HOTSPOT
You have a Microsoft 365 E5 subscription that contains two users named User1 and User2.
You create the audit retention policies shown in the following table.
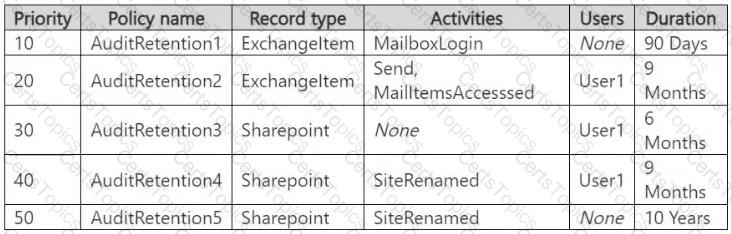
The users perform the following actions:
● User1 renames a Microsoft SharePoint Online site.
● User2 sends an email message.
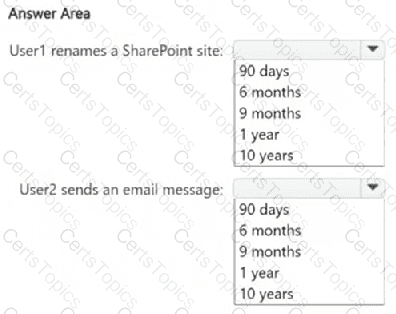
How long will the audit log records be retained for each action? To answer, select the appropriate options in the answer area.
NOTE : Each correct selection is worth one point.
You have a Microsoft 36515 subscription tha1 contains a Microsoft SharePoint Online site named Site1 Site1 contains three tiles named File1. File2 and File3.
You create the data loss prevention (DIP) policies shown in the following table.
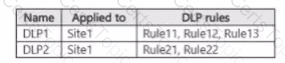
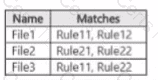
The DIP rule matches for each tile are shown in the following table.
How many DIP policy matches events will be added to Activity explorer, and how many policy matches will be added to the DLP incidents report? To answer, select the appropriate options m the answer area.

You have a Microsoft 365 E5 subscription that contains a Microsoft SharePoint Online site named Site1.
You need to deploy a Microsoft Purview insider risk management solution that will generate an alert when users share sensitive information on Site1 with external recipients.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct answer is worth one point.
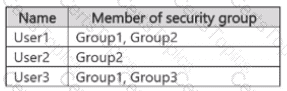
You have a Microsoft 365 E5 subscription that contains the users shown in the following table.
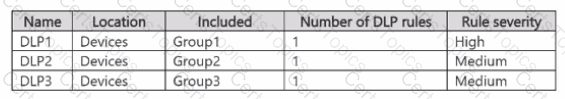
You have the data loss prevention (DLP) policies shown in the following table.
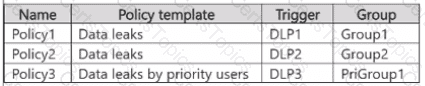
From Insider risk management, you configure a priority user group named PriGroup1 that contains User3 as a member. You have the insider risk policies shown in the following table.
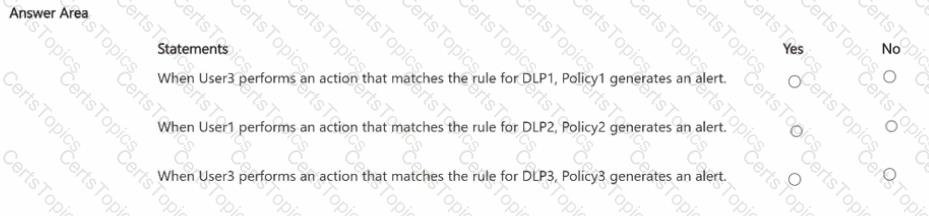
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.