CompTIA Related Exams
220-1202 Exam







A user installed a free application from an unofficial application store. Now, their smartphone displays random pop-ups and shows increased data usage. Additionally, the user cannot perform certain actions such as opening banking applications or updating their OS. Which of the following should the user do first to address the security issues on their smartphone?
Which of the following Microsoft Windows versions would most likely be installed on a server?
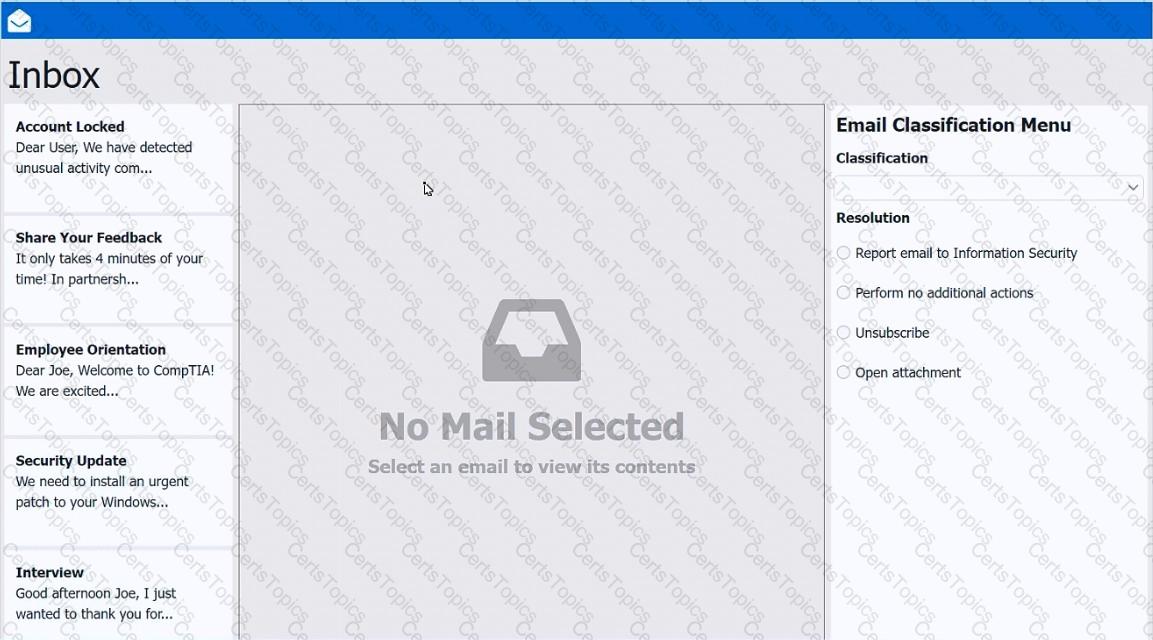
