Huawei Related Exams
H12-721 Exam







In the USG firewall, which two commands can be used to view the running status and memory/CPU usage of the device components (main control board, board, fan, power supply, etc.)?
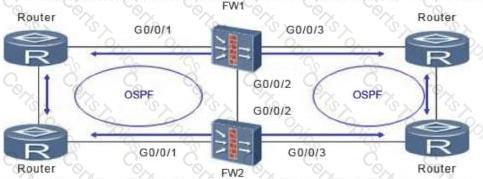
As shown in the figure, the firewall is dual-system hot standby. In this networking environment, all service interfaces of the firewall work in routing mode, and OSPF is configured on the upper and lower routers. Assume that the convergence time of OSPF is 30s after the fault is rectified. What is the best configuration for HRP preemption management?