A cloud developer needs to update a REST API endpoint to resolve a defect. When too many users attempt to call the API simultaneously, the following message is displayed:
Error: Request Timeout - Please Try Again Later
Which of the following concepts should the developer consider to resolve this error?
A cloud engineer wants to implement a monitoring solution to detect cryptojacking and other cryptomining malware on cloud instances. Which of the following metrics would most likely be used to identify the activity?
A newly configured VM fails to run application updates despite having internet access. The updates download automatically from a third-party network. Given the following output:
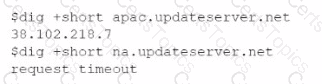
Which of the following troubleshooting steps would be best to take?
Once a change has been made to templates, which of the following commands should a cloud architect use next to deploy an laaS platform?
A list of CVEs was identified on a web server. The systems administrator decides to close the ports and disable weak TLS ciphers. Which of the following describes this vulnerability management stage?
Which of the following is used to detect signals and measure physical properties, such as the temperature of the human body?
A SaaS provider introduced new software functionality for customers as part of quarterly production enhancements. After an update is implemented, users cannot locate certain transactions from an inbound integration. During the investigation, the application owner finds the following error in the logs:
Error: REST API - Deprecated call is no longer supported in this release.
Which of the following is the best action for the application owner to take to resolve the issue?
A cloud engineer is receiving multiple alerts from the infrastructure monitoring agent. The alerts state that all the VMs in the public subnet are at 100% CPU utilization. However, when the engineer checks the network utilization of the VMs, the network throughput is at normal levels. Which of the following is the most likely cause of this issue?
Which of the following provides secure, private communication between cloud environments without provisioning additional hardware or appliances?
An IT manager is migrating the production environment to the cloud but needs to keep control of the operating systems, patches, and settings of all resources. Which of the following deployment models will best meet the requirements?
A cloud security analyst is looking for existing security vulnerabilities on software applications. Which of the following describes this vulnerability management phase?
An organization's critical data was exfiltrated from a computer system in a cyberattack. A cloud analyst wants to identify the root cause and is reviewing the following security logs of
a software web application:
"2021/12/18 09:33:12" "10. 34. 32.18" "104. 224. 123. 119" "POST / login.php?u=administrator&p=or%201%20=1"
"2021/12/18 09:33:13" "10.34. 32.18" "104. 224. 123.119" "POST /login. php?u=administrator&p=%27%0A"
"2021/12/18 09:33:14" "10. 34. 32.18" "104. 224. 123. 119" "POST /login. php?u=administrator&p=%26"
"2021/12/18 09:33:17" "10.34. 32.18" "104. 224. 123.119" "POST / login.php?u=administrator&p=%3B"
"2021/12/18 09:33:12" "10.34. 32. 18" "104. 224. 123. 119" "POST / login. php?u=admin&p=or%201%20=1"
"2021/12/18 09:33:19" "10.34.32.18" "104. 224. 123.119" "POST / login. php?u=admin&p=%27%0A"
"2021/12/18 09:33:21" "10. 34. 32.18" "104.224. 123.119" "POST / login. php?u=admin&p=%26"
"2021/12/18 09:33:23" "10. 34. 32.18" "104. 224. 123.119" "POST / login. php?u=admin&p=%3B"
Which of the following types of attacks occurred?
A systems engineer tries to mount an iSCSI LUN to a VM host in a data center, but the host does not discover any iSCSI targets. A sample of the switch configuration is shown in the following image:
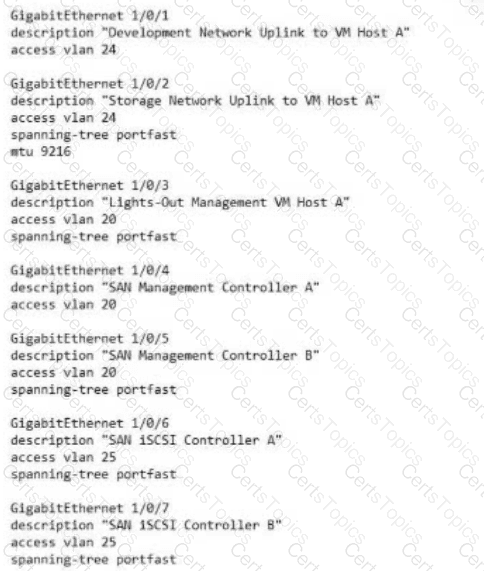
Which of the following configuration changes would most likely resolve the discovery issues?
A cloud engineer is reviewing the following Dockerfile to deploy a Python web application:
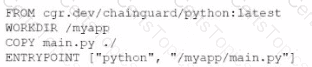
Which of the following changes should the engineer make lo the file to improve container security?
