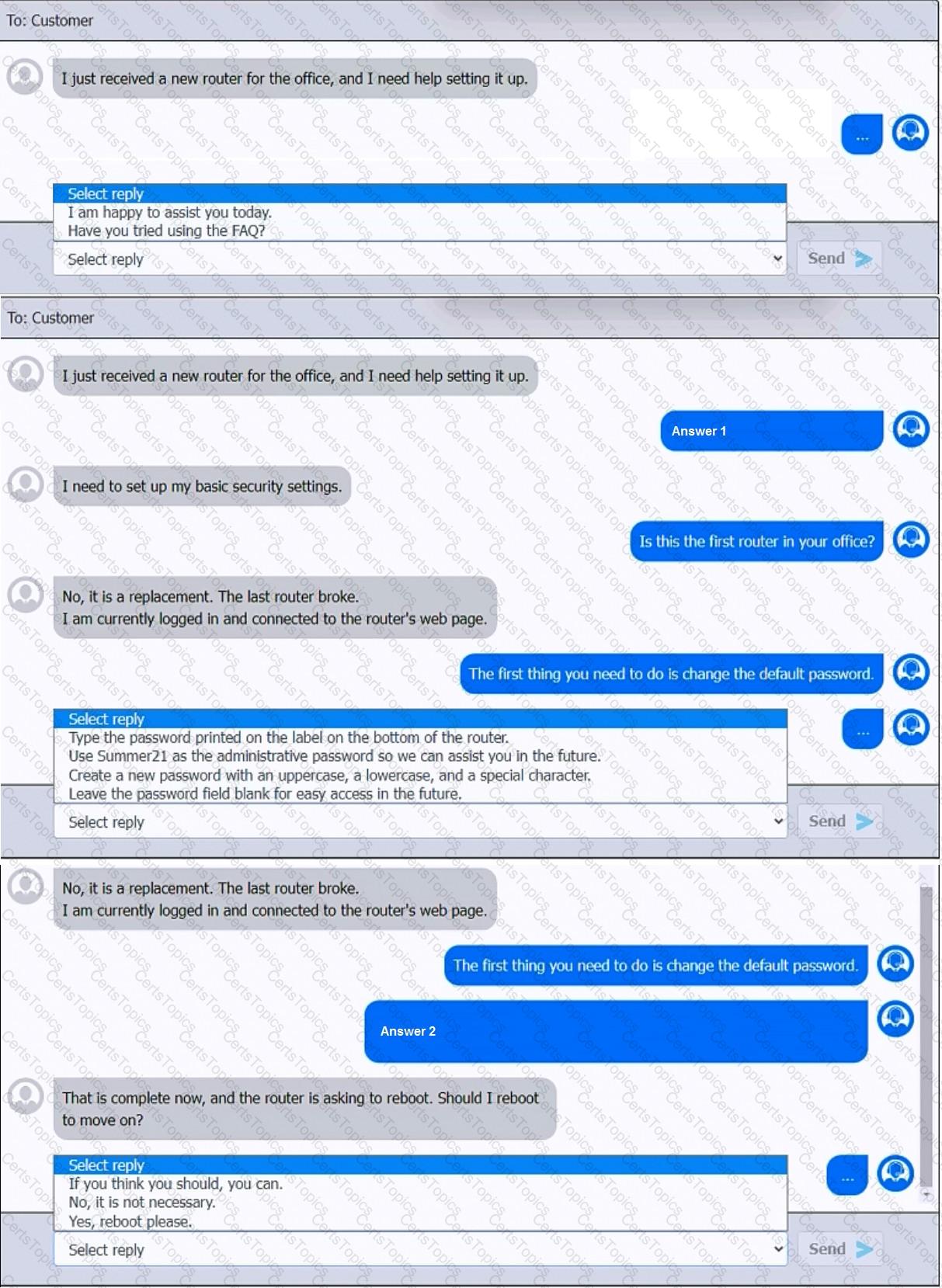
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
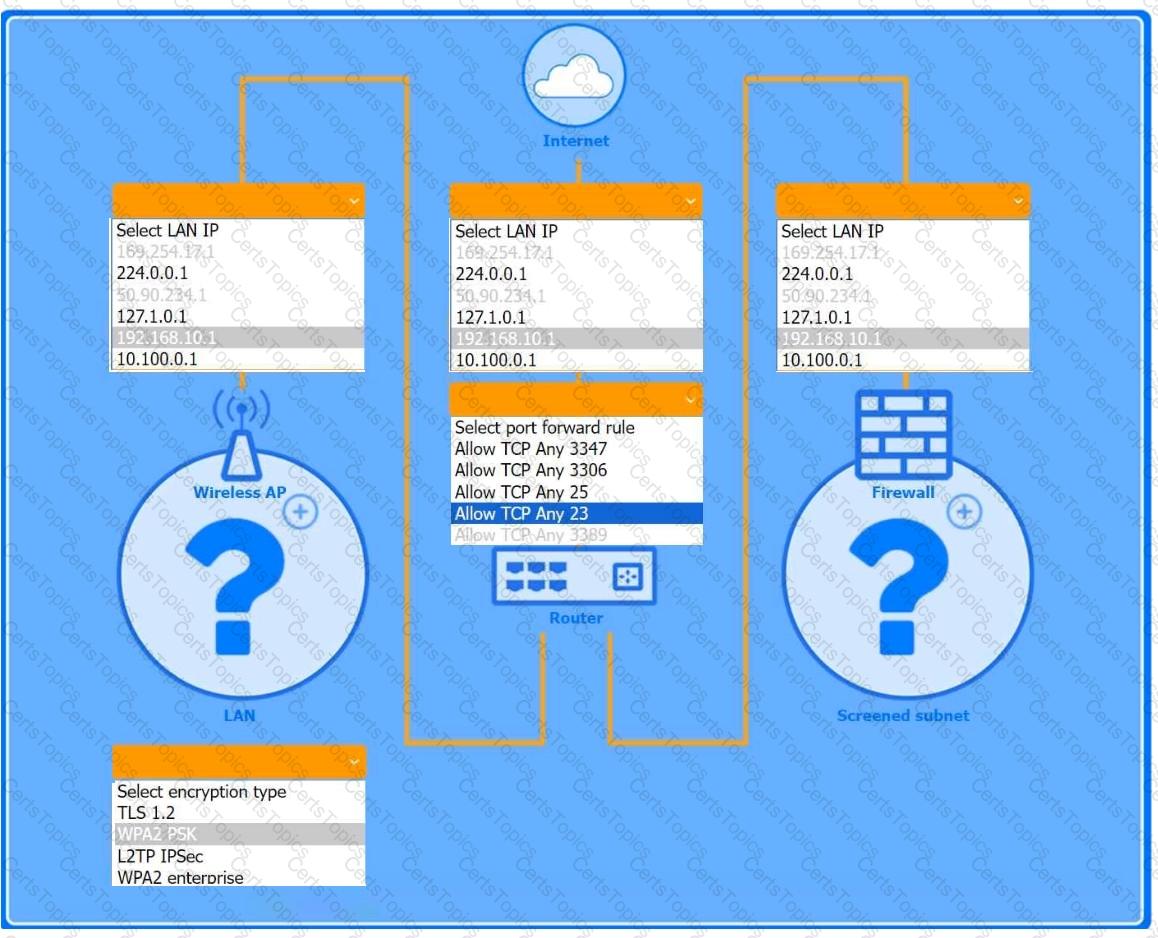
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
Firewall Screened Subnet
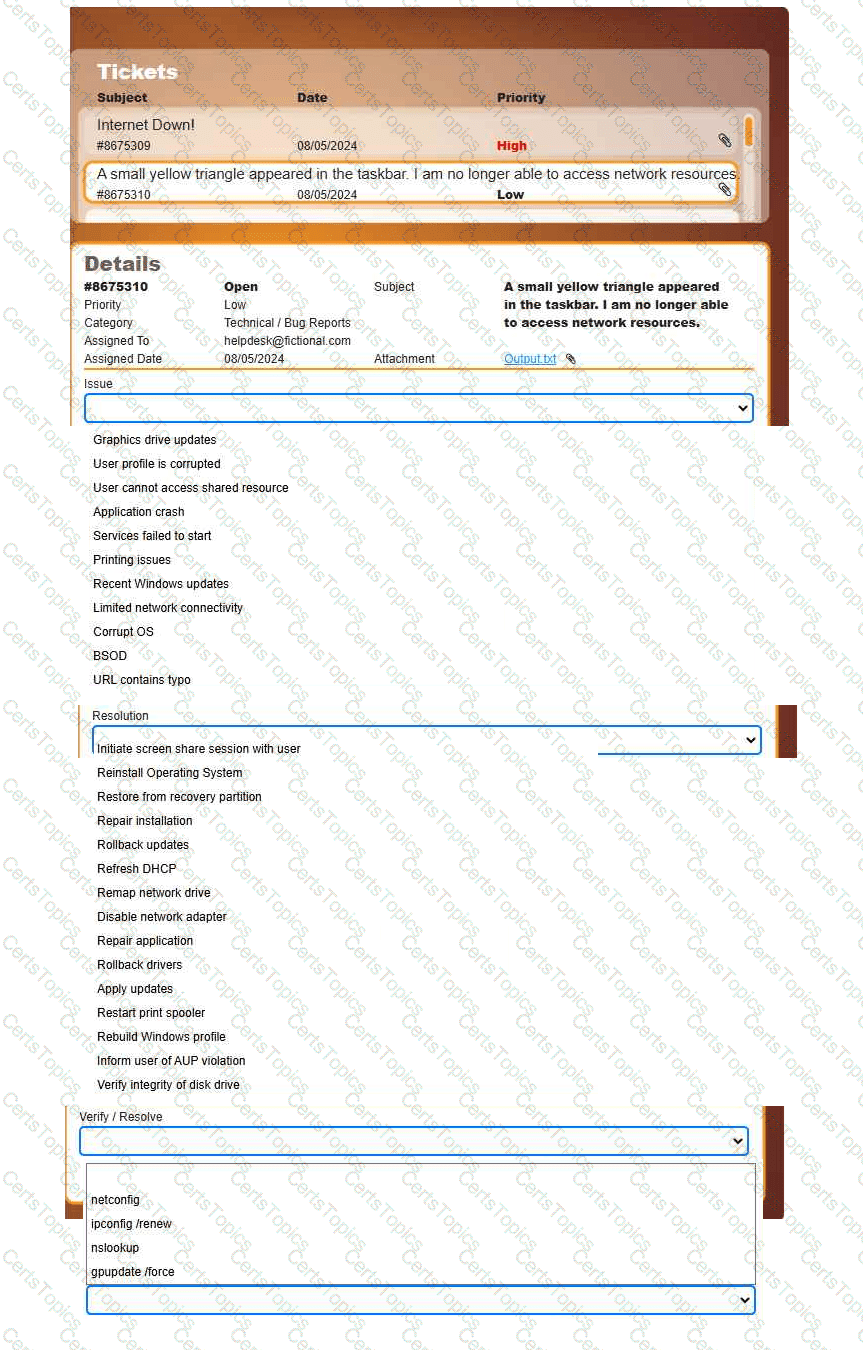
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
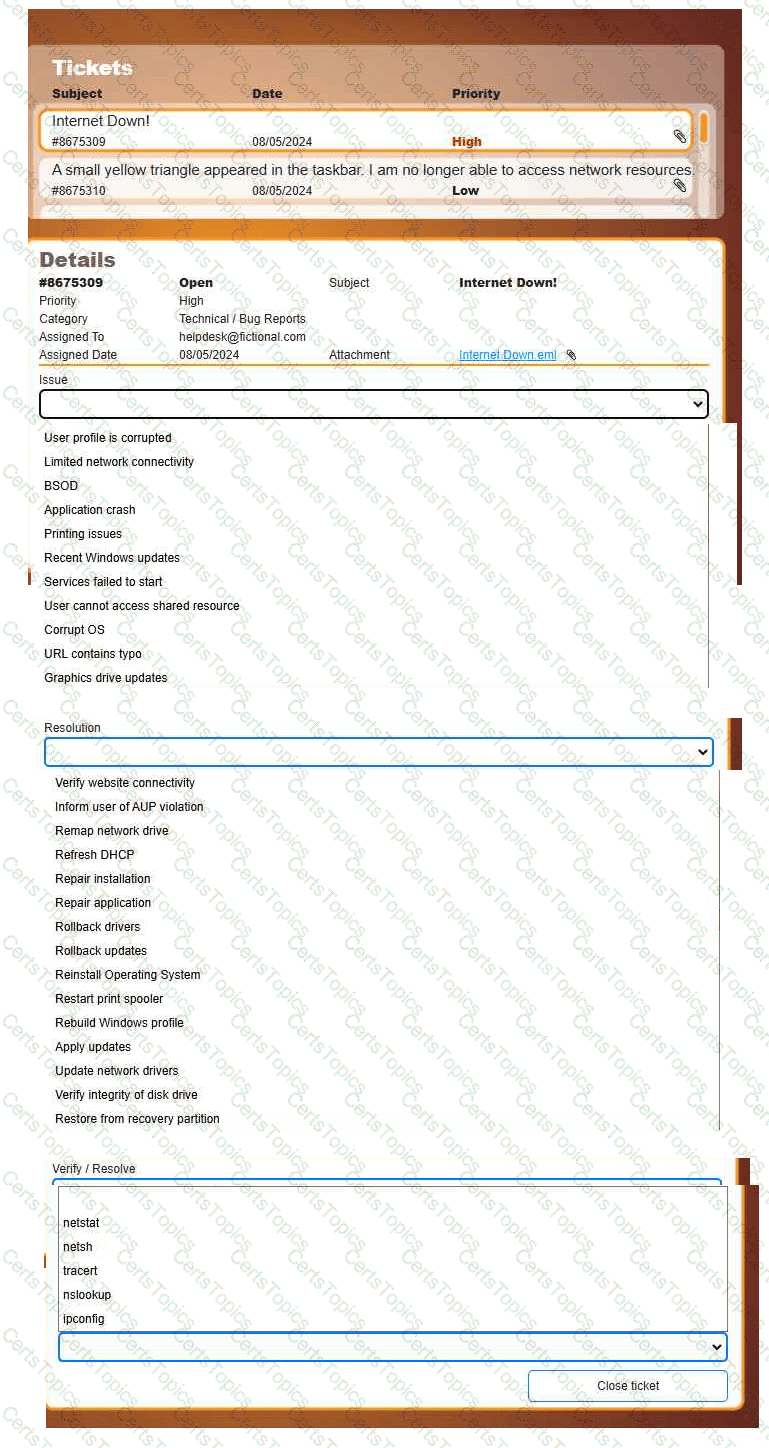
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
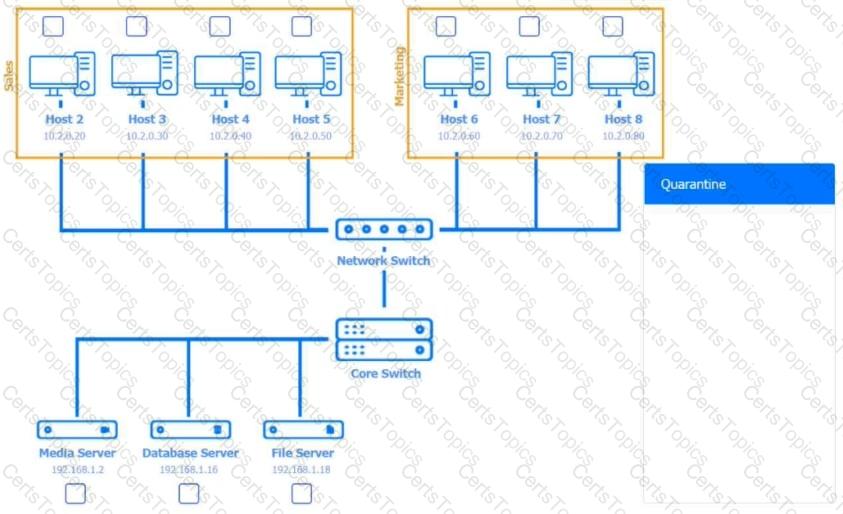
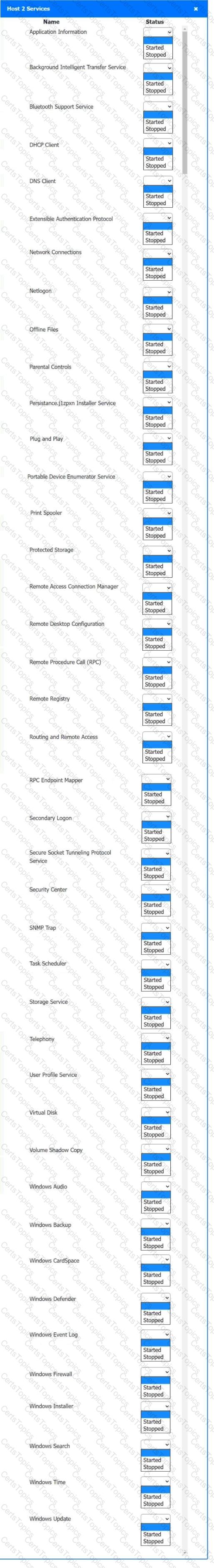
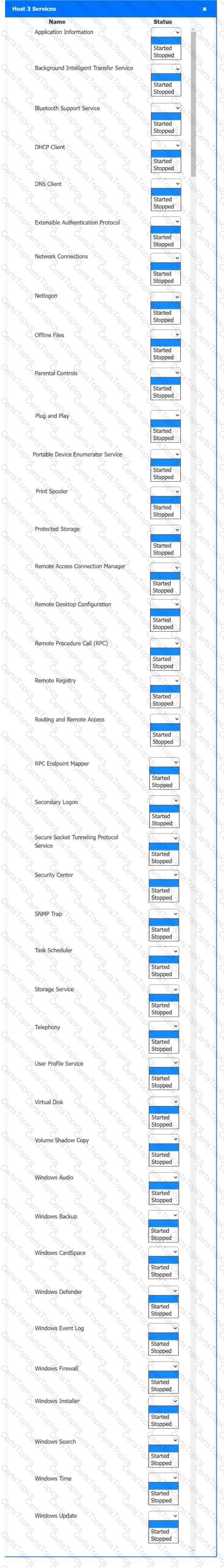
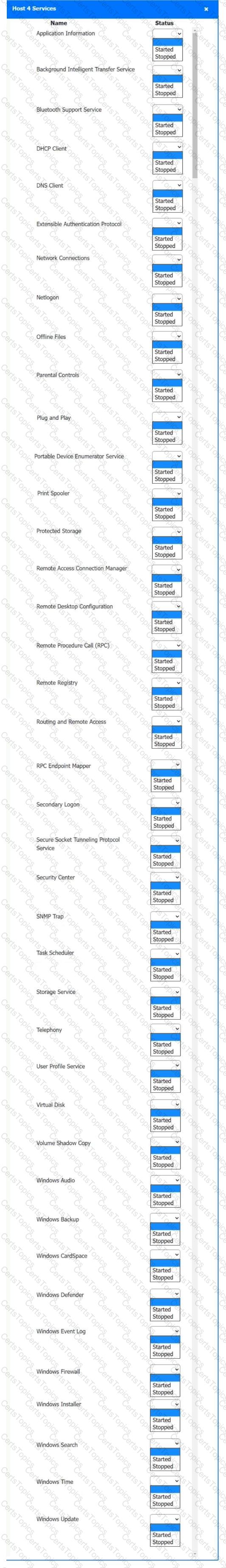
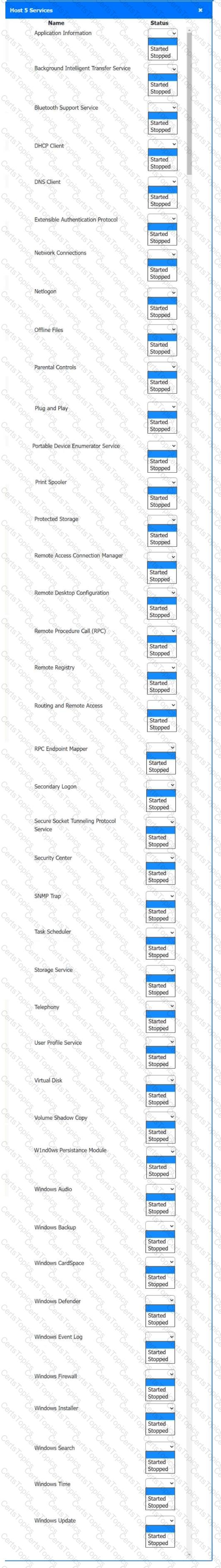
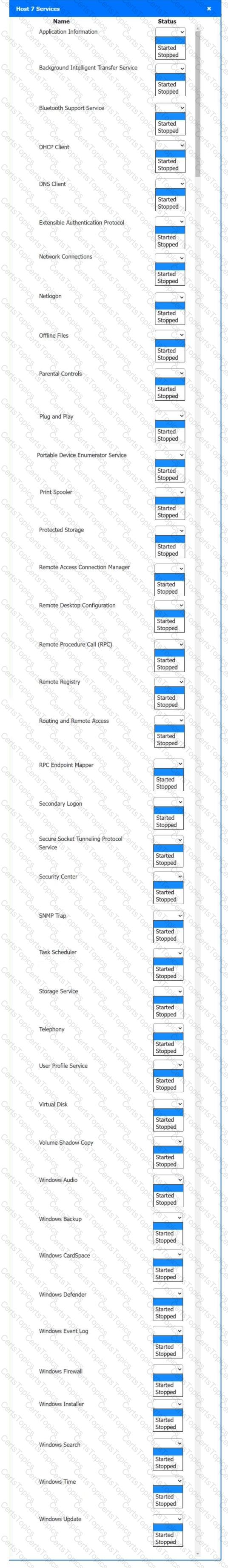
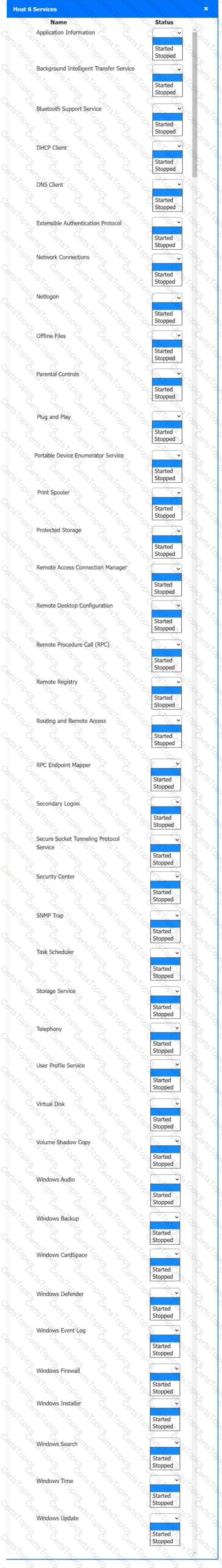
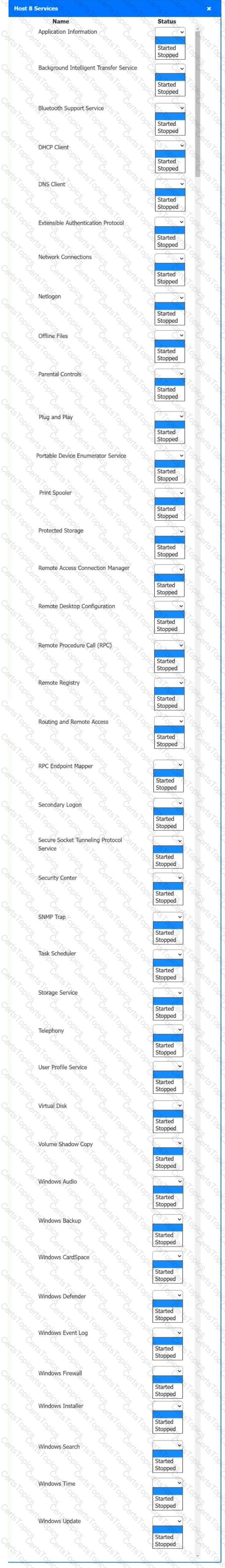
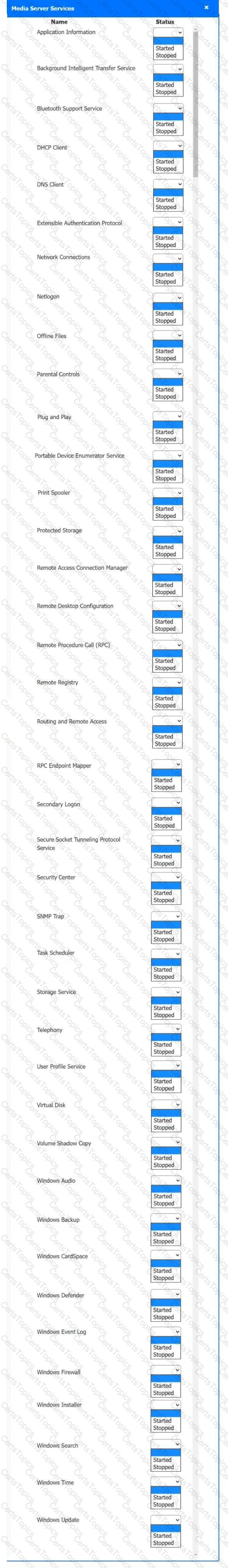
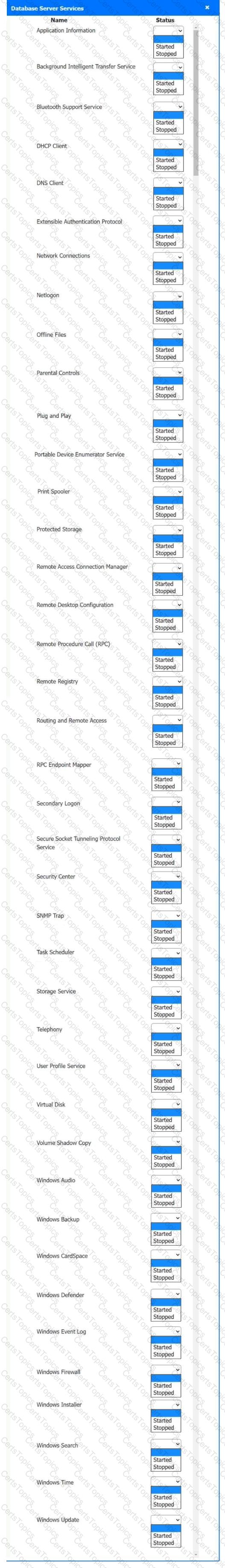
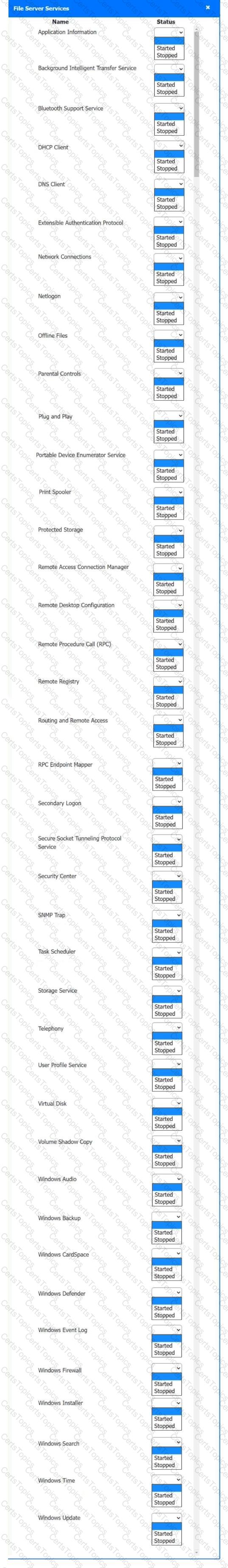
