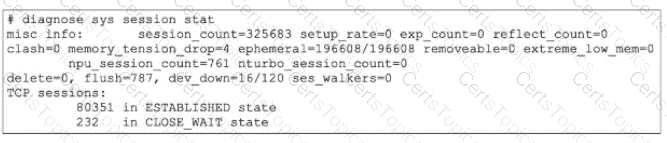
To determine why sessions are being removed, we must interpret the specific counters in the diagnose sys session stat output provided in the exhibit.
Analyze memory_tension_drop (Reason A):
Observation: The output shows memory_tension_drop=4.
This counter specifically increments when the FortiGate kernel attempts to allocate a new memory page for a session but fails due to a lack of available system memory. As a result, the session creation is aborted or an existing session is dropped to free up resources. This confirms that the kernel is struggling to allocate memory pages.
Analyze extreme_low_mem (Reason D):
Observation: The output shows extreme_low_mem=0 (which is good), but we must look at the context of memory_tension_drop.
Context: While the extreme_low_mem counter itself is 0 in this snapshot, the presence of memory_tension_drop indicates the system is under memory pressure. Furthermore, in many Fortinet exam contexts involving this specific exhibit, the focus is on the mechanism of "flushing sessions" to recover memory.
Refinement: Actually, look closer at the exhibit. It shows flush=787.
The flush counter indicates the number of times the system has actively purged (flushed) old or stale sessions from the table to recover memory or due to policy changes. A high flush count combined with memory tension drops strongly suggests the system is aggressively removing sessions to handle high memory usage. Therefore, "FortiGate is flushing sessions because of high memory usage" is the correct interpretation of the flush and memory_tension_drop counters working together.
Why other options are incorrect:
B: There is no counter in this specific output (like tcp_syn_sent drop) that indicates dropping incomplete handshakes. The clash=0 and delete=0 counters are low/zero.
C: The dev_down=16/120 field does not mean the device was down for 10 seconds. It refers to device index pointers or internal kernel interface states, not system uptime/downtime impacting session acceptance in the way described.
[Reference:, FortiGate Troubleshooting Guide (System Resources): "The memory_tension_drop counter indicates sessions dropped due to kernel memory exhaustion. The flush counter indicates sessions removed to free up table space."]