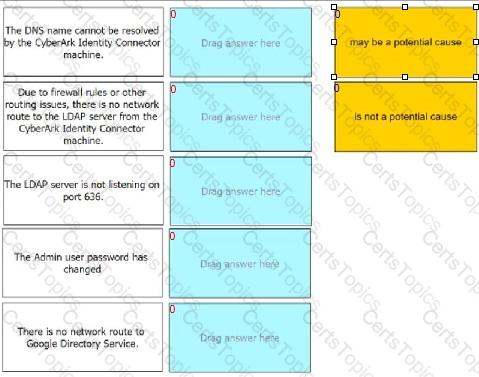
For each statement listed, indicate if it may be a potential cause of this problem.
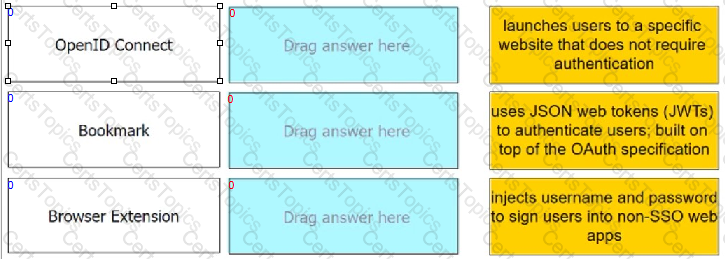
Match each Web App Connector to the phrase that best describes its service offering.
Which statement is true about the app gateway?
ACME Corporation employees access critical business web applications through CyberArk Identity. You notice a constant high volume of unauthorized traffic from 103.1.200.0/24 trying to gain access to the CyberArk Identity portal. Access to the CyberArk Identity portal is time sensitive. ACME decides to enforce IP restrictions to reduce vulnerability.
Which configuration can help achieve this?
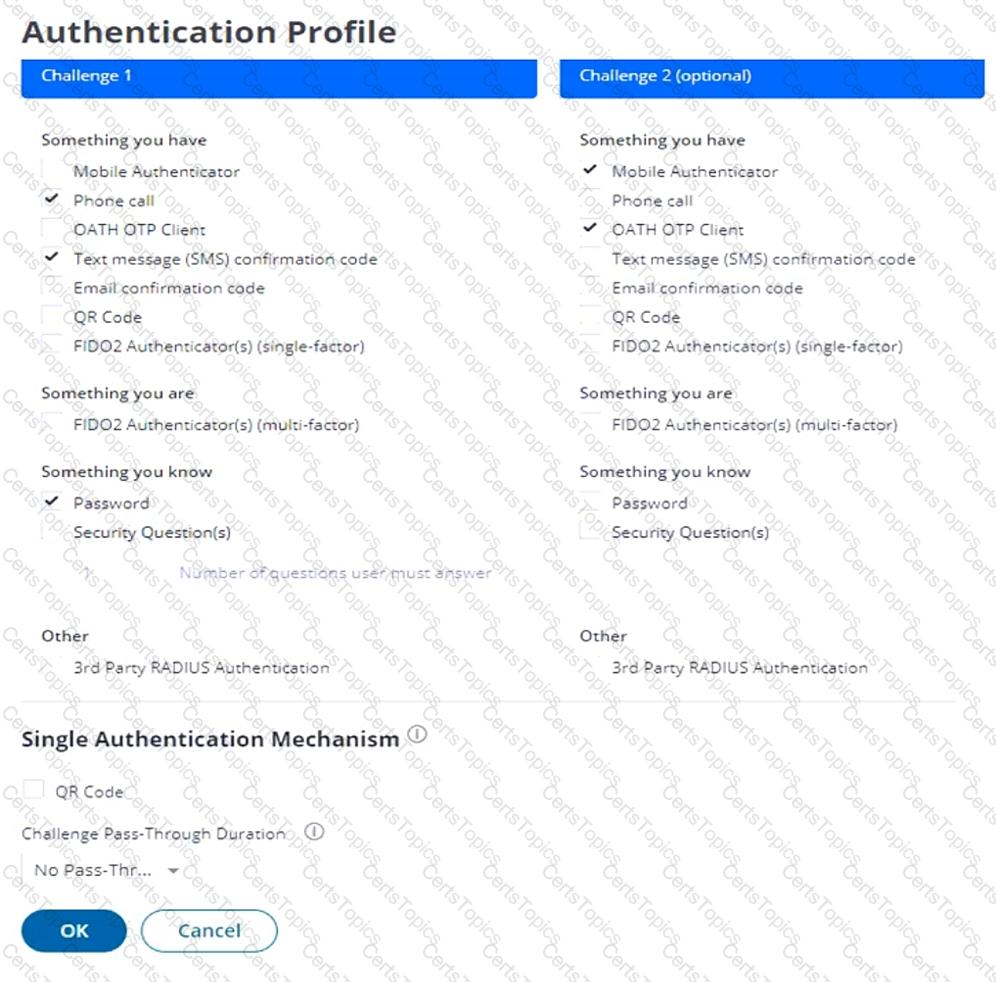
Refer to the exhibit.
This exhibit shows the base authentication policy for ACME Corporation. You must edit the policy to allow users to authenticate once if they fulfill certain authentication criteria.