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
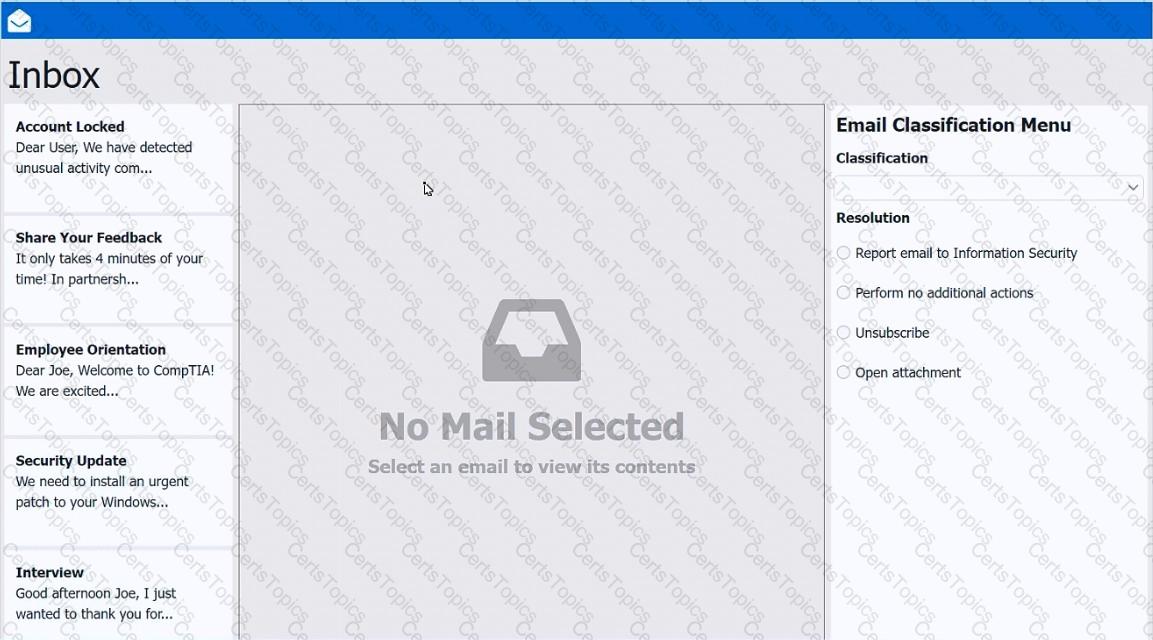
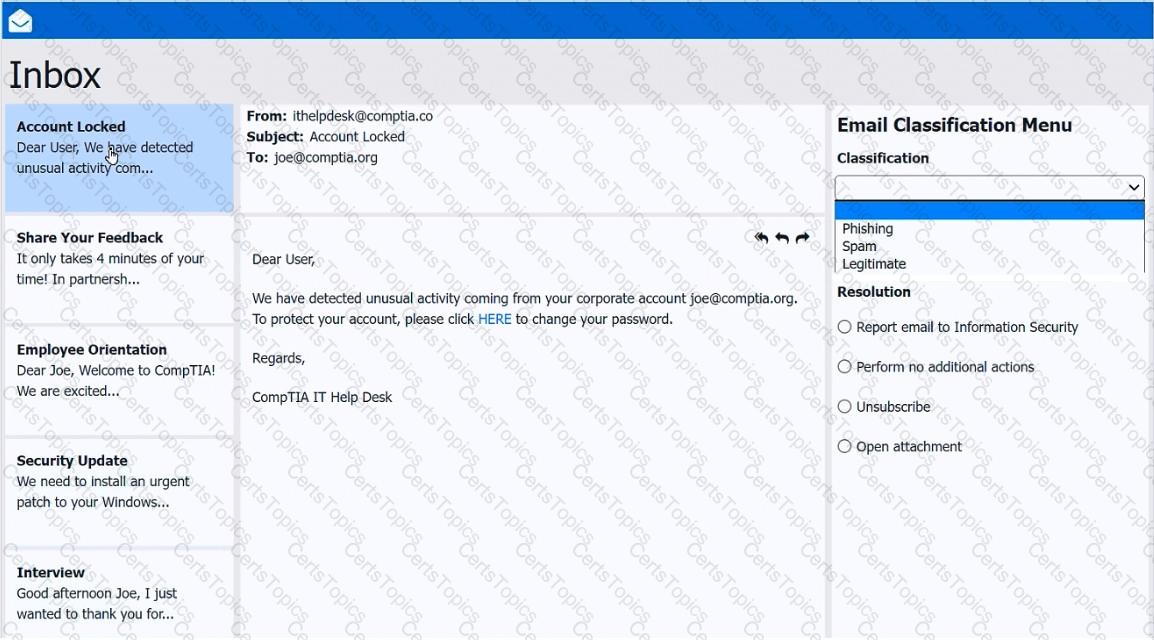
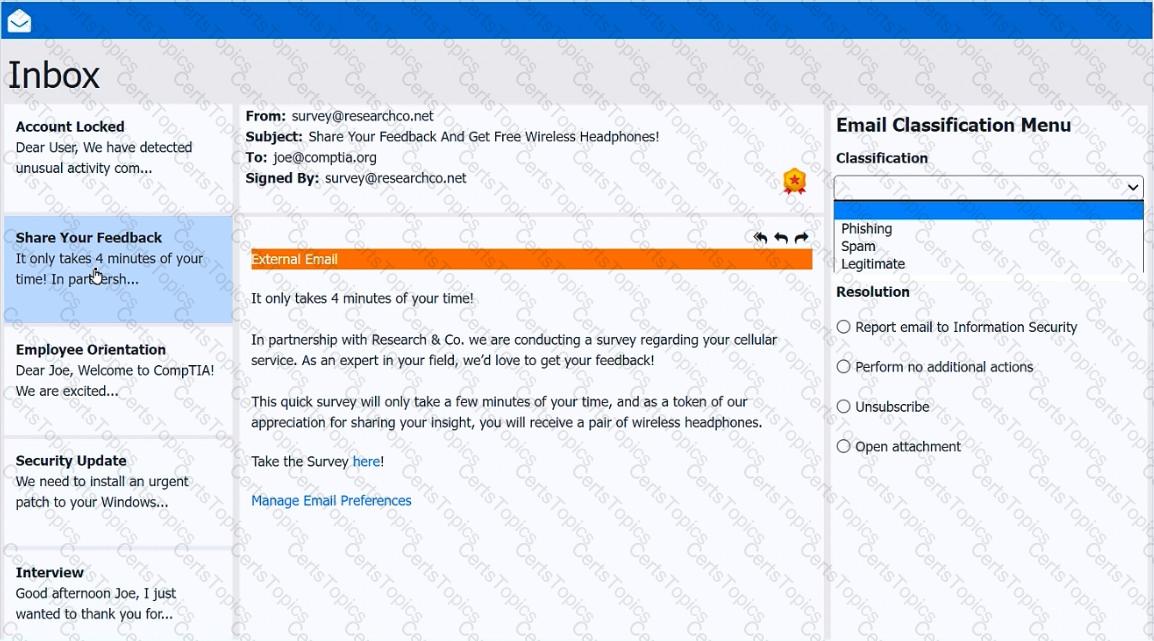
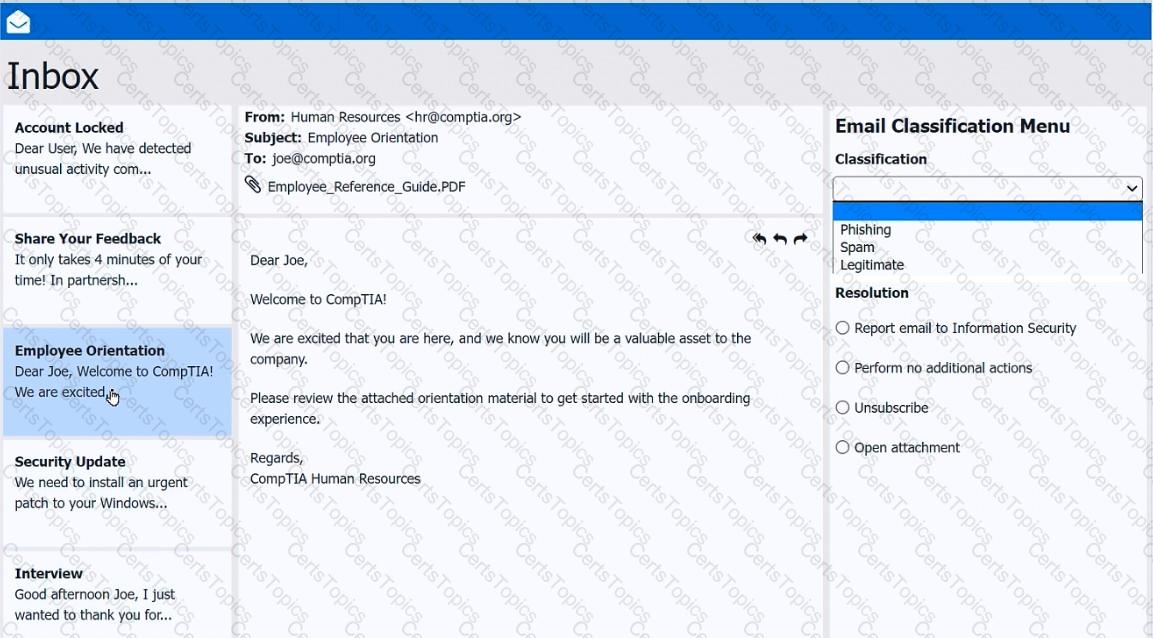
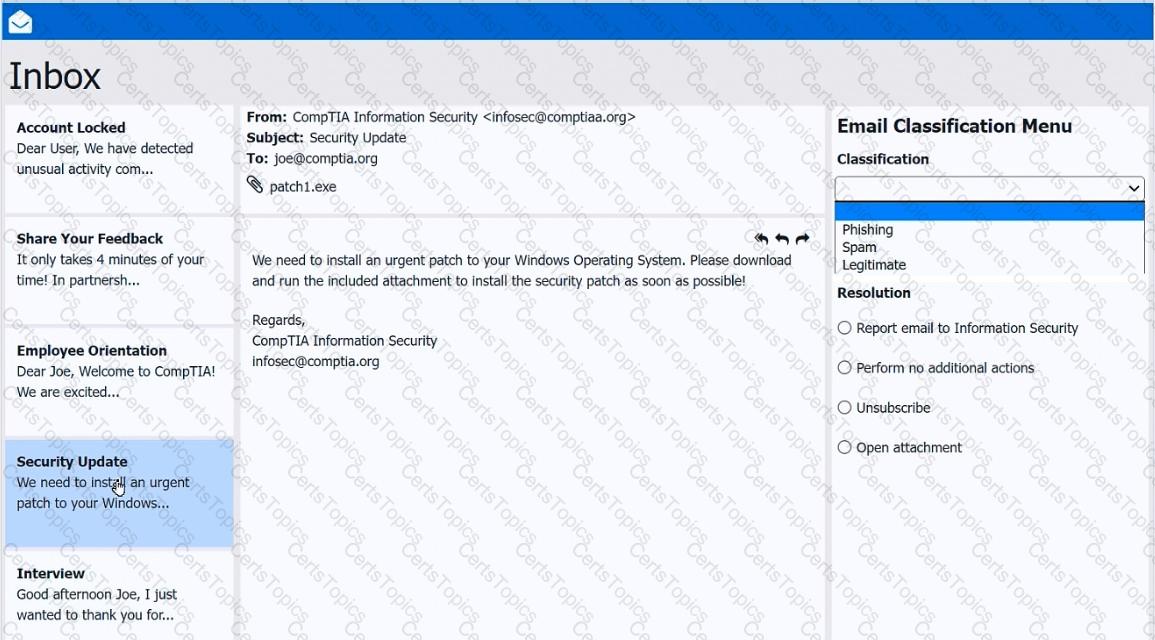
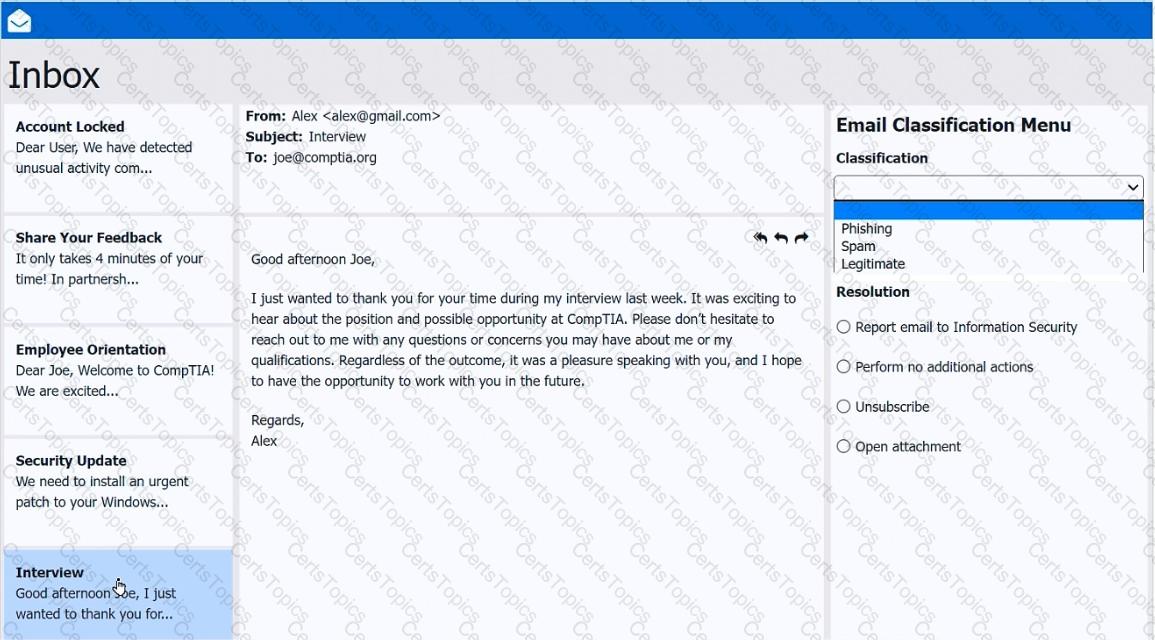
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
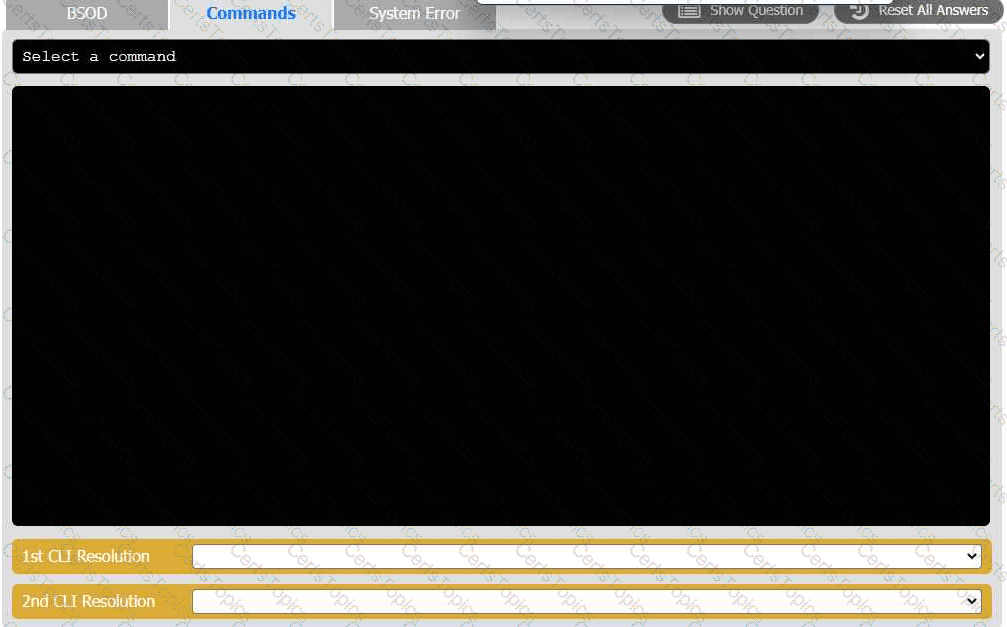
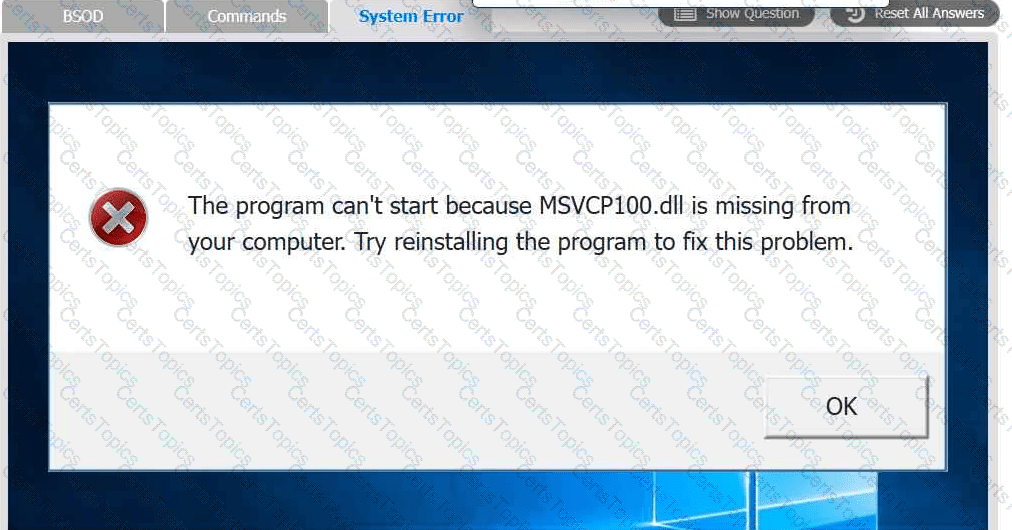
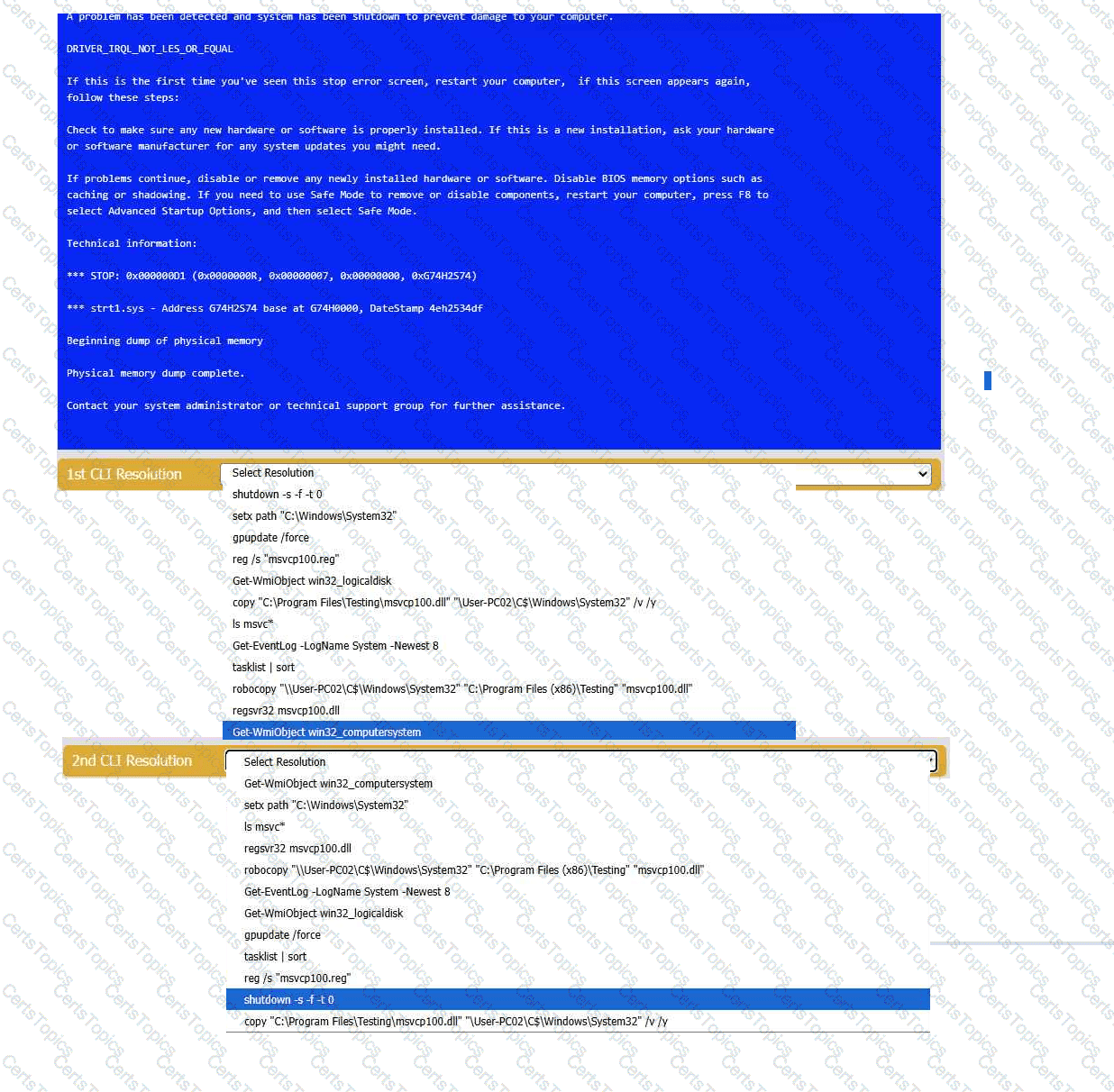
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
A user reports that double-clicking an application ' s shortcut fails to launch the program. A technician believes the application process is running in the background in an unresponsive state. Which of the following tools should the technician use to resolve the issue?
