Cisco Related Exams
300-745 Exam







Which financial reporting regulatory framework must a publicly traded company doing business in the US comply with?
The network security team of a private university is conducting a comprehensive audit to evaluate the security posture across the network infrastructure. During the review, the security team found that a trusted vendor disclosed serious vulnerabilities identified in a product that plays a crucial role in the university’s CI/CD pipeline. The security team must act promptly to mitigate the potential risks posed by these vulnerabilities. Which action must the security team take first in response to the disclosure?
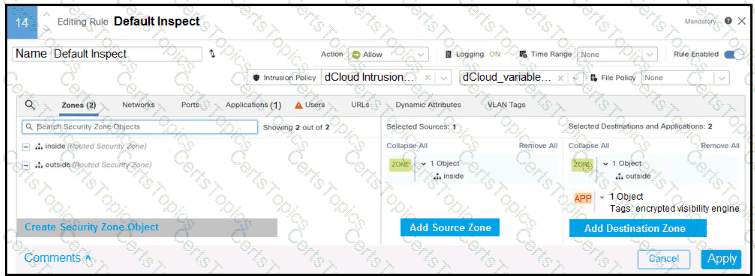
Refer to the exhibit.
In addition to SSL decryption, which firewall feature allows malware to be blocked?