A Logon Account can be specified in the Master Policy.
Which of the following are secure options for storing the contents of the Operator CD, while still allowing the contents to be accessible upon a planned Vault restart? (Choose three.)
Target account platforms can be restricted to accounts that are stored m specific Safes using the Allowed Safes property.
Which command generates a full backup of the Vault?
Where can a user with the appropriate permissions generate a report? (Choose two.)
A new HTML5 Gateway has been deployed in your organization.
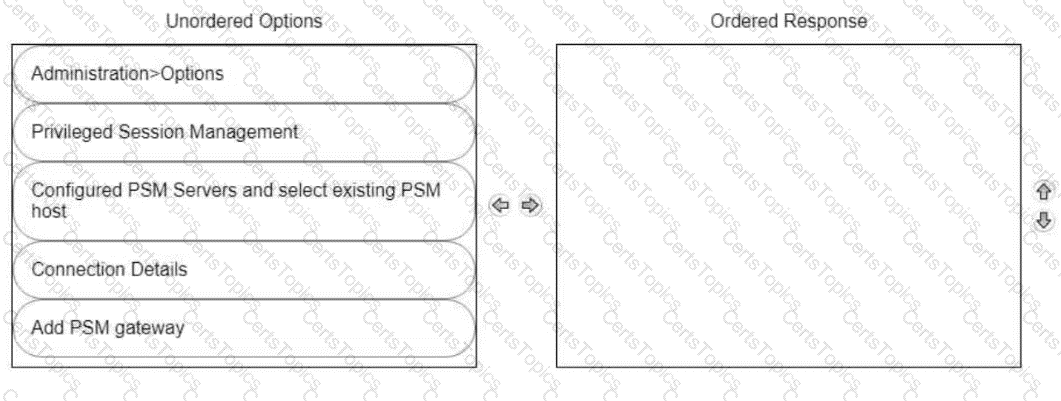
From the PVWA, arrange the steps to configure a PSM host to use the HTML5 Gateway in the correct sequence.
When onboarding multiple accounts from the Pending Accounts list, which associated setting must be the same across the selected accounts?
When are external vault users and groups synchronized by default?
CyberArk recommends implementing object level access control on all Safes.
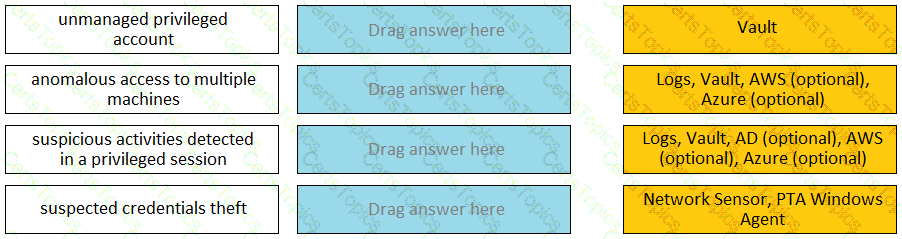
Match each PTA alert category with the PTA sensors that collect the data for it.
Which statement about the Master Policy best describes the differences between one-time password and exclusive access functionality?
Which Automatic Remediation is configurable for a PTA detection of a “Suspected Credential Theft”?
All of your Unix root passwords are stored in the safe UnixRoot. Dual control is enabled for some of the accounts in that safe. The members of the AD group UnixAdmins need to be able to use the show, copy, and connect buttons on those passwords at any time without confirmation. The members of the AD group Operations Staff need to be able to use the show, copy and connect buttons on those passwords on an emergency basis, but only with the approval of a member of Operations Managers never need to be able to use the show, copy or connect buttons themselves.
Which safe permission do you need to grant Operations Staff? Check all that apply.
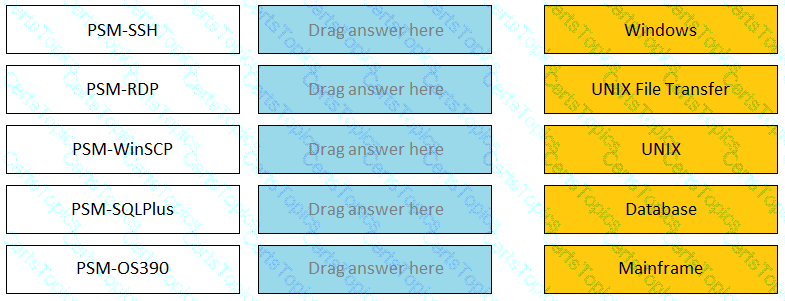
Match the connection component to the corresponding OS/Function.
Select the best practice for storing the Master CD.
As long as you are a member of the Vault Admins group you can grant any permission on any safe.
Within the Vault each password is encrypted by:
Due to corporate storage constraints, you have been asked to disable session monitoring and recording for 500 testing accounts used for your lab environment.
How do you accomplish this?
A user requested access to view a password secured by dual-control and is unsure who to contact to expedite the approval process. The Vault Admin has been asked to look at the account and identify who can approve their request.