Which of the following is the most cost-effective and efficient strategy when migrating to the cloud?
A cloud engineer is exploring options to reduce the management overhead of the servers and network. Which of the following cloud service models should the engineer implement?
A cloud service provider just launched a new serverless service that is compliant with all security regulations. A company deployed its code using the service, and the company's application was hacked due to leaked credentials. Which of the following is responsible?
A software engineer at a cybersecurity company wants to access the cloud environment. Per company policy, the cloud environment should not be directly accessible via the internet. Which of the following options best describes how the software engineer can access the cloud resources?
A cloud engineer must find the root cause of a recent performance issue. Logs and metrics have been collected and are available. Which of the following is the best way to determine the source of the issue?
A developer is building a new application version using a CI/CD pipeline. The developer receives the following error message log when the build fails:
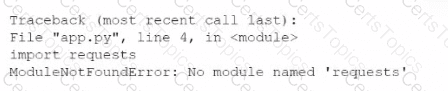
Which of the following is the most likely cause of this failure?
Which of the following cloud deployment strategies is best for an organization that wants to run open-source workloads with other organizations that are sharing the cost?
A cloud engineer hardened the WAF for a company that operates exclusively in North America. The engineer did not make changes to any ports, and all protected applications have
continued to function as expected. Which of the following configuration changes did the engineer most likely apply?
A developer is sending requests to a SaaS application. The developer becomes unable to send more requests after sending a number of them, but other developers can still send requests. Which of the following is most likely causing the issue?
Which of the following describes what CRUD is typically used for?
An engineer made a change to an application and needs to select a deployment strategy that meets the following requirements:
• Is simple and fast
• Can be performed on two Identical platforms
Which of the following strategies should the engineer use?
A cloud developer is creating a static website that customers will be accessing globally. Which of the following services will help reduce latency?
A company runs a discussion forum that caters to global users. The company's monitoring system reports that the home page suddenly is seeing elevated response times, even
though internal monitoring has reported no issues or changes. Which of the following is the most likely cause of this issue?
A security team recently hired multiple interns who all need the same level of access. Which of the following controls should the security team implement to provide access to the
cloud environment with the least amount of overhead?
A cloud engineer is concerned about command-and-control (C2) communication leaving a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify this type of communication?
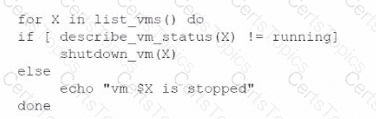
An administrator is creating a cron job that shuts down the virtual machines at night to save on costs. Which of the following is the best way to achieve this task?
A)
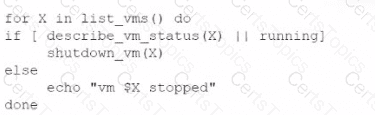
B)
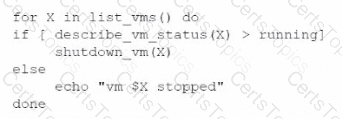
C)
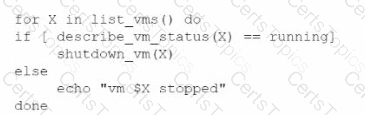
D)
A software development team must manage changes to source code for different clients who utilize the same product with different features. Which of the following meets this requirement?
Which of the following strategies requires the development of new code before an application can be successfully migrated to a cloud provider?
A company migrated its CRM system to a SaaS solution. The security team is updating the RAG matrix for the newly migrated CRM. Given the following table:
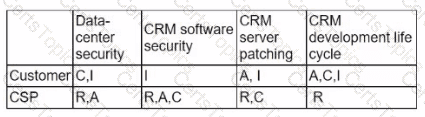
Which of the following responsibility assignments best aligns with the shared responsibility model for the new CRM?
A cloud engineer wants to implement a disaster recovery strategy that:
. Is cost-effective.
. Reduces the amount of data loss in case of a disaster.
. Enables recovery with the least amount of downtime.
Which of the following disaster recovery strategies best describes what the cloud engineer wants to achieve?
Which of the following will best reduce the cost of running workloads while maintaining the same performance? (Select two).
An organization has been using an old version of an Apache Log4j software component in its critical software application. Which of the following should the organization use to
calculate the severity of the risk from using this component?
A security analyst reviews the daily logs and notices the following suspicious activity:
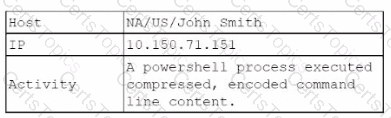
The analyst investigates the firewall logs and identities the following:
Which of the following steps should the security analyst take next to resolve this issue? (Select two).
