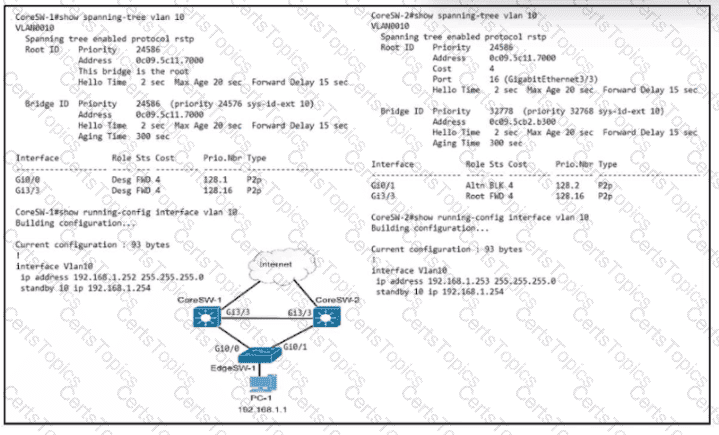
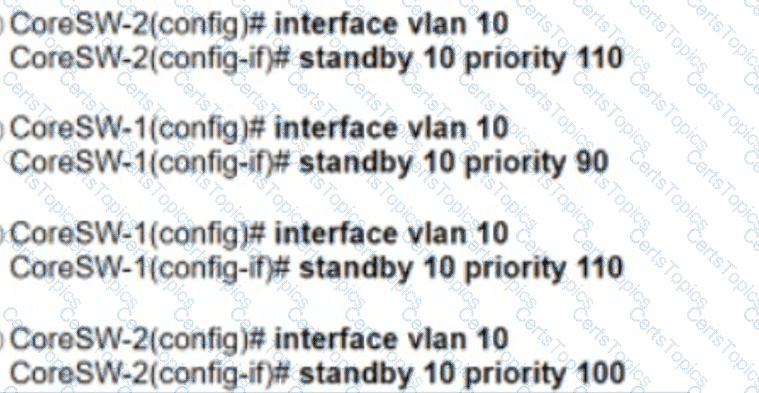
Refer to the exhibit. Which configuration causes the traffic from PC-1 to the internet to use the link between CoreSW-1 and CoreSW-2 when both switches are up?
Which A record type should be configured for access points to resolve the IP address of a wireless LAN controller using DNS?
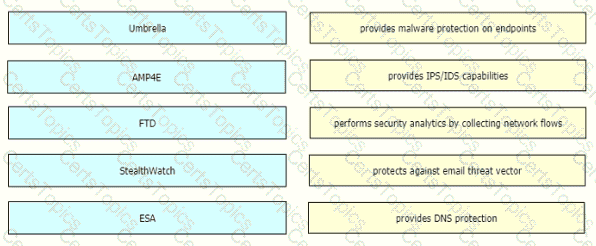
Drag and drop the threat defense solutions from the left onto their descriptions on the right.
Which new security enhancement is introduced by deploying a next-generation firewall at the data center in addition to the Internet edge?