A company’s IDS has identified outbound traffic from one of the web servers coming over port 389 to an outside address. This server only hosts websites. The company’s SOC administrator has asked a technician to harden this server. Which of the following would be the BEST way to complete this request?
Which of the following technologies would allow an administrator to build a software RAID on a Windows server?
Which of the following, if properly configured, would prevent a user from installing an OS on a server? (Select TWO).
Which of the following can be used to map a network drive to a user profile?
A server administrator has noticed that the storage utilization on a file server is growing faster than planned. The administrator wants to ensure that, in the future, there is a more direct relationship between the number of users using the server and the amount of space that might be used. Which of the following would BEST enable this correlation?
A server administrator is configuring the IP address on a newly provisioned server in the testing environment. The network VLANs are configured as follows:
The administrator configures the IP address for the new server as follows:
IP address: 192.168.1.1/24
Default gateway: 192.168.10.1
A ping sent to the default gateway is not successful. Which of the following IP address/default gateway combinations should the administrator have used for the new server?
An administrator is troubleshooting a RAID issue in a failed server. The server reported a drive failure, and then it crashed and would no longer boot. There are two arrays on the failed server: a two-drive RAIO 0 set tor the OS, and an eight-drive RAID 10 set for data. Which of the following failure scenarios MOST likely occurred?
Which of the following techniques can be configured on a server for network redundancy?
A server technician is configuring the IP address on a newly installed server. The documented configuration specifies using an IP address of 10.20.10.15 and a default gateway of 10.20.10.254. Which of the following subnet masks would be appropriate for this setup?
A storage administrator is investigating an issue with a failed hard drive. A technician replaced the drive in the storage array; however, there is still an issue with the logical volume. Which of the following best describes the NEXT step that should be completed to restore the volume?
A datacenter technician is attempting to troubleshoot a server that keeps crashing. The server runs normally for approximately five minutes, but then it crashes. After restoring the server to operation, the same cycle repeats. The technician confirms none of the configurations have changed, and the load on the server is steady from power-on until the crash. Which of the following will MOST likely resolve the issue?
A company uses a hot-site, disaster-recovery model. Which of the following types of data replication is required?
A server technician has been asked to upload a few files from the internal web server to the internal FTP server. The technician logs in to the web server using PuTTY, but the connection to the FTP server fails. However, the FTP connection from the technician’s workstation is suсcessful. To troubleshoot the issue, the technician executes the following command on both the web server and the workstation:
ping ftp.acme.local
The IP address in the command output is different on each machine. Which of the following is the MOST likely reason for the connection failure?
Which of the following is an example of load balancing?
Which of the following is the MOST appropriate scripting language to use for a logon script for a Linux box?
Which of the following will correctly map a script to a home directory for a user based on username?
A server administrator is experiencing difficulty configuring MySQL on a Linux server. The administrator issues the getenforce command and receives the following output:
># Enforcing
Which of the following commands should the administrator issue to configure MySQL successfully?
A server administrator is completing an OS installation for a new server. The administrator patches the server with the latest vendor-suggested software, configures DHCP, and verifies all network cables are properly connected in the IDF, but there is no network connectivity. Which of the following is the MOST likely reason for the lack of connectivity?
A company deploys antivirus, anti-malware, and firewalls that can be assumed to be functioning properly. Which of the following is the MOST likely system vulnerability?
Which of the following BEST describes the concept of right to downgrade?
Users have noticed a server is performing below Baseline expectations. While diagnosing me server, an administrator discovers disk drive performance has degraded. The administrator checks the diagnostics on the RAID controller and sees the battery on me controller has gone bad. Which of the following is causing the poor performance on the RAID array?
A company stores extremely sensitive data on an alt-gapped system. Which of the following can Be Implemented to increase security against a potential insider threat?
Which of the following server types would benefit MOST from the use of a load balancer?
Due to a recent application migration, a company’s current storage solution does not meet the necessary requirements tor hosting data without impacting performance when the data is accessed in real time by multiple users. Which of the following is the BEST solution for this Issue?
A server administrator is installing a new server that uses 40G0 network connectivity. The administrator needs to find the proper cables to connect the server to the switch. Which of the following connectors should the administrator use?
A datacenter in a remote location lost power. The power has since been restored, but one ol the servers has not come back online. After some investigation, the server is found to still be powered off. Which of the following is the BEST method to power on the server remotely?
