and the last four are digits (for example, AB1234).
How do you ensure that the correct pattern is entered when the user exits the field?
The primary purpose of a production ruleset is to allow rules to be
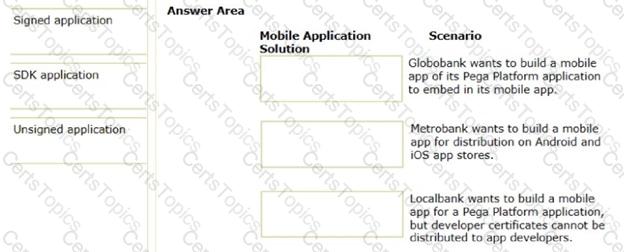
In the Answer Area, drag each mobile application solution on the left to the correct scenario.