(Which of the following is used to store product quantities in a table while ensuring the minimal amount of storage is consumed?)
Which of the following commands is part of DDL?
(An analyst in the United States configured a database server so it could be accessed remotely by users in Brazil and Canada. Users in Brazil can connect to the server, but users in Canada cannot connect to the server. Which of the following is the reason for the issue?)
A DBA is reviewing the following logs to determine the current data backup plan for a primary data server:
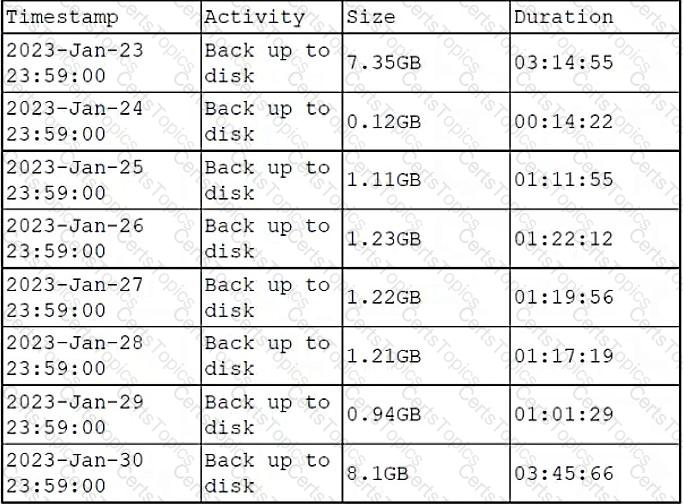
Which of the following best describes this backup plan?
Which of the following constraints is used to enforce referential integrity?
(A database administrator has configured a Resource Governor with three resource pools. The first resource pool is assigned a minimum CPU and memory value of 25%. The second resource pool is assigned a minimum CPU and memory value of 35%. The database administrator wants to assign the maximum CPU and the maximum resource pool to the third resource. Which of the following is the maximum the database administrator should assign to the third resource?)
A database's daily backup failed. Previous backups were completed successfully. Which of the following should the database administrator examine first to troubleshoot the issue?
(Which of the following would a database administrator monitor to gauge server health? Select two.)
Which of the following describes a scenario in which a database administrator would use a relational database rather than a non-relational database?
(Which of the following is used to store product quantities in a table while ensuring the minimal amount of storage is consumed?)
(A shared folder can only be accessed by authorized users. Which of the following policies was applied in this scenario?)
A business analyst is using a client table and an invoice table to create a database view that shows clients who have not made purchases yet. Which of the following joins is most appropriate for the analyst to use to create this database view?
Which of the following database structures is a type of NoSQL database?
Which of the following is recommended in order to provide encrypted data communication pathways for information as it is transmitted over a network?
(A healthcare company relies on contact forms and surveys on its website to properly communicate with patients. To which of the following attacks is the company’s data most vulnerable?)
(Five minutes after a power failure occurred in a data center, a CO₂ system was automatically triggered. Which of the following caused the CO₂ system to start?)
(A database manager would like to reduce the overhead caused by log-based recoveries. Which of the following should the manager use to best mitigate the situation?)
A database administrator is migrating the information in a legacy table to a newer table. Both tables contain the same columns, and some of the data may overlap.
Which of the following SQL commands should the administrator use to ensure that records from the two tables are not duplicated?
Which of the following is a characteristic of all non-relational databases?
Which of the following is an attack in which an attacker hopes to profit from locking the database software?
An on-premises application server connects to a database in the cloud. Which of the following must be considered to ensure data integrity during transmission?
Which of the following database instances are created by default when SQL Server is installed? (Choose two.)
Which of the following is a result of an on-path attack on a system?
(Which of the following are ORM tools? Select two.)
A database administrator needs to ensure continuous availability of a database in case the server fails. Which of the following should the administrator implement to ensure high availability of the database?
(Which of the following is a CPU-intensive operation that improves database performance and information retrieval?)
A new retail store employee needs to be able to authenticate to a database. Which of the following commands should a database administrator use for this task?
(Which of the following normal forms (NFs) is considered the most preferable for relational database design?)
(Before installing a new database instance for an organization, a DBA needs to verify the amount of space, the hardware, and the network resources. Which of the following best describes this process?)
A DBA left the company, and the DBA's account was removed from the system. Soon after, scheduled jobs began failing.
Which of the following would have most likely prevented this issue?
A database administrator is concerned about transactions in case the system fails. Which of the following properties addresses this concern?
Which of the following NFs is considered the most preferable for relational database design?
Which of the following can be used to protect physical database appliances from damage in a server room? (Choose two.)
Which of the following have data manipulation and procedural scripting power? (Choose two.)
A database administrator needs to aggregate data from multiple tables in a way that does not impact the original tables, and then provide this information to a department. Which of the following is the best way for the administrator to accomplish this task?