A company's man web application is no longer accessible via the internet. The cloud administrator investigates and discovers the application is accessible locally and only via an IP access. Which of the following was misconfigured?
Department supervisors have requested a report that will help them understand the utilization of cloud resources, make decisions about budgeting for the following year, and reduce
costs. Which of the following are the most important requisite steps to create the report? (Select two).
A cloud server needs to automatically allocate more resources during sudden peak times. This allocation does not need to occur in regular intervals. Which of the following scaling
approaches should be used?
A cloud administrator shortens the amount of time a backup runs. An executive in the company requires a guarantee that the backups can be restored with no data loss. Which of th€ following backup features should the administrator lest for?
A company uses containers to implement a web application. The development team completed internal testing of a new feature and is ready to move the feature to the production
environment. Which of the following deployment models would best meet the company's needs while minimizing cost and targeting a specific subset of its users?
A company wants to implement a work environment that will have low operational overhead and highly accessible enterprise resource planning, email, and data resources. Which of
the following cloud service models should the company implement?
Which of the following types of storage is read-only and is accessed only when needed?
A company needs to deploy its own code directly in the cloud without provisioning additional infrastructure. Which of the following is the best cloud service model for the company to use?
A company's VMs that are created using the noncritical application tag are automatically shut down at 5:00 p.m. using a cronjob. Which of the following actions would allow a cloud engineer to stop all unresponsive instances with the least effort in case the automation fails?
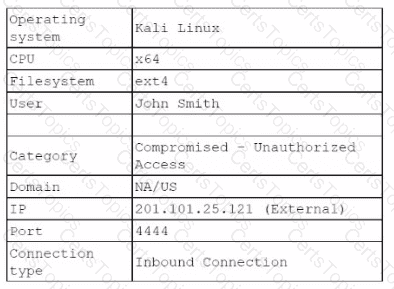
A cloud engineer is troubleshooting a connectivity issue. The application server with IP 192.168.1.10 in one subnet is not connecting to the MySQL database server with IP 192.168.2 20 in a different subnet. The cloud engineer reviews the following information:
Application Server Stateful Firewall
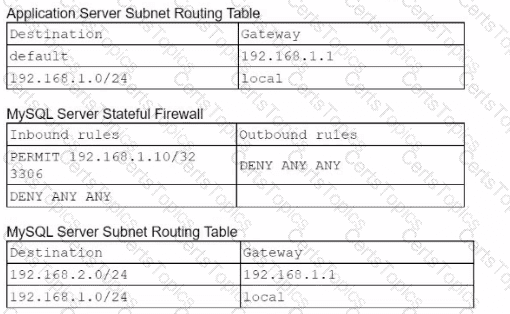
Which of the following should the cloud engineer address lo fix the communication issue?
A company has decided to adopt a microservices architecture for its applications that are deployed to the cloud. Which of the following is a major advantage of this type of architecture?
Which of the following best explains the concept of migrating from on premises to the cloud?
A software engineer is integrating an application lo The cloud that is web socket based. Which of the following applications is the engineer most likely deploying?
A cloud engineer wants containers to run the latest version of a container base image to reduce the number of vulnerabilities. The applications in use requite Python 3.10 and ate not compatible with any other version. The containers' images are created every time a new version is released from the source image. Given the container Dockerfile below:
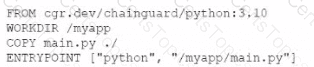
Which of the following actions will achieve the objectives with the least effort?
Which of the following would allow a cloud engineer to flatten a deeply nested JSON log to improve readability for analysts?
An organization is preparing for seasonal sales on its storefront web application. Which of the following approaches is best suited to meet this requirement with the minimal cost?
A systems administrator notices a surge of network traffic is coming from the monitoring server. The administrator discovers that large amounts of data are being downloaded to an external source. While investigating, the administrator reviews the following logs:
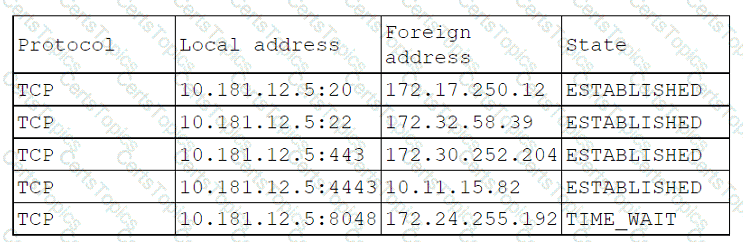
Which of the following ports has been compromised?
