Employees in a healthcare organization could not access their devices when they returned to work after the weekend. The security team discovered that a threat actor had encrypted the devices. Which security solution would mitigate the risk in future?
Refer to the exhibit.
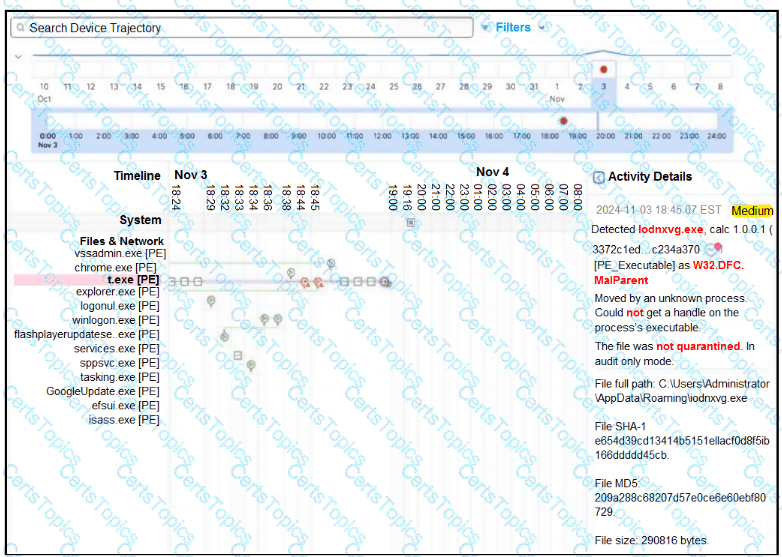
A retail company recently deployed a file inspection feature using secure endpoint. The file inspection must detect and prevent the execution of malicious files on machines. During testing, logs showed that certain malicious files are still being executed despite the presence of the security measure. To understand why the threats are not being blocked, it is essential to investigate the configuration of secure endpoint policies. Which configuration is allowing the files to execute?
An agricultural company wants to enhance the cybersecurity posture by implementing a defense-in-depth strategy to protect against polymorphic malware threats. Currently, the company’s security infrastructure relies solely on a stateful traditional edge firewall that does not provide adequate protection against malware variants. Which technology must be added to the company’s security architecture to achieve the goal?
Refer to the exhibit.
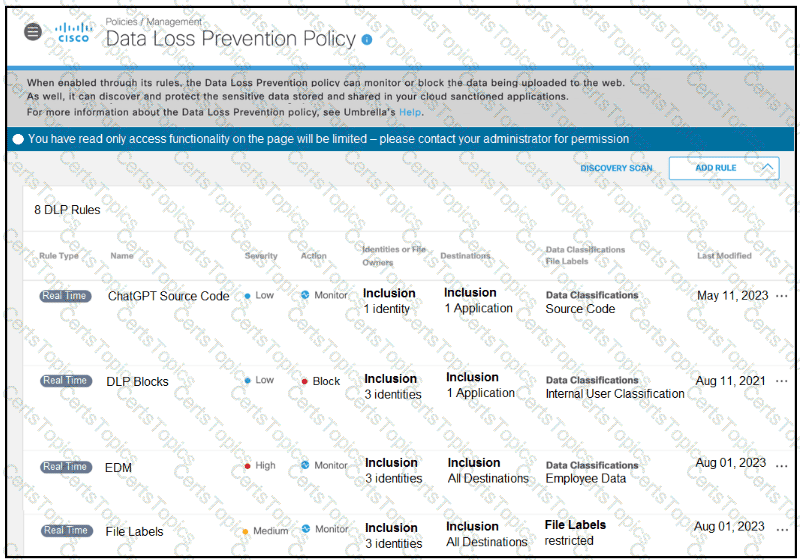
A software developer noticed that the application source code had been found on the internet. To avoid such an incident from happening again, the developer applied a DLP policy to prevent from uploading source code into generative AI tool like ChatGPT. When testing the policy, the developer noticed that it is still possible for the source code to be uploaded. Which action must the developer take to prevent this issue?