What is the correct location to identify users or groups who can approve?
Which service should NOT be running on the DR Vault when the primary Production Vault is up?
An auditor needs to login to the PSM in order to live monitor an active session. Which user ID is used to establish the RDP connection to the PSM server?
Which Master Policy Setting must be active in order to have an account checked-out by one user for a pre-determined amount of time?
Which parameters can be used to harden the Credential Files (CredFiles) while using CreateCredFile Utility? (Choose three.)
Which master policy settings ensure non-repudiation?
By default, members of which built-in groups will be able to view and configure Automatic Remediation and Session Analysis and Response in the PVWA?
As long as you are a member of the Vault Admins group, you can grant any permission on any safe that you have access to.
When on-boarding account using Accounts Feed, Which of the following is true?
Which methods can you use to add a user directly to the Vault Admin Group? (Choose three.)
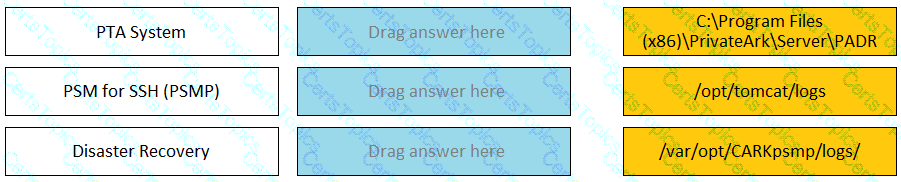
Match each component to its respective Log File location.
Users who have the 'Access Safe without confirmation' safe permission on a safe where accounts are configured for Dual control, still need to request approval to use the account.
In a default CyberArk installation, which group must a user be a member of to view the “reports” page in PVWA?
Where can you check that the LDAP binding is using TCP/636?
PSM captures a record of each command that was executed in Unix.
You created a new platform by duplicating the out-of-box Linux through the SSH platform.
Without any change, which Text Recorder Type(s) will the new platform support? (Choose two.)
When a DR Vault Server becomes an active vault, it will automatically fail back to the original state once the Primary Vault comes back online.
Which user(s) can access all passwords in the Vault?
You are onboarding 5,000 UNIX root accounts for rotation by the CPM. You discover that the CPM is unable to log in directly with the root account and will need to use a secondary account.
How should this be configured to allow for password management using least privilege?
Refer to the exhibit.
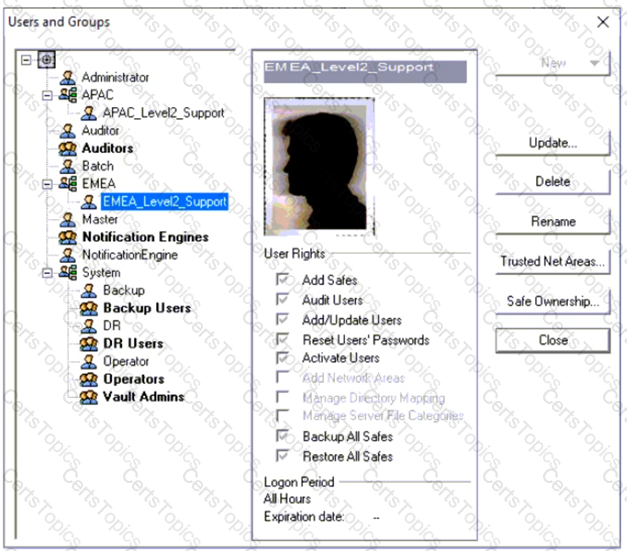
Why is user "EMEALevel2Support" unable to change the password for user "Operator"?
Secure Connect provides the following. Choose all that apply.
You need to enable the PSM for all platforms.
Where do you perform this task?
To ensure all sessions are being recorded, a CyberArk administrator goes to the master policy and makes configuration changes.
Which configuration is correct?
In PVWA, you are attempting to play a recording made of a session by user jsmith, but there is no option to “Fast Forward” within the video. It plays and only allows you to skip between commands instead. You are also unable to download the video.
What could be the cause?
You have been asked to turn off the time access restrictions for a safe.
Where is this setting found?
Match the log file name with the CyberArk Component that generates the log.

You received a notification from one of your CyberArk auditors that they are missing Vault level audit permissions. You confirmed that all auditors are missing the Audit Users Vault permission.
Where do you update this permission for all auditors?
The Active Directory User configured for Windows Discovery needs which permission(s) or membership?
You are logging into CyberArk as the Master user to recover an orphaned safe.
Which items are required to log in as Master?
To use PSM connections while in the PVWA, what are the minimum safe permissions a user or group will need?
What is the purpose of the HeadStartlnterval setting m a platform?
What must you specify when configuring a discovery scan for UNIX? (Choose two.)
You have been asked to turn off the time access restrictions for a safe.
Where is this setting found?
Due to network activity, ACME Corp’s PrivateArk Server became active on the OR Vault while the Primary Vault was also running normally. All the components continued to point to the Primary Vault.
Which steps should you perform to restore DR replication to normal?
