Fortinet Related Exams
NSE6_FML-6.4 Exam







Refer to the exhibit.
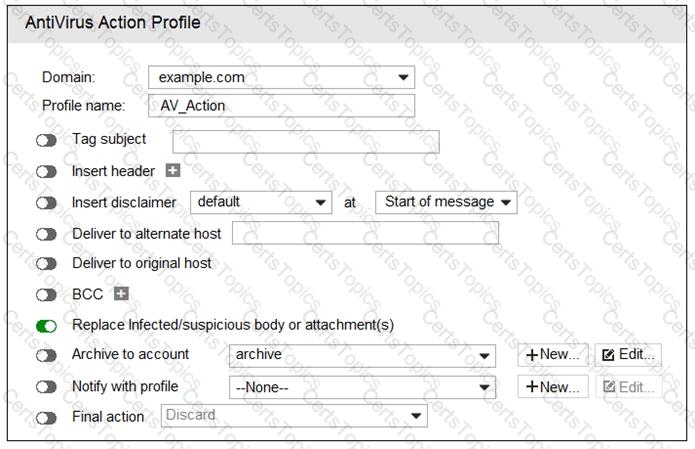
What are two expected outcomes if FortiMail applies this antivirus action profile to an email? (Choose two.)
Examine the FortiMail recipient-based policy shown in the exhibit; then answer the question below.
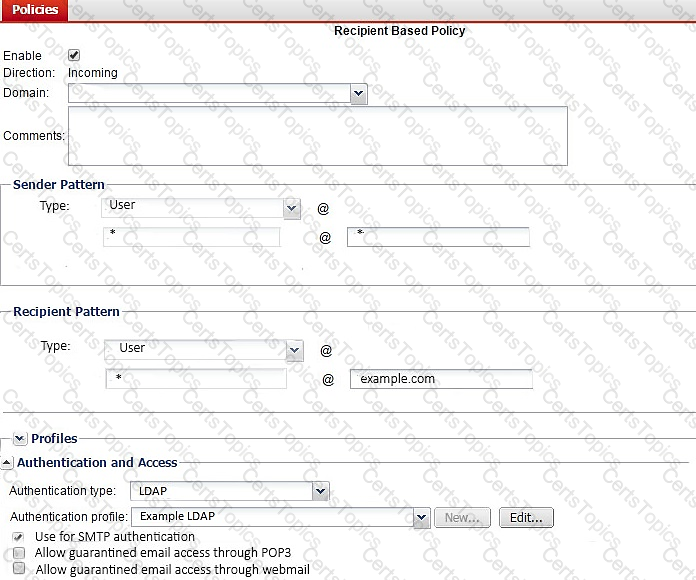
After creating the policy, an administrator discovered that clients are able to send unauthenticated email using SMTP. What must be done to ensure clients cannot send unauthenticated email?
A FortiMail administrator is concerned about cyber criminals attempting to get sensitive information from employees using whaling phishing attacks.
What option can the administrator configure to prevent these types of attacks?