Which of the following statements are correct about IKE-based SA establishment in IPsec?
Which of the following statements is correct about security zones on a Huawei firewall?
Which of the following protocols is a file transfer protocol?
Which of the following is not included in the Business Impact Analysis (BIA).
At what layer does packet filtering technology in the firewall filter packets?
As shown in the figure, the administrator needs to test the network quality of the 20.0.0/24 CIDR block to the 40.0.0/24 CIDR block on Device B, and the device needs to send large packets for a long time to test the network connectivity and stability.

We should choose the encryption algorithm according to our own use characteristics. When we need to encrypt a large amount of data, it is recommended to use the ____ encryption algorithm to improve the encryption and decryption speed.[fill in the blank]*
Which of the following statements is incorrect about DoS attacks?
The following description of asymmetric encryption algorithms, which item is wrong?
IPSec VPN uses an asymmetric algorithm to calculate the ___ key to encrypt data packets.[fill in the blank]
On a firewall, security policies with the permit action do not need to be configured for traffic between users in the same zone.
The traffic direction of a firewall is based on the zone priority. The _____ direction refers to the direction from a low-priority zone to a high-priority zone. Capitalize the first letter.
Devices that need to provide network services externally, such as WWW servers and FTP servers, can be placed in the DMZ.
Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
Which type of NAT applies to the scenario where there are a small number of Internet access users and the number of public IP addresses is the same as the number of concurrent Internet access users?
Information security aims to protect data in hardware, software, and their systems on information networks to prevent data damage, tampering, or breach due to occasional or malicious reasons and ensure proper system running and non-stop information services.
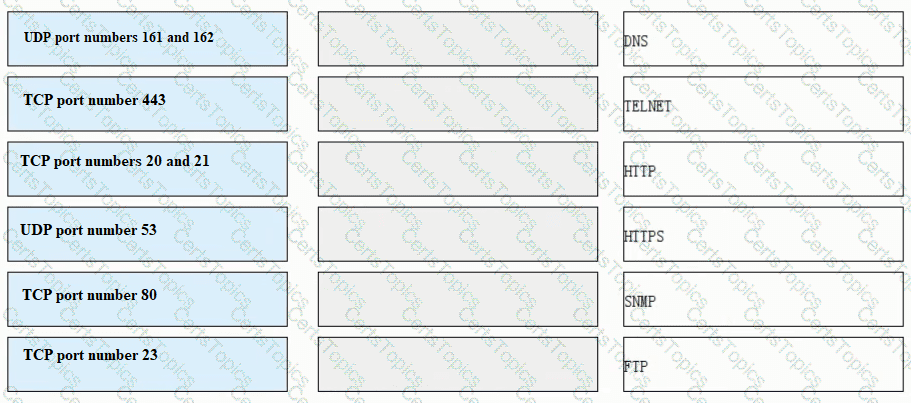
Match each of the following application layer service protocols with the correct transport layer protocols and port numbers.
Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.
Which layer of data packets does a packet filtering firewall check?
Which layer of the protocol stack does SSL provide end-to-end encrypted transmission services?
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
Which of the following authentication modes are supported by AAA?
Which of the following is not a type of Windows log event?
Which security zone can be deleted and its priority can be reconfigured?
For which of the following parameters can the packet filtering firewall filter?
The following description of IDS, which items are correct
The IDS cannot be linked to the firewall.
Drag the phases of the cybersecurity emergency response on the left into the box on the right, and arrange them from top to bottom in the order of execution. 1. Inhibition stage, 2. recovery phase, 3. Detection stage, 4. eradication phase[fill in the blank]*
Which of the following descriptions about the main implementation of single sign-on is wrong?
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
The following description of investigation and evidence collection, which one is correct
ARP man-in-the-middle attacks are a type of spoofing attack technique.
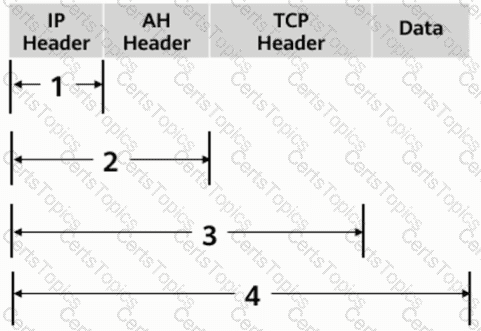
As shown, in transmission mode, which of the following locations should the AH header be inserted in?
When IKEv1 negotiation phase 1 uses the aggressive mode, only three messages are used. Which of the following is the function of message 3?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
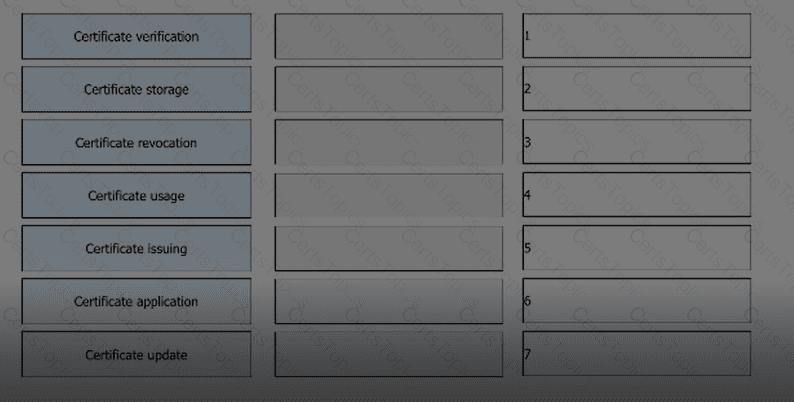
Arrange the following processes in the correct order based on the PKI lifecycle.
Among the various aspects of the risk assessment of IS027001, which of the following does not belong to the system design and release process?
Which of the following statements are correct about the status of the firewall VGMP group?
A three-way handshake is required to establish a TCP connection, and a four-way handshake is required to end a TCP connection.
Match the following single-packet attack types with their corresponding descriptions.

IPS signatures describe the characteristics of attack behaviors on the network. The firewall detects and defends against attacks by comparing data flows with IPS signatures.
What are the correct entries in the following description of firewall security zones?
In cases where some configurations alter existing session table entries and want them to take effect immediately, you can regenerate the session table by clearing the session table information. All session table information can be cleared by executing the _____firewall session table command.
The following description of the intrusion fire protection system IPS, which is correct?
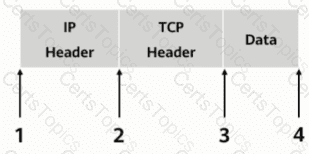
As shown in the figure, what is the range of the AH protocol authentication range in transmission mode?