Huawei Related Exams
H12-831_V1.0 Exam







I-SPF and PRC can speed up ISIS route convergence. PRC does not calculate nodes. Instead, it updates routes based on the shortest path tree (SPT) calculated using the SPF algorithm.
After port isolation is configured on a switch, hosts in the same VLAN cannot communicate with each other at Layer 2 or Layer 3 by default.
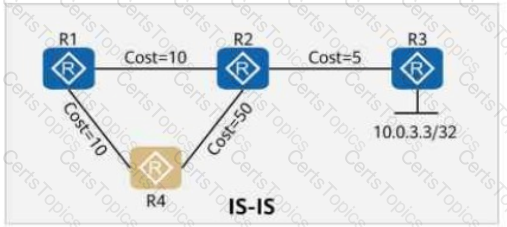
On the OSPF network shown in the figure, the cost values of links are marked. IS-IS Auto FRR is enabled on R1. The primary path from R1 to 10.0.3.3/32 is R1 → R2 → R3, and the backup path is R1 → R4 → R2 → R3.
Is this statement TRUE or FALSE?