A technician needs to set up a server backup method for some systems. The company’s management team wants to have quick restores but minimize the amount of backup media required. Which of the following are
the BEST backup methods to use to support the management’s priorities? (Choose two.)
A server administrator is installing an OS on a new server. Company policy states no one is to log in directly to the server. Which of the following Installation methods is BEST suited to meet the company policy?
Which of the following open ports should be closed to secure the server properly? (Choose two.)
A technician is laying out a filesystem on a new Linux server. Which of the following tools would work BEST to allow the technician to increase a partition's size in the future without reformatting it?
A server administrator is exporting Windows system files before patching and saving them to the following location:
\\server1\ITDept\
Which of the following is a storage protocol that the administrator is MOST likely using to save this data?
A technician is unable to access a server’s package repository internally or externally. Which of the following are the MOST likely reasons? (Choose two.)
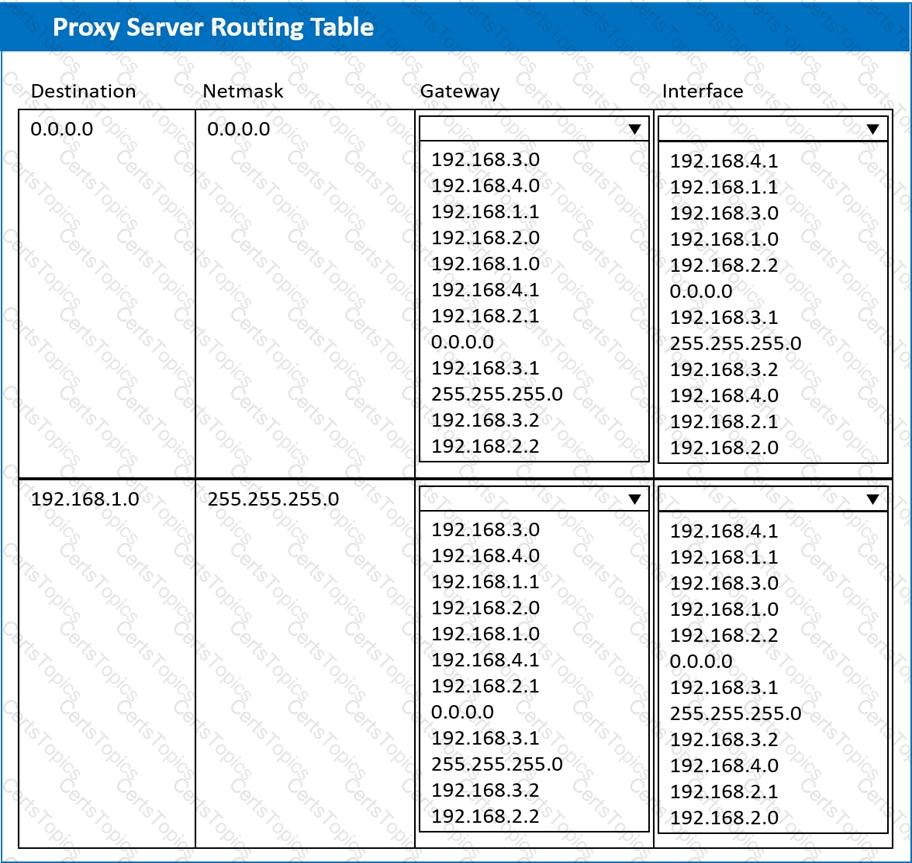
A systems administrator deployed a new web proxy server onto the network. The proxy server has two interfaces: the first is connected to an internal corporate firewall, and the second is connected to an internet-facing firewall. Many users at the company are reporting they are unable to access the Internet since the new proxy was introduced. Analyze the network diagram and the proxy server’s host routing table to resolve the Internet connectivity issues.
INSTRUCTIONS
Perform the following steps:
1. Click on the proxy server to display its routing table.
2. Modify the appropriate route entries to resolve the Internet connectivity issue.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Which of the following relates to how much data loss a company agrees to tolerate in the event of a disaster?
A technician recently upgraded several pieces of firmware on a server. Ever since the technician rebooted the server, it no longer communicates with the network. Which of the following should the technician do FIRST to return the server to service as soon as possible?
Which of the following should an administrator use to transfer log files from a Linux server to a Windows workstation?