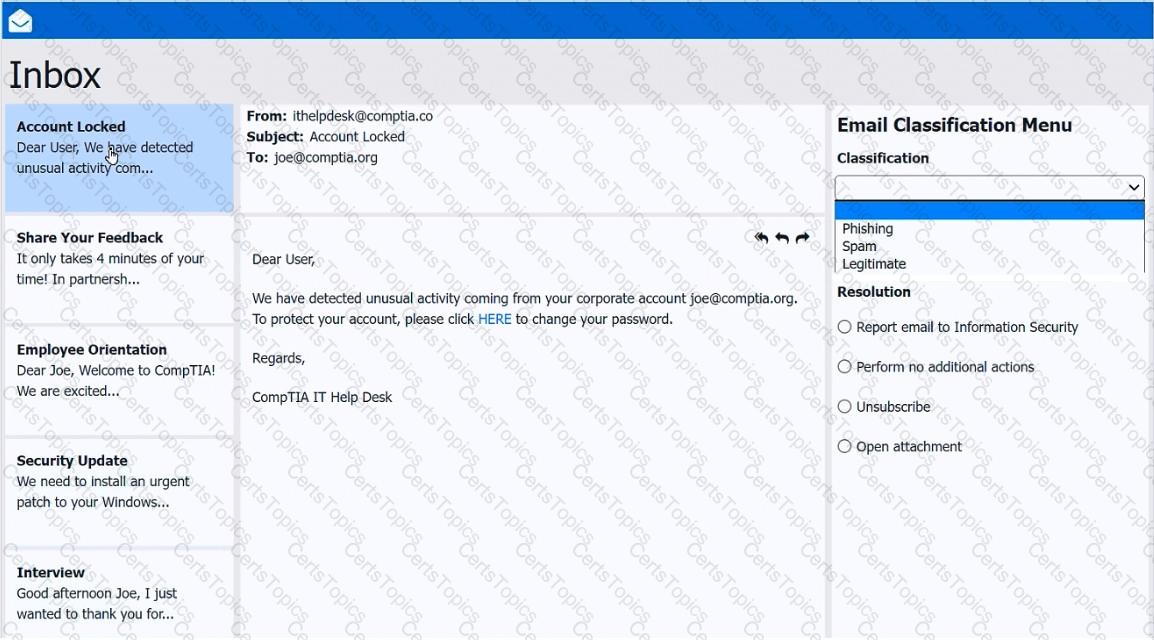
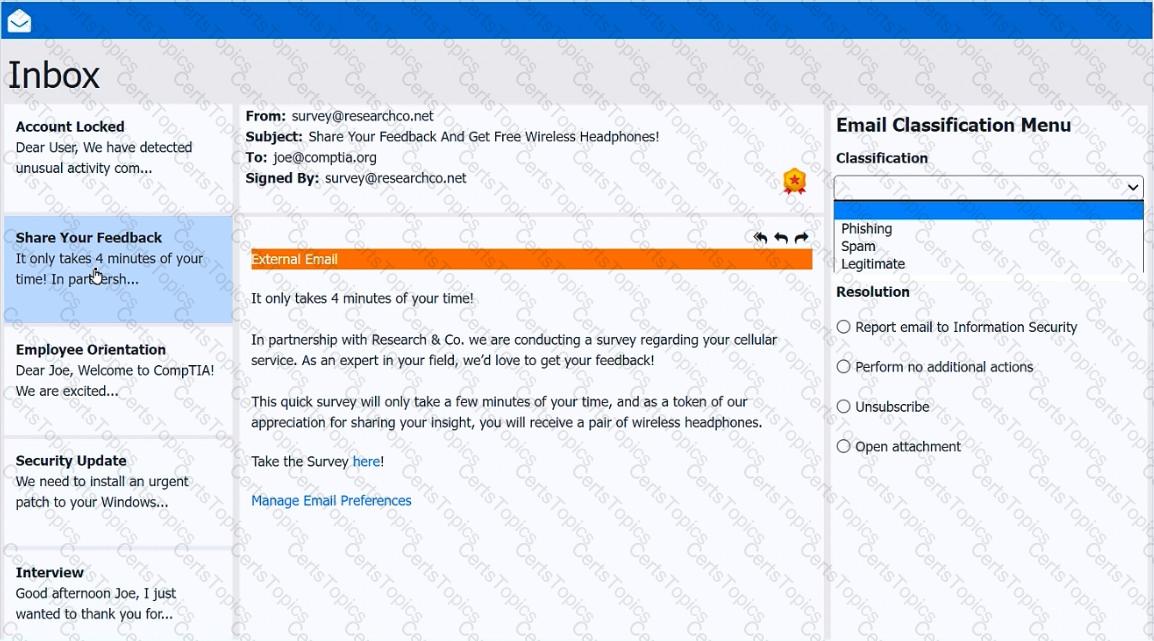
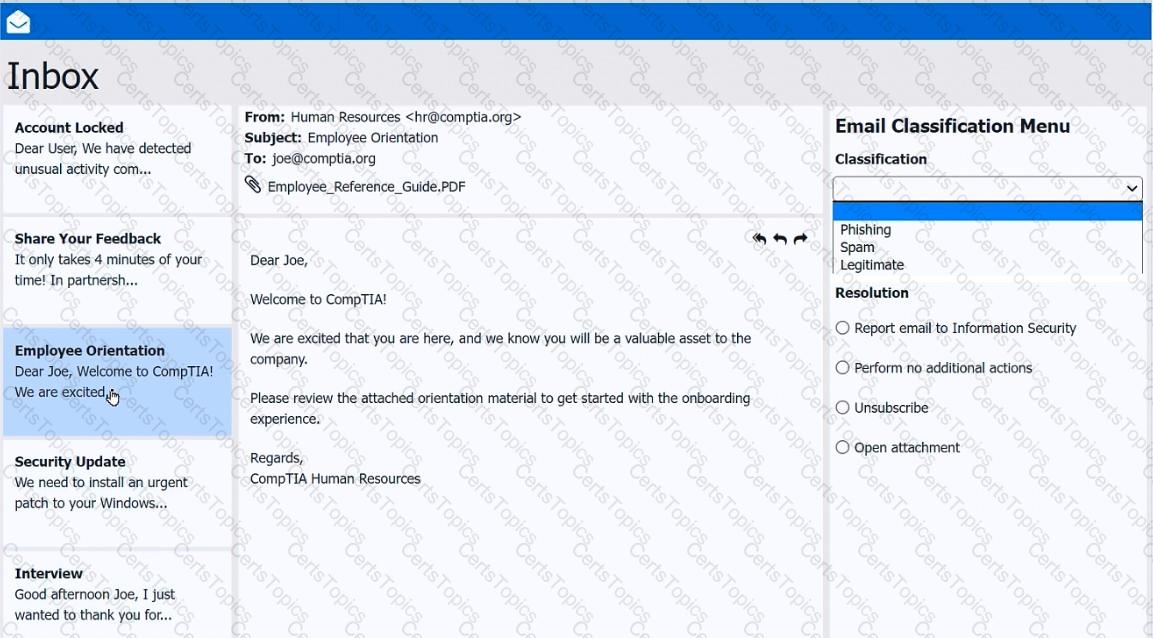
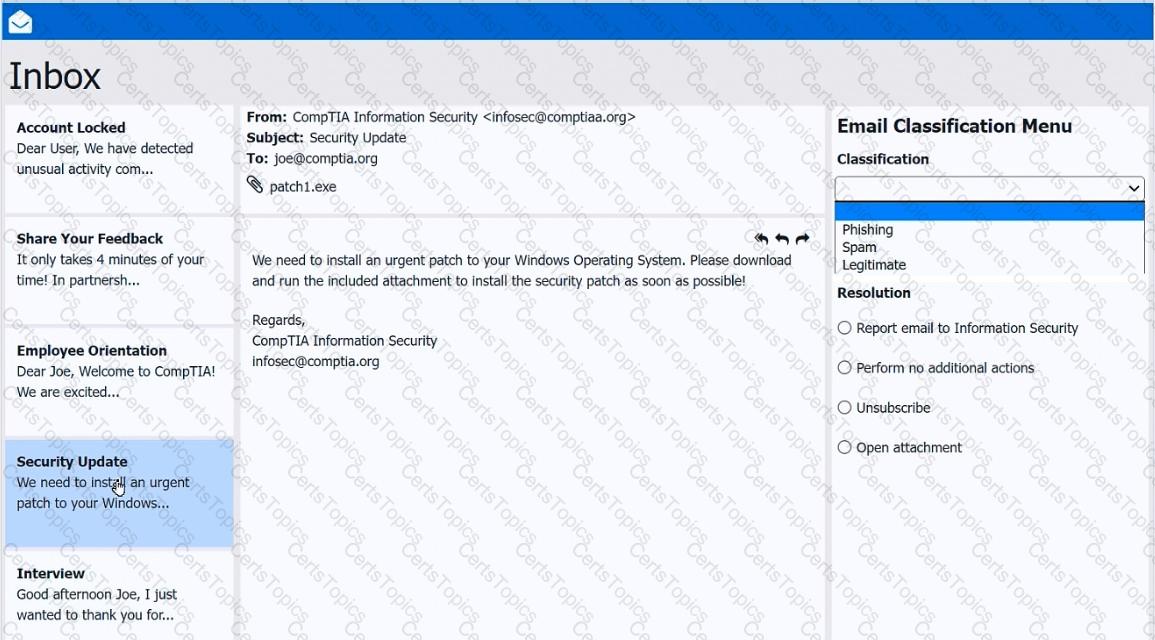
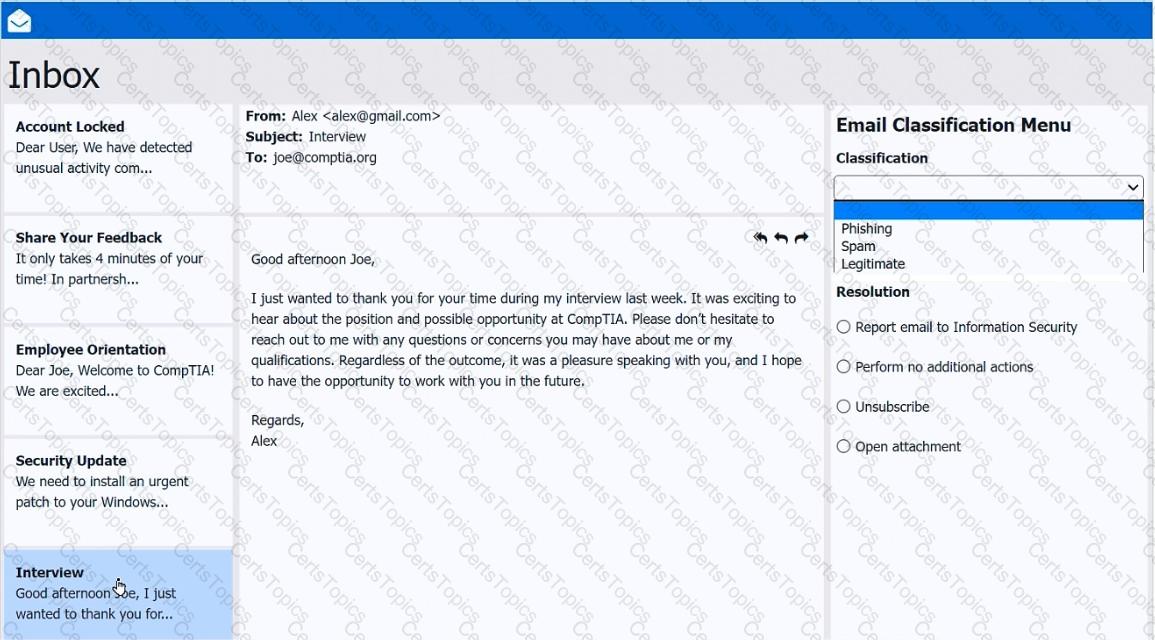
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.