CyberArk Related Exams
ACCESS-DEF Exam







Your team is deploying endpoint authentication onto the corporate endpoints within an organization. Enrollment details include when the enrollment must be completed, and the enrollment code was sent out to the users. Enrollment can be performed in the office or remotely (without the assistance of an IT support engineer). You received feedback that many users are unable to enroll into the system using the enrollment code.
What can you do to resolve this? (Choose two.)
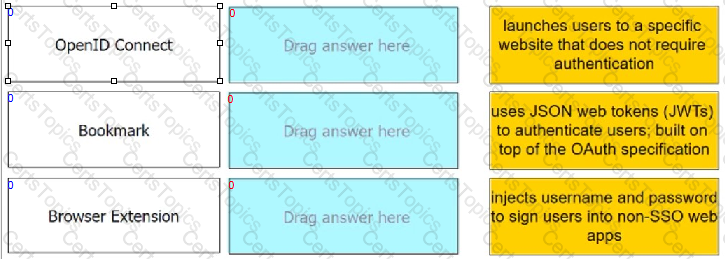
Match each Web App Connector to the phrase that best describes its service offering.
Within a Web App connector, which feature does an admin use to grant users access?