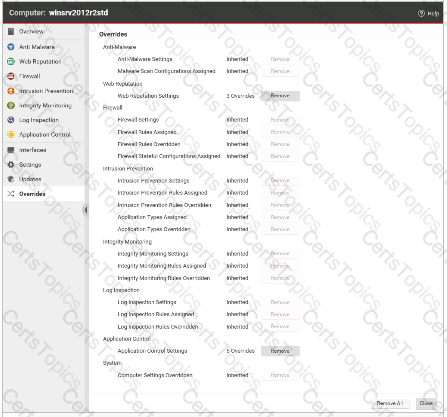
The Overrides settings for a computer are displayed in the exhibit. Which of the following statements is true regarding the displayed configuration?
Which of the following statements is FALSE regarding Firewall rules using the Bypass action?
Which of the following statements is true regarding the use of the Firewall Protection Module in Deep Security?
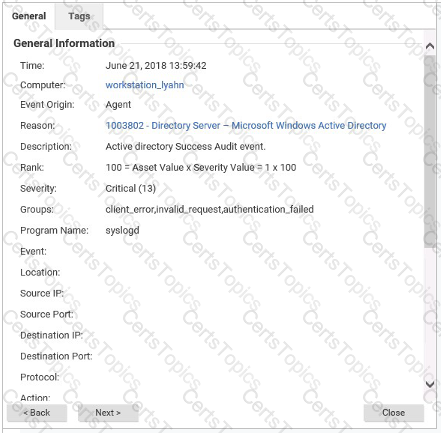
The details for an event are displayed in the exhibit. Based on these details, which Protection Module generated the event?