A technician needs to provide remote support for a legacy Linux-based operating system from their Windows laptop. The solution needs to allow the technician to see what the user is doing and provide the ability to interact with the user ' s session. Which of the following remote access technologies would support the use case?
A technician thinks that an application a user downloaded from the internet may not be the legitimate one, even though the name is the same. The technician needs to confirm whether the application is legitimate. Which of the following should the technician do?
A technician is securing a newly deployed workstation. Only authorized users should access it. Which actions should the technician take? (Select two)
A technician is working on a complex, large-scale software deployment. In which of the following places would the technician most likely reference deployment instructions?
A technician wants to create new partitions on a device so that a user can keep work data and personal data separate. Which of the following tools should the technician use?
A Windows 11 Home device is receiving constant pop-ups about an urgent need to update antivirus software to remove a detected threat. The user has been clicking the " X " button in the window frame but it always reappears. The pop-up includes an " OK " button to install the update and remove the threat. Which of the following should the user do next?
A user wants to dispose of a failed hard drive in a way that ensures the data is unrecoverable. Which of the following is the best at-home method?
A technician completes the installation of an OS that appears to be successful. However, when the technician removes the USB drive that was used for the installation and restarts the system, the error “No boot device found” appears. Which of the following should the technician do next to resolve the issue?
