A vulnerability scan of a web server that is exposed to the internet was recently completed. A security analyst is reviewing the resulting vector strings:
Vulnerability 1: CVSS: 3.0/AV:N/AC: L/PR: N/UI : N/S: U/C: H/I : L/A:L
Vulnerability 2: CVSS: 3.0/AV: L/AC: H/PR:N/UI : N/S: U/C: L/I : L/A: H
Vulnerability 3: CVSS: 3.0/AV:A/AC: H/PR: L/UI : R/S: U/C: L/I : H/A:L
Vulnerability 4: CVSS: 3.0/AV: P/AC: L/PR: H/UI : N/S: U/C: H/I:N/A:L
Which of the following vulnerabilities should be patched first?
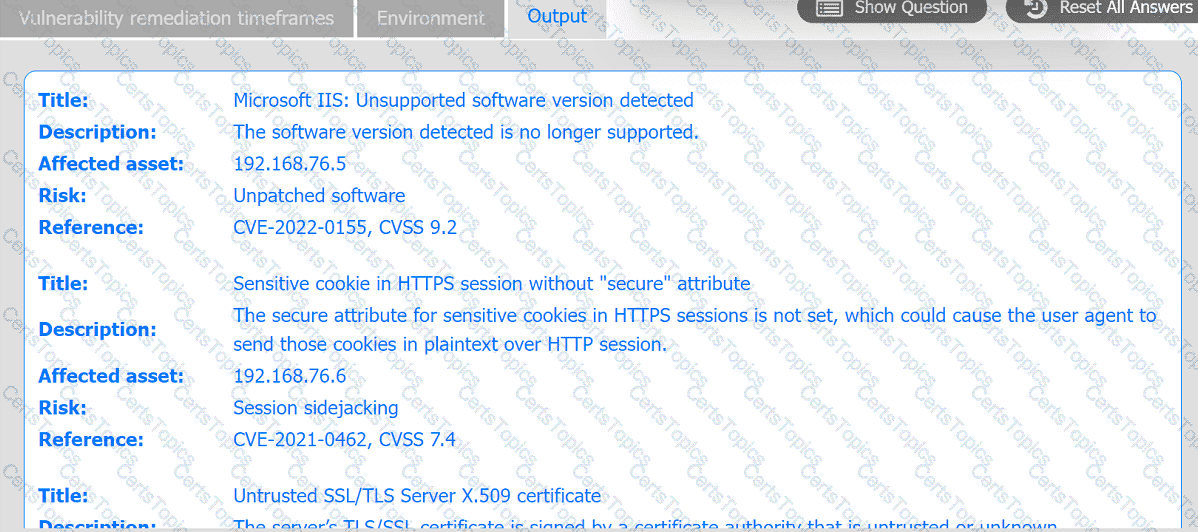
A systems administrator is reviewing the output of a vulnerability scan.
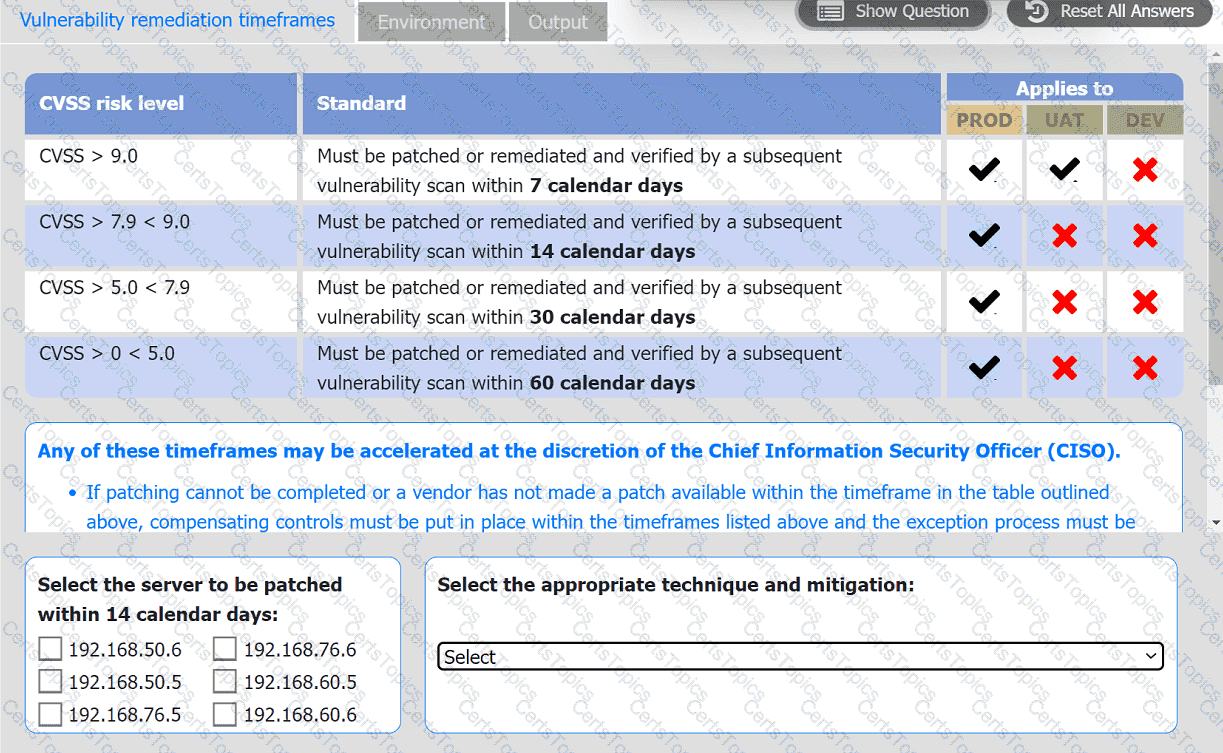
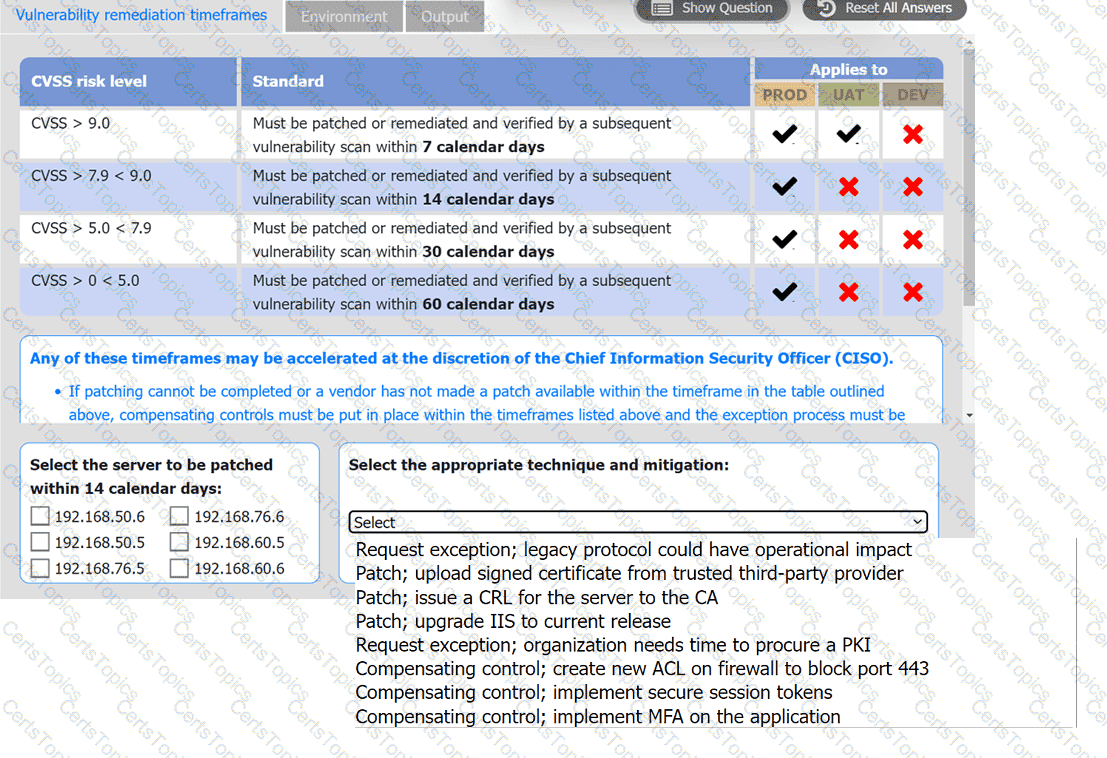
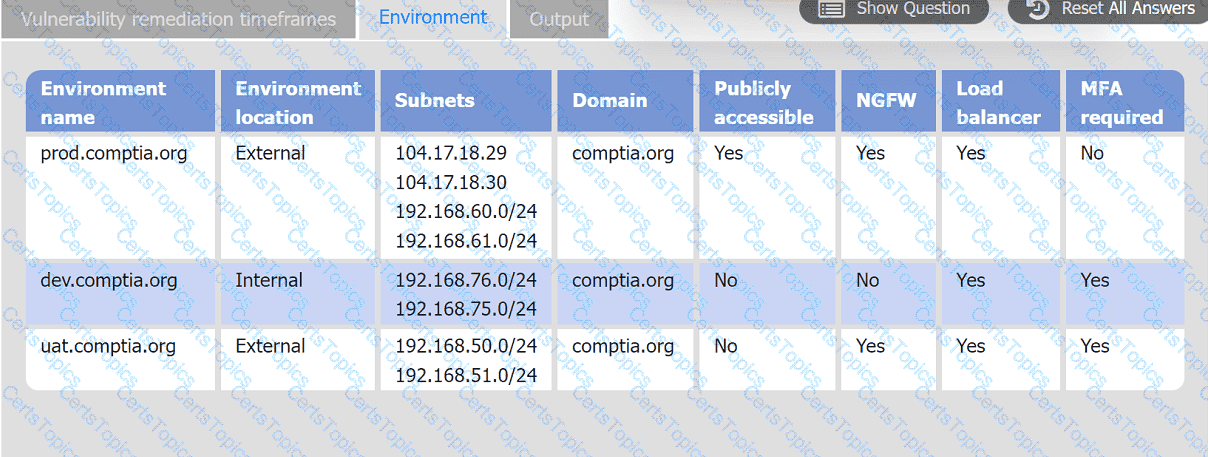
INSTRUCTIONS
Review the information in each tab.
Based on the organization ' s environment architecture and remediation standards,
select the server to be patched within 14 days and select the appropriate technique
and mitigation.