How should you configure this policy to support BOTH?
Within a Web App connector, which feature does an admin use to grant users access?
Which device enrollment settings are valid? (Choose two.)
What is considered an "Identity Provider Initiated" login to an application?
Your team is deploying endpoint authentication onto the corporate endpoints within an organization. Enrollment details include when the enrollment must be completed, and the enrollment code was sent out to the users. Enrollment can be performed in the office or remotely (without the assistance of an IT support engineer). You received feedback that many users are unable to enroll into the system using the enrollment code.
What can you do to resolve this? (Choose two.)
You get the following error: "Not Authorized. You do not have permission to access this feature".
What is most likely the cause of the error?
Which settings can help minimize the number of 2FA / MFA prompts? (Choose two.)
You are tasked to enforce certificate based authentication onto all the domain-joined Windows machines within your organization. Based on the inventory record, there are 1000 Windows machines, which include 150 standalone Windows machines. The enrollment will be conducted from either the office network or through the Virtual Private Network (VPN).
Which parameter(s) should you define within the enrollment code to ensure the security of the code and that only the authorized endpoints get registered?
Where can you download the CyberArk Identity mobile app? (Choose two.)
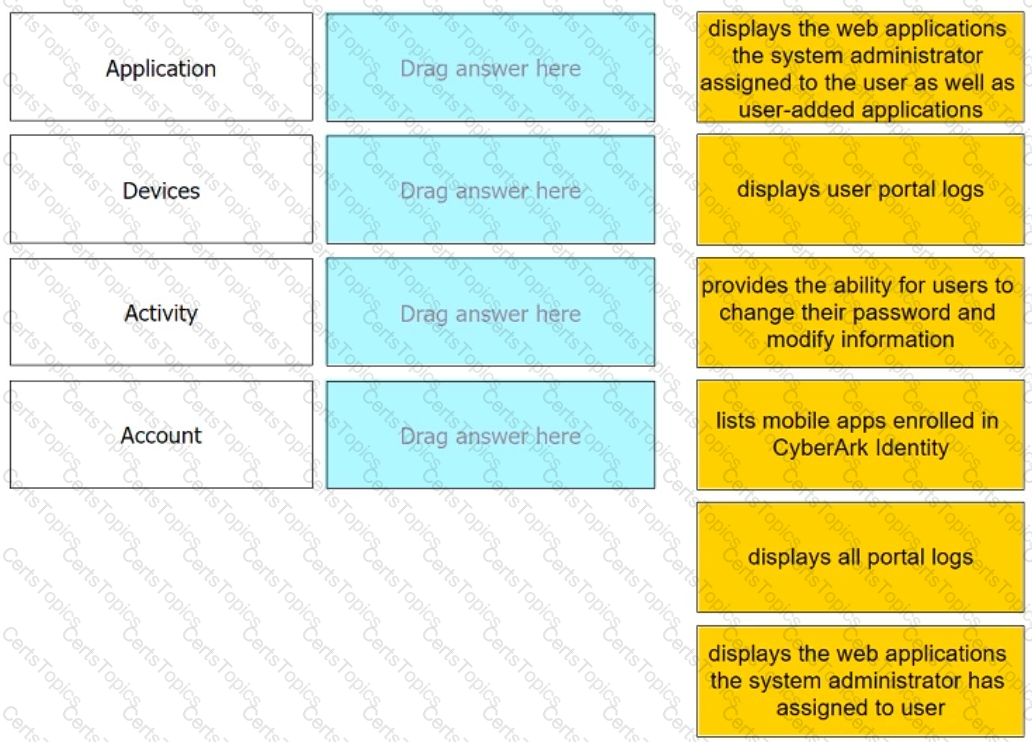
Match each User Portal tab to the correct description.
An organization previously allowed users to add their personal apps on the Identity User Portal. This will soon be disabled due to policy changes.
What is the impact to the users for personal apps previously added to the User Portal?
When a user enrolls a mobile device (iOS or Android) without enabling mobile device management, what happens? (Choose three.)
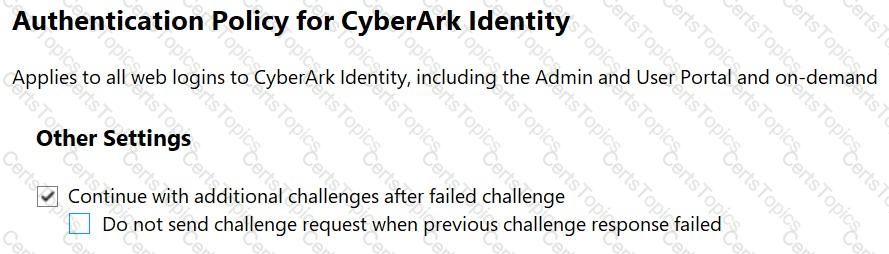
Refer to the exhibit.
Which statements are correct regarding this Authentication Policy? (Choose two.)
What is the most likely reason a CyberArk Identity admin would turn on the "Provisioning" feature within a Web App connector?
Your Chief Executive Officer lost his phone and cannot perform MFA to log in to work.
How can you enable him to bypass MFA right away and not delay his work?