A user takes an iOS-based smartphone to a repair shop due to performance issues. The technician observes:
Battery charge: 25%
Battery health: 90%
Hotspot: On
Used space: 63.76GB / 64GB
Which of the following is the most likely cause of the performance issue?
Why would a network engineering team provide a help desk technician with IP addresses for a wired network segment?
Which of the following prevents forced entry into a building?
Which of the following Microsoft Windows versions would most likely be installed on a server?
An administrator is investigating a technical outage. The management team wants information that includes the summary of the outage and actions taken. Which of the following documentation should the administrator provide?
After using a third-party disk optimization software package, a technician restarts a laptop and receives the message " No operating system found. " The technician verifies that the BIOS properly recognizes the SSD. Which of the following should the technician do next?
A user hears an unexpected noise coming from their desktop computer. To troubleshoot the issue, a technician needs to open the case. Which of the following actions should the technician take next?
A user ' s application only works with a legacy version of the OS. The OS is reaching its end-of-life date. For security reasons, the company is migrating to the current version of the OS. Which of the following is the most efficient way to complete the migration while maintaining accessibility to the application?
A technician is setting up a Windows server to allow remote desktop connections for multiple users. Which of the following should the technician configure on the workstation?
A user installed a free application from an unofficial application store. Now, their smartphone displays random pop-ups and shows increased data usage. Additionally, the user cannot perform certain actions such as opening banking applications or updating their OS. Which of the following should the user do first to address the security issues on their smartphone?
Performance on a user’s smartphone is degrading. Applications take a long time to start, and switching between apps is slow. Which of the following diagnostic steps should a mobile technician take first?
A company ' s IT department discovers that unauthorized software has been installed on several workstations. The IT manager requests a review and an update of the workstation security posture, focusing on preventing future unauthorized software installations. Which of the following should the company do?
A utility failure causes a workstation to immediately shut down. Which of the following would help prevent this from reoccurring?
A user needs to test several software replacement possibilities. Part of the process involves installing the different software options on a corporate-imaged sandboxed PC. Which of the following is the best option to allow the user to install the required software?
A user receives a new personal computer but is unable to run an application. An error displays saying that .NET Framework 3.5 is required and not found. Which of the following actions is the best way to resolve this issue?
A technician is troubleshooting a print spooler that fails to start on a Windows 11 desktop computer. The technician determines the root cause is that required dependencies are failing to run. Which of the following tools is the technician using?