A penetration tester is conducting a test on an organization ' s software development website. The penetration tester sends the following request to the web interface:
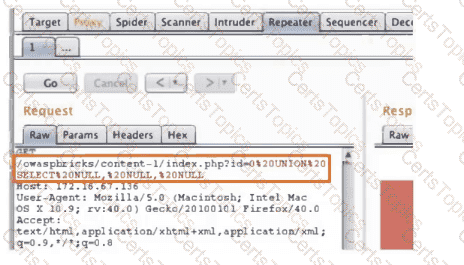
Which of the following exploits is most likely being attempted?
An analyst is reviewing a vulnerability report for a server environment with the following entries:
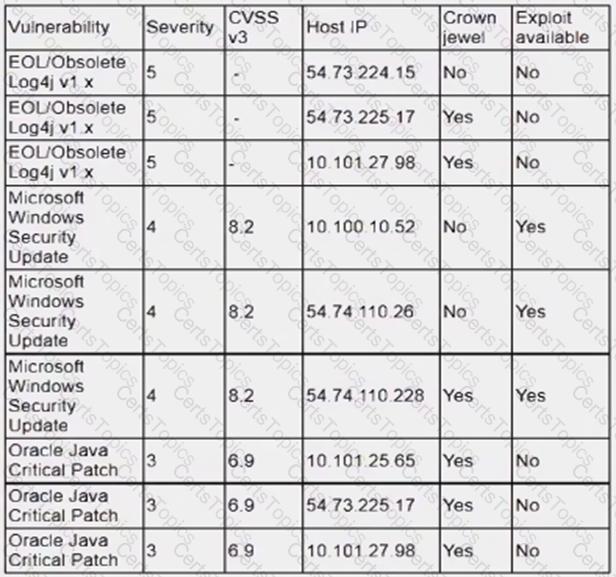
Which of the following systems should be prioritized for patching first?