You want to give a newly-created group rights to review security events under the Security pane. You also want to be able to update the status of these events.
Where must you update the group to allow this?
What is required to enable access over SSH to a Unix account through both PSM and PSMP?
It is possible to restrict the time of day, or day of week that a [b]verify[/b] process can occur
Which file must be edited on the Vault to configure it to send data to PTA?
It is possible to control the hours of the day during which a user may log into the vault.
The Vault administrator can change the Vault license by uploading the new license to the system Safe.
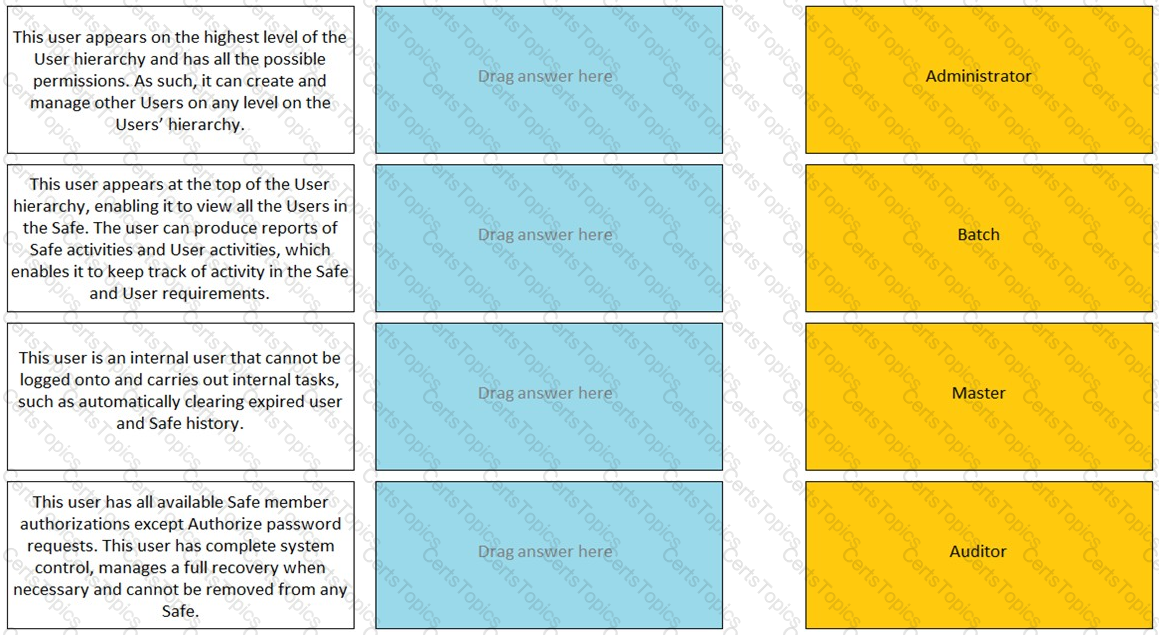
Match the built-in Vault User with the correct definition.
PTA can automatically suspend sessions if suspicious activities are detected in a privileged session, but only if the session is made via the CyberArk PSM.
You are configuring CyberArk to use HTML5 gateways exclusively for PSM connections.
In the PVWA, where do you set DefaultConnectionMethod to HTML5?
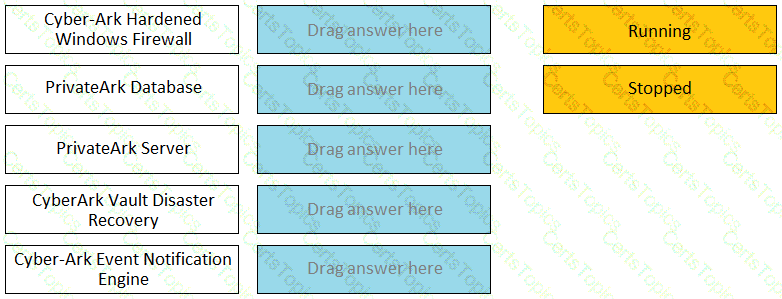
Match the Status of Service on a DR Vault to what is displayed when it is operating normally in Replication mode.
Vault admins must manually add the auditors group to newly created safes so auditors will have sufficient access to run reports.
Which Cyber Are components or products can be used to discover Windows Services or Scheduled Tasks that use privileged accounts? Select all that apply.
VAULT authorizations may be granted to_____.
What are the minimum permissions to add multiple accounts from a file when using PVWA bulk-upload? (Choose three.)
The Privileged Access Management solution provides an out-of-the-box target platform to manage SSH keys, called UNIX Via SSH Keys.
How are these keys managed?
What is the chief benefit of PSM?
A new colleague created a directory mapping between the Active Directory groups and the Vault.
Where can the newly Configured directory mapping be tested?
Users are unable to launch Web Type Connection components from the PSM server. Your manager asked you to open the case with CyberArk Support.
Which logs will help the CyberArk Support Team debug the issue? (Choose three.)
What are the mandatory fields when onboarding from Pending Accounts? (Choose two.)