EMC Related Exams
D-ISM-FN-23 Exam







Which Dell EMC product is a disk-based backup and recovery solution that provides inherent source-based deduplication?
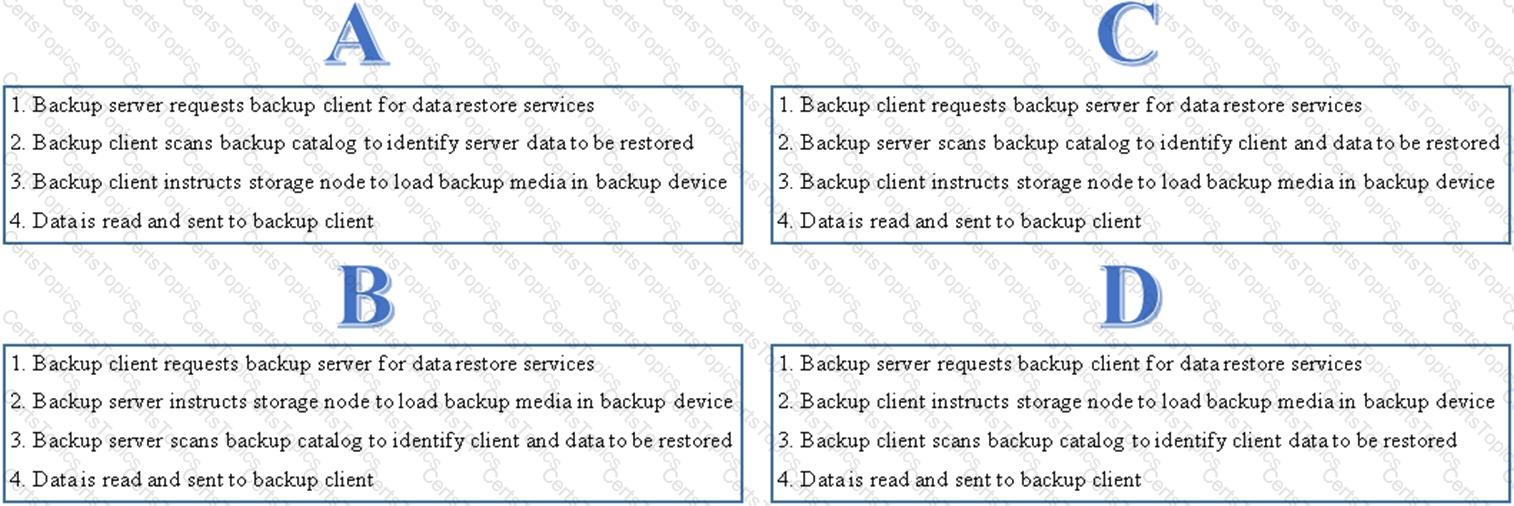
Which option shows the correct sequence of steps to perform a data recovery operation?
Which Connectrix FC switch model supports NVMe in a 32Gb/s SAN fabric exclusively?