A technician is attempting to update a server’s firmware. After inserting the media for the firmware and restarting the server, the machine starts normally into the OS. Which of the following should the technician do
NEXT to install the firmware?
Which of the following actions should a server administrator take once a new backup scheme has been configured?
A server technician has received reports of database update errors. The technician checks the server logs and determines the database is experiencing synchronization errors. To attempt to correct the errors, the technician should FIRST ensure:
A technician is working on a Linux server. The customer has reported that files in the home directory are missing. The /etc/ f stab file has the following entry:
nfsserver:/home /home nfs defaults 0 0
However, a df -h /home command returns the following information:
/dev/sda2 10G 1G 9G 10% /home
Which of the following should the technician attempt FIRST to resolve the issue?
Winch of the following is a type of replication in which all files are replicated, all the time?
Which of the following BEST measures now much downtime an organization can tolerate Curing an unplanned outage?
Which of the following tools will analyze network logs in real time to report on suspicious log events?
Which of the following would MOST likely be part of the user authentication process when implementing SAML across multiple applications?
Which of the following would a systems administrator implement to ensure all web traffic is secure?
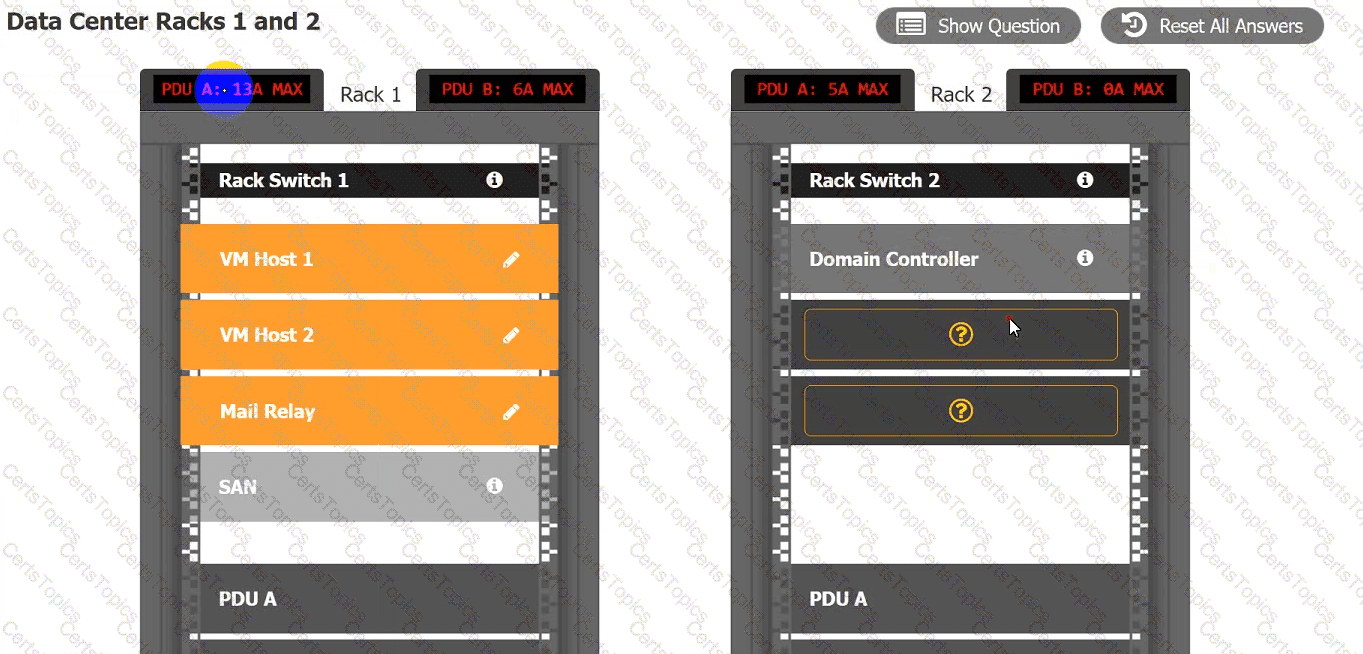
A recent power Outage caused email services to go down. A sever administrator also received alerts from the datacenter’s UPS.
After some investigation, the server administrator learned that each POU was rated at a maximum Of 12A.