A web server hosted in a PaaS public cloud platform has been the target of DDoS attacks. A cloud engineer needs to protect the server from future volumetric DDoS attacks. Which of the following are the best actions for the engineer to take? (Select two.)
Users have been reporting that a remotely hosted application is not accessible following a recent migration. However, the cloud administrator is able to access the application from
the same site as the users. Which of the following should the administrator update?
A company wants to create a few additional VDIs so support vendors and contractors have a secure method to access the company's cloud environment. When a cloud
administrator attempts to create the additional instances in the new locations, the operation is successful in some locations but fails in others. Which of the following is the
most likely reason for this failure?
Which of the following interfaces is most commonly used for SSDs but not for HDDs?
A cloud solutions architect needs to have consistency between production, staging, and development environments. Which of the following options will best achieve this goal?
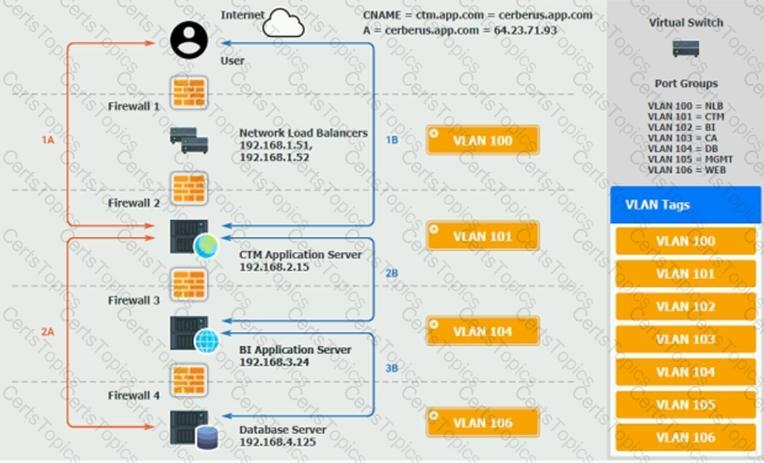
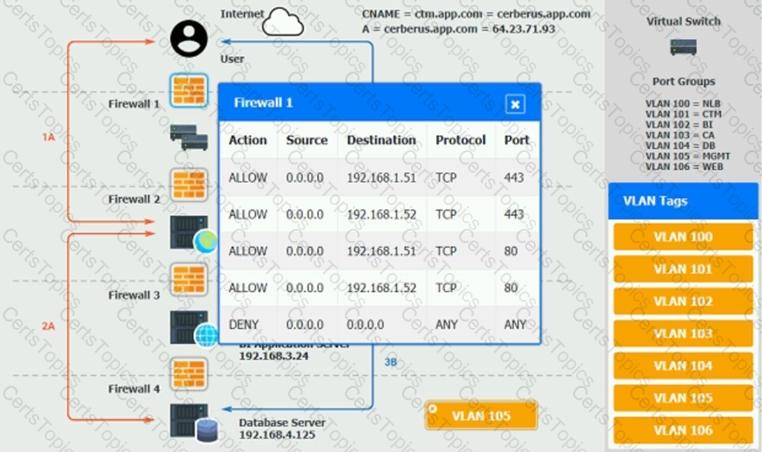
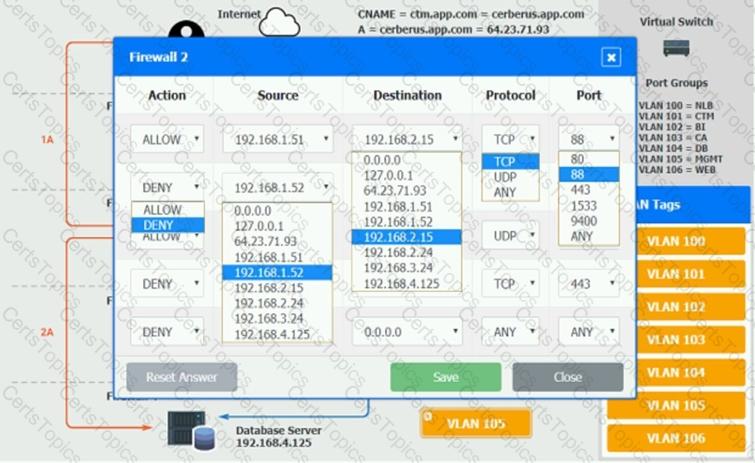
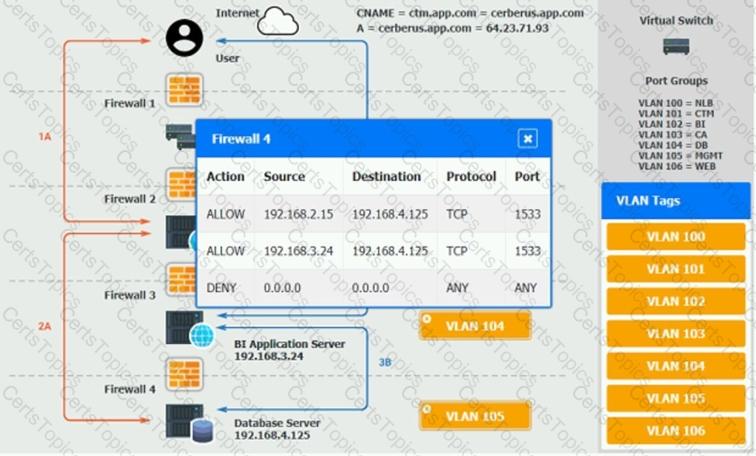
The QA team is testing a newly implemented clinical trial management (CTM) SaaS application that uses a business intelligence application for reporting. The UAT users were instructed to use HTTP and HTTPS.
