Huawei Related Exams
H12-725_V4.0 Exam







: 52 DRAG DROP
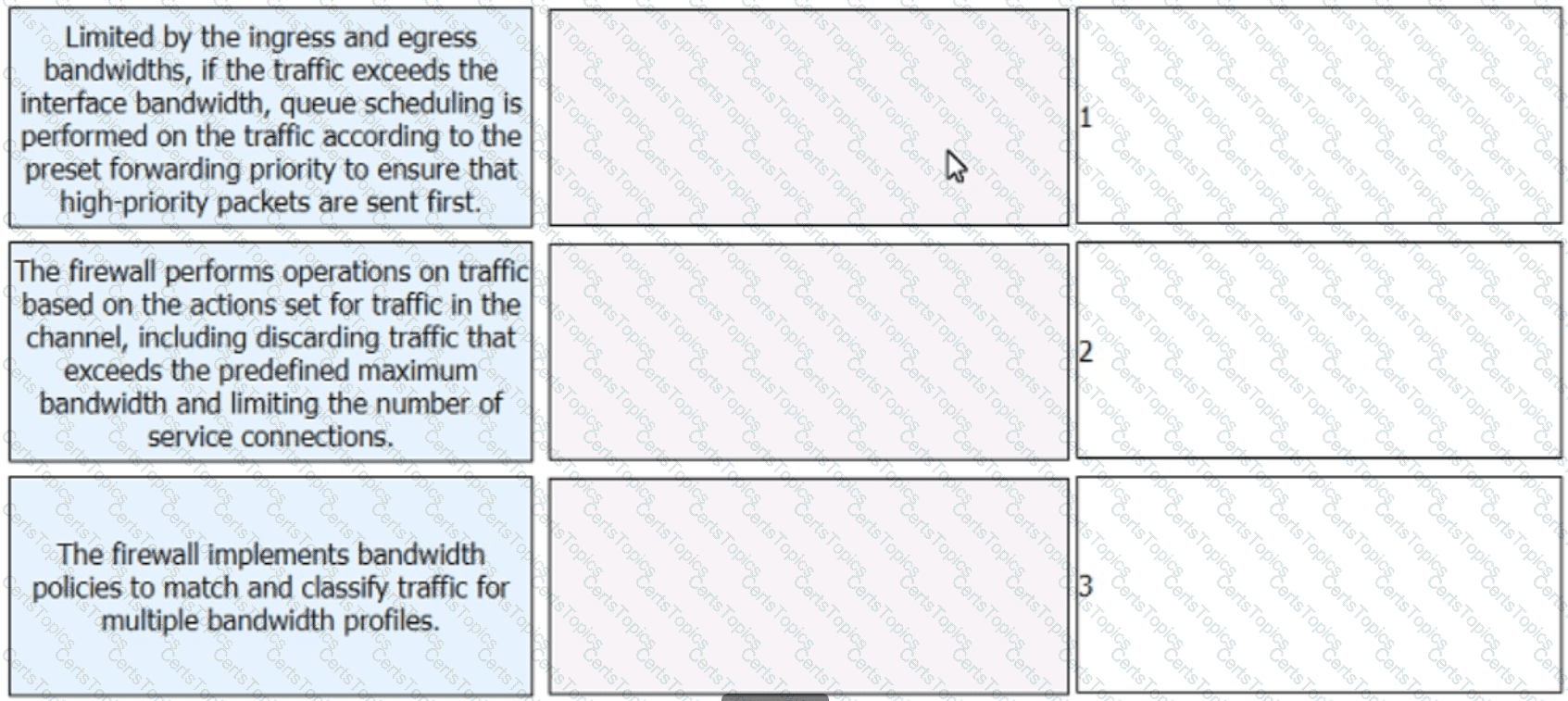
Arrange the steps of the bandwidth management process on firewalls in the correct sequence.
When an IPsec VPN is established in aggressive mode, AH+ESP can be used to encapsulate packets in NAT traversal scenarios.
During deployment of Portal authentication, an authentication-free rule profile needs to be configured to ensure Portal pages can be opened on authentication terminals. To achieve this purpose, the following traffic needs to be permitted in the authentication-free rule profile: DNS resolution traffic of user terminals, traffic from user terminals for accessing Portal pages, and traffic from user terminals to the RADIUS server.