CyberArk Related Exams
PAM-SEN Exam







You are designing the number of PVWAs a customer must deploy. The customer has three data centers with a distributed Vault in each, requires high availability, and wants to use all Vaults at all times.
How many PVWAs does the customer need?
After installing the first PSM server and before installing additional PSM servers, you must ensure the user performing the installation is not a direct owner of which safe?
-
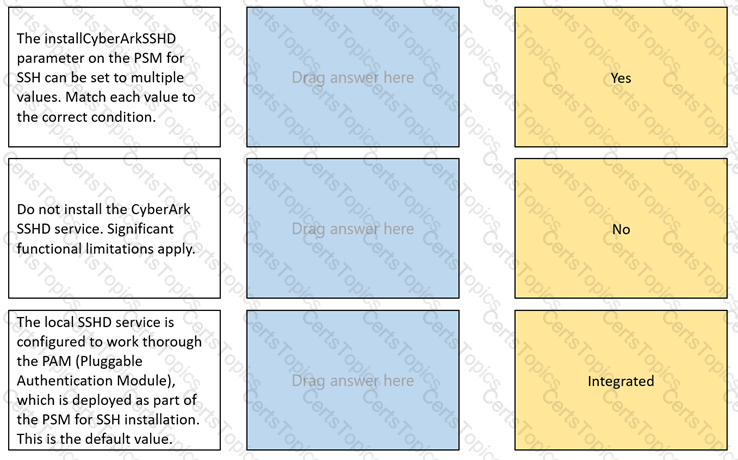
The installCyberArkSSHD parameter on the PSM for SSH can be set to multiple values.
Match each value to the correct condition.