Refer to the application dataflow:
1A – The end user accesses the application through a web browser to enter and view clinical data.
2A – The CTM application server reads/writes data to/from the database server.
1B – The end user accesses the application through a web browser to run reports on clinical data.
2B – The CTM application server makes a SOAP call on a non-privileged port to the BI application server.
3B – The BI application server gets the data from the database server and presents it to the CTM application server.
When UAT users try to access the application using or they get a message stating: “Browser cannot display the webpage.” The QA team has raised a ticket to troubleshoot the issue.
INSTRUCTIONS
You are a cloud engineer who is tasked with reviewing the firewall rules as well as virtual network settings.
You should ensure the firewall rules are allowing only the traffic based on the dataflow.
You have already verified the external DNS resolution and NAT are working.
Verify and appropriately configure the VLAN assignments and ACLs. Drag and drop the appropriate VLANs to each tier from the VLAN Tags table. Click on each Firewall to change ACLs as needed.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
An on-premises data center is located in an earthquake-prone location. The workload consists of real-time, online transaction processing. Which ot the following data protection strategies should be used to back up on-premises data to the cloud while also being cost effective?
Which of the following is the best type of database for storing different types of unstructured data that may change frequently?
A cloud engineer is developing an operating expense report that will be used to purchase various cloud billing models for virtual machine instances. The cloud billing model must meet the following requirements:
• The instance cannot be ephemeral.
• The minimum life cycle of the instance is expected to be five years.
• The software license is charged per physical CPU count.
Which of the following models would best meet these requirements?
A company uses containers stored in Docker Hub to deploy workloads (or its laaS infrastructure. The development team releases changes to the containers several times per hour. Which of the following should a cloud engineer do to prevent the proprietary code from being exposed to third parties?
For compliance purposes, a cloud developer at an insurance company needs to save all customer policies for more than ten years. Which of the following options is the most cost-
efficient tier to save the data in the cloud?
Which of the following migration types is best to use when migrating a highly available application, which is normally hosted on a local VM cluster, for usage with an external user population?
A cloud engineer is designing a high-performance computing cluster for proprietary software. The software requires low network latency and high throughput between cluster nodes.
Which of the following would have the greatest impact on latency and throughput when designing the HPC infrastructure?
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
A junior cloud administrator was recently promoted to cloud administrator and has been added to the cloud administrator group. The cloud administrator group is the only one that can access the engineering VM. The new administrator unsuccessfully attempts to access the engineering VM. However, the other administrators can access it without issue. Which of the following is the best way to identify the root cause?
A cloud engineer needs to deploy a new version of a web application to 100 servers. In the past, new version deployments have caused outages. Which of the following deployment types should the cloud engineer implement to prevent the outages from happening this time?
A customer relationship management application, which is hosted in a public cloud laaS network, is vulnerable to a remote command execution vulnerability. Which of the following is
the best solution for the security engineer to implement to prevent the application from being exploited by basic attacks?
Which of the following Al/ML technologies consumes text input to discern tone?
Which of the following is used to deliver code quickly and efficiently across the development, test, and production environments?
A company serves customers globally from its website hosted in North America. A cloud engineer recently deployed new instances of the website in the Europe region. Which of the
following is the most likely reason?
An DevOps engineer is receiving reports that users can no longer access the company's web application after hardening of a web server. The users are receiving the following error:
ERR_SSLJ/ERSION_OR_CIPHER_MISMATCH.
Which of the following actions should the engineer take to resolve the issue?