INSTRUCTIONS
Ensure power redundancy is implemented throughout each rack and UPS alarms are resolved. Ensure the maximum potential PDU consumption does not exceed 80% or 9.6A).
a. PDU selections must be changed using the pencil icon.
b. VM Hosts 1 and 2 and Mail Relay can be moved between racks.
c. Certain devices contain additional details
Which of the following are measures that should be taken when a data breach occurs? (Select TWO).
A user cannot save large files to a directory on a Linux server that was accepting smaller files a few minutes ago. Which of the following commands should a technician use to identify the issue?
A security analyst suspects a remote server is running vulnerable network applications. The analyst does not have administrative credentials for the server. Which of the following would MOST likely help the analyst determine if the applications are running?
A server administrator is gathering business requirements to determine how frequently backups need to be performed on an application server. Which of the following is the administrator attempting to establish?
A server administrator needs to implement load balancing without purchasing any new hardware or implementing any new software. Which of the following will the administrator most likely implement?
A technician is attempting to resolve an issue with a file server that is unable to download a file Given the following output:
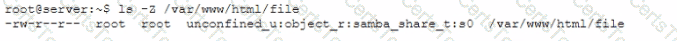
Which of the following would best allow this file to be read?
A server administrator created a new script and included the path to the script binary as the first line of the script. Which of the following scripting languages did the administrator most likely use?
A server administrator set up a monitoring application on various servers to keep track of CPU usage, memory consumption, and disk space utilization. Which of the following should be configured on the application so it can send email alerts about a specific issue?
An administrator has deployed a new virtual server from a template. After confirming access to the subnet's gateway, the administrator is unable to log on with the domain credentials. Which of the following is the most likely cause of the issue?
Which of the following actions should the server administrator perform on the server?
A technician set up a new multifunction printer. After adding the printer to the print server, the technician configured the printer on each user's machine. Several days later, users reported that they were no longer able to print, but scanning to email worked. Which of the following is most likely causing this issue?
Which of the following security risks provides unauthorized access to an application?
A technician is configuring a new server with four disks for the development team. The requirements are disk redundancy and maximum usable disk capacity. Which of the following RAID levels should be used for this server?
A datacenter has ten 40U racks in a hot/cold aisle configuration. The room has adequate air conditioning, but servers located near the top of the racks are shutting down due to issues with heat. Which of the following should be used to reduce issues with heat?
A technician is investigating a server's configuration to secure it from physical threats. The technician checks the BIOS and sees the following boot order:
USB Drive CDROM Drive Network Adapter RAID Controller
Additionally, the server's host OS is stored on mirrored drives. Which of the following should the technician do to secure the server?
Which of the following will protect critical data during a natural disaster?
A server administrator is currently working on an incident. Which of the following steps should the administrator perform before resolving the issue?
The management team has requested that new software licenses be purchased out of the capital budget as one-time, non-renewing expenses this year. Which of the following types of software licenses would most likely be used to meet this request?
A systems administrator is performing a routine update to a server. The administrator applies the update, restarts the server, and then conducts routine testing that reveals the critical functionality provided by the server is unavailable. Event logs indicate a core service is failing to start. The service is configured to start automatically, and rolling back the update does not correct the issue. Which of the following is most likely causing the service failure?
A server administrator is setting up a disk with enforcement policies on how much data each home share can hold. The amount of data that is redundant on the
server must also be minimized. Which of the following should the administrator perform on the server? (Select two).
An administrator is unable to get server updates from a WSUS server. However, the administrator was able to patch the server successfully last month. Which of the following should the administrator check first?
Which of the following would a systems administrator most likely implement to encrypt data in transit for remote administration?
A technician is tasked with upgrading 24 hosts simultaneously with a Type 1 hypervisor. Which of the following protocols should the technician use for this upgrade?
Under which of the following should a technician implement scripting?
Which of the following types of physical security controls would most likely be a target of a social engineering attack?
An administrator connects a server to an external gigabit switch, but the server can only get a speed of 100Mbps. Which of the following is the most likely cause of this issue?
A server administrator is tasked with upgrading the network on a server to 40Gbps. After installing the card, which of the following connectors should the administrator use?
An IT administrator is configuring ten new desktops without an operating system. The infrastructure contains an imaging server and operating system loaded on a USB, a DVD, and an SD card. Which of the following options
would minimize the amount of time the administrator needs to load the operating system on every machine?
A server administrator deployed a new product that uses a non-standard port for web access on port 8443. However, users are unable to access the new
application. The server administrator checks firewall rules and determines 8443 is allowed. Which of the following is most likely the cause of the issue?
An administrator has been asked to copy files from a Windows server that may not conform to Windows file-naming standards. Which of the following would best facilitate the copy process?
A Windows server has experienced a BSOD, and the administrator needs to monitor thereboot. The server is in a datacenter with no OOB management. Which of the following tools should the administrator use to complete this task?
A remote, embedded loT server is having a Linux OS upgrade installed. Which of the following is the best method to stage the new media for the default boot device of the server?
A server administrator notices drive C on a critical server does not have any available space, but plenty of unallocated space is left on the disk. Which of the following should the administrator perform to address the availability issue while minimizing downtime?
A site is considered a warm site when it:
has basic technical facilities connected to it.
has faulty air conditioning that is awaiting service.
is almost ready to take over all operations from the primary site.
Which of the following documents would explain the consequences of server downtime?
A server administrator is reviewing the following specifications:
VM01 Host:
CPU: 2 Physical, 4 Cores
RAM: 16GB
Storage: 16TB
Server 1 on VM01:
CPU: 1 virtual socket, 1 core per socket
RAM: 4GB
Storage: 8TB
Server 2 on VM01:
CPU: 2 virtual sockets, 2 cores per socket
RAM: 8GB
Storage: 10TB
Which of the following is described given these specifications?
Which of the following should be created to understand how long data is stored and how frequently data backups should be scheduled?
A systems administrator notices that a SAN is running out of space. There is no additional funding in the budget to upgrade the storage space. Which of the following will significantly reduce the storage space with the least effort? (Select two).
An administrator is working locally in a data center with multiple server racks. Which of the following is the best low-cost option to connect to any server while on site?
Which of the following types of asset management documentation is commonly used as a reference when processing the replacement of a faulty server component?
A systems administrator notices the fans are running at full speed in a newly upgraded server. Which of the following should be done to address this issue?
Which of the following backup types is used to capture all data regardless of any changes from the previous backup jobs?
A user is unable to access the database server from a workstation. All other workstations are able to access the database server. The technician issues the following command to check the workstation:
userGhost:!# nmap localhost
Nmap scan report for localhost (127.0.0.1)
Host is up (0.001 ms latency).
Not shown: 1023 closed ports
PORT STATE SERVICE
3306 open mysql
Which of the following should the technician perform next to allow access?
An administrator is patching a file and print server After rebooting the server, it begins acting strangely. The administrator tries to open Print Management, but it will not open Upon inspection, the spooler service has been disabled. The administrator then notices the server has services that should be enabled but are disabled. Which of the following actions should the administrator take next to resolve the issue as quickly as possible?
The internal IT department policy for monitoring server health requires that evidence of server reboots be collected and reviewed on a regular basis. Which of the following should be monitored to best provide this evidence?
A server administrator is installing a new server on a manufacturing floor. Because the server is publicly accessible, security requires the server to undergo hardware hardening. Which of the following actions should the administrator take?
A server administrator is tasked with resolving an issue with the server's local storage. The administrator turns on the server and only two out of the four drives are found. After several reboots, an additional hard drive connects and disconnects randomly. Which of the following is most likely the cause?
A server administrator is installing a new server with multiple NICs on it. The Chief Information Officer has asked the administrator to ensure the new server will have the least amount of network downtime but a good amount of network speed. Which of the following best describes what the administrator should implement on the new server?
A server in the data center reportedly has a BSOD and is not responding. The server needs to be rebooted. Which of the following is the best method to reboot the server remotely?
A technician notices a server that contains four fans is now louder than normal even though the temperature in the room has not changed and the load on the server has not increased. Which of the following is most likely the cause of the noise?
Multiple users have reported an issue accessing files on a specific server. Which of the following should be the first step in troubleshooting this issue?
A startup company needs to set up an initial disaster recovery site. The site must be cost-effective and deployed quickly. Which of the following sites should the company set up?
A Linux server was recently updated. Now, the server stops during the boot process with a blank screen and an£s> prompt. When of the following is the MOST likely cause of this issue?
Which of the following BEST describes a warm site?
Which of the following cloud models is BEST described as running workloads on resources that are owned by the company and hosted in a company-owned data center, as well as on rented servers in another company's data center?
Which of the following is the MOST secure method to access servers located in remote branch offices?
A technician needs to install a Type 1 hypervisor on a server. The server has SD card slots, a SAS controller, and a SATA controller, and it is attached to a NAS. On which of the following drive types should the technician install the hypervisor?
Users are able to connect to the wireless network, but they are unable to access the internet. The network administrator verifies connectivity to all network devices, and there are no ISP outages. The server administrator removes the old address leases from the active leases pool, which allows users to access the internet. Which of the following is most likely causing the internet issue?
A technician noted the RAID hard drives were functional while troubleshooting a motherboard failure. The technician installed a spare motherboard with similar specifications and used the original components. Which of the following should the technician do to restore operations with minimal downtime?
Which of the following ensures a secondary network path is available if the primary connection fails?
Which of the following BEST measures how much downtime an organization can tolerate during an unplanned outage?
A VLAN needs to be configured within a virtual environment for a new VM. Which of the following will ensure the VM receives a correct IP address?
An administrator is investigating several unexpected documents and video files that recently appeared in a network share. The administrator checks the properties of the files and sees the author's name on the documents is not a company employee. The administrator questions the other users, but no one knows anything about the files. The administrator then checks the log files and discovers the FTP protocol was used to copy the files to the server. Which of the following needs to be done to prevent this from happening again?
A company needs to increase the security controls on its servers. An administrator is implementing MFA on all servers using cost effective techniques. Which of the following should the administrator use to satisfy the MFA requirement?
A technician is configuring a point-to-point heartbeat connection between two servers using IP addressing. Which of the following is the most efficient
subnet mask for this connection?
An administrator is able to ping the default gateway and internet sites by name from a file server. The file server is not able to ping the print server by name. The administrator is able to ping the file server from the print server by both IP address and computer name. When initiating an initiating from the file server for the print server, a different IP address is returned, which of the following is MOST Likely the cause?
The accounting department needs more storage and wants to retain the current data for quick read-write access. The accounting server does not have any internet drive bays available to keep both disks however the server does have USB 3 0 and eSATA ports available. Which of the following is the BEST way to accomplish the department's goals?
A server administrator is building a pair of new storage servers. The servers will replicate; therefore, no redundancy is required, but usable capacity
must be maximized. Which of the following RAID levels should the server administrator implement?
While running a local network security scan an administrator discovers communication between clients and one of the web servers is happening in cleartext. Company policy requires all communication lo be encrypted. Which of the following ports should be closed to stop the deartext communication?
Which of the following often-overlooked parts of the asset life cycle can cause the greatest number of issues in relation to Pll exposure?
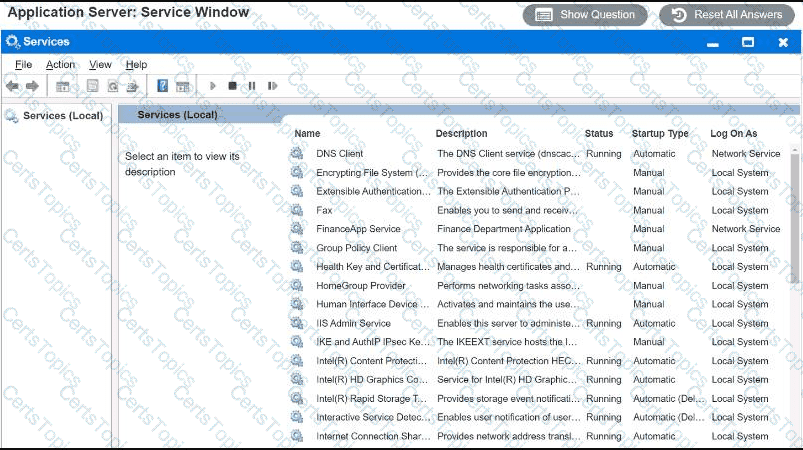
Users report that the FinanceApp software is not running, and they need immediate
access. Issues with the FinanceApp software occur every week after the IT team
completes server system updates. The users, however, do not want to contact the
help desk every time the issue occurs. The users also report the new MarketApp
software is not usable when it crashes, which can cause significant downtime. The
technician who restarted the MarketApp software noticed it is running under a test
account, which is a likely cause of the crashes.
INSTRUCTIONS
Using the Services menu provided, modify the appropriate application services to
remedy the stated issues.
An administrator needs to increase the size of an existing RAID 6 array that is running out of available space. Which of the following is the best way the administrator can perform this task?
A server administrator is creating a script that will move files only if they were created before a date input by the user. Which of the following constructs will allow the script to apply this test until all available files are assessed?
An administrator is researching the upcoming licensing software requirements for an application that usually requires very little technical support. Which of the following licensing models would be the LOWEST cost solution?
A backup application is copying only changed files each time it runs. During a restore, however, only a single file is used. Which of the following backup methods does this describe?
Which of the following backup types copies changed data from a server and then combines the backups on the backup target?
After the installation of an additional network card into a server, the server will not boot into the OS. A technician tests the network card in a different server with a different OS and verifies the card functions correctly. Which of the following should the technician do NEXT to troubleshoot this issue?
A server administrator is implementing an authentication policy that will require users to use a token during login. Which of the following types of authentication is the administrator implementing?
In which of the following media rotation schemes are daily, weekly, and monthly backup media utilized in a first-in, first-out method?
An administrator is troubleshooting a failed NIC in an application server. The server uses DHCP to get all IP configurations, and the server must use a
specific IP address. The administrator replaces the NIC, but then the server begins to receive a different and incorrect IP address. Which of the following will enable the server to get the proper IP address?
A server administrator wants to check the open ports on a server. Which of the following commands should the administrator use to complete the task?
A user has been unable to authenticate to the company's external, web-based database after clicking a link in an email that required the user to change the account password. Which of the following steps should the company take next?
The HIDS logs on a server indicate a significant number of unauthorized access attempts via USB devices at startup. Which of the following steps should a server administrator take to BEST secure the server without limiting functionality?
Which of the following environmental controls must be carefully researched so the control itself does not cause the destruction of the server equipment?
An administrate is helping to replicate a large amount of data between two Windows servers. The administrator is unsure how much data has already been transferred. Which of the following will BEST ensure all the data is copied consistently?
An administrator is alerted to a hardware failure in a mission-critical server. The alert states that two drives have failed. The administrator notes the drives are in different RAID 1 arrays, and both are hot-swappable. Which of the following steps will be the MOST efficient?
A hardware technician is installing 19 1U servers in a 42 the following unit sizes should be allocated per server?
A staff memberwho a monitoring a data center reports one rack is experiencing higher temperatures than the racks next to it, despite the hardware in each rack being the same. Which of the following actions would MOST likely remediate the heal issue?
An organization stores backup tapes of its servers at cold sites. The organization wants to ensure the tapes are properly maintained and usable during a DR scenario. Which of the following actions should the organization perform?
Users at a company are licensed to use an application that is restricted by the number of active sessions. Which of the following best describes this licensing model?
A systems administrator is setting up a server farm for a new company. The company has a public range of IP addresses and uses the addresses internally. Which of the following IP addresses best fits this scenario?
The management team at a healthcare organization is concerned about being able to access the dairy vital records if there is an IT disaster that causes both servers and the network lo be offline. Which of the following backup types can the organization use to mitigate this risk?
A junior administrator needs to configure a single RAID 5 volume out of four 200GB drives attached to the server using the maximum possible capacity. Upon completion, the server reports that all drives were used, and the approximate volume size is 400GB. Which of the following BEST describes the result of this configuration?
Which of the following backup types resets the archive bit each time it is run?
A technician re working on a Linux server and re trying to access another server over the network. The technician gets server notfoundmessage when trying to execute ping servername but no error messages when usingpingservername. Domain.com. Which ofthefollowing should the technician do to resolve the error?
A company's security team has noticed employees seem to be blocking the door in the main data center when they are working on equipment to avoid having to gain access each time. Which of the following should be implemented to force the employees to enter the data center properly?
A technician is decommissioning a server from a production environment. The technician removes the server from the rack but then decides to repurpose the system as a lab server instead of decommissioning it. Which of the following is the most appropriate NEXT step to recycle and reuse the system drives?
A technician is troubleshooting a server issue. The technician has determined several possible causes of the issue and has identified various solutions. Which of the following should the technician do next?
An administrator is working on improving the security of a new domain controller. A report indicates several open ports on the server. Which of the following ports should the administrator disable?
An administrator has been asked to verify that all traffic egressing from a company is secured. The administrator confirms all the information that is sent over the network is encrypted. Which of the following describes the type of traffic being encrypted?
A technician is setting up a small office that consists of five Windows 10 computers. The technician has been asked to use a simple IP configuration without manually adding any IP addresses. Which of the following will the technician MOST likely